Authentication system and method based on peer-to-peer computing network
A computing network and authentication system technology, applied in the field of computing network authentication systems, can solve problems such as single point failure, and achieve the effect of improving resource utilization
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] Hereinafter, the present invention will be described in detail with reference to the drawings and examples. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other.
[0028] System embodiment
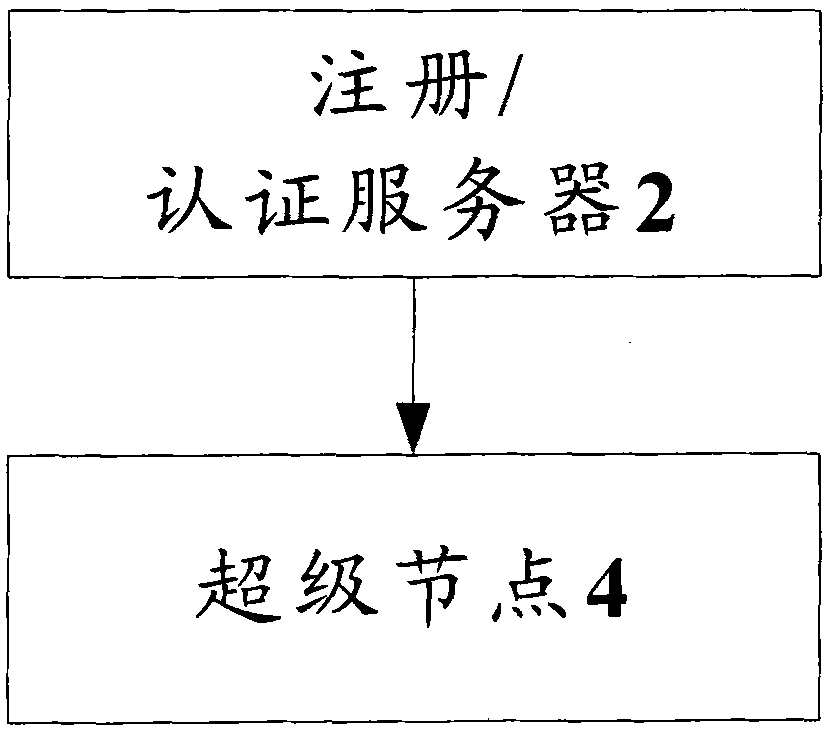
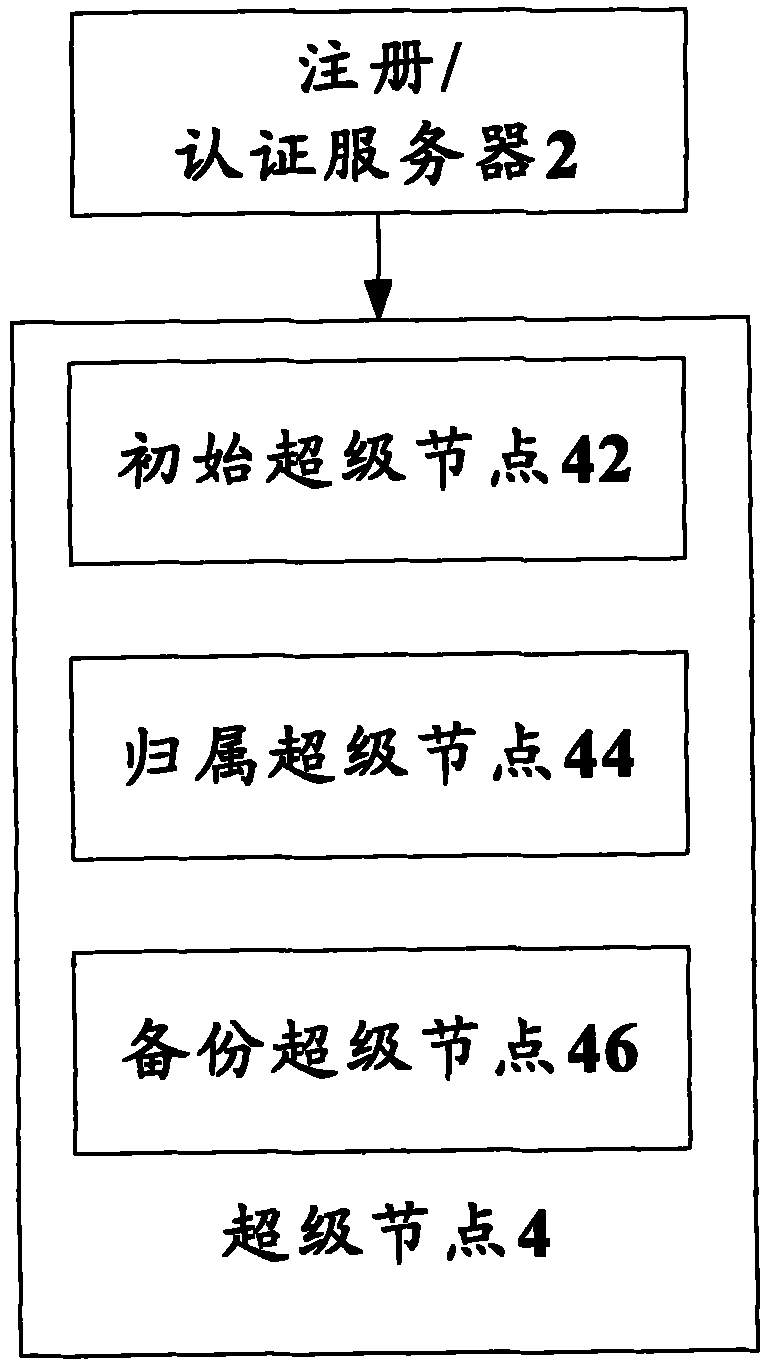
[0029] According to an embodiment of the present invention, an authentication system based on a peer-to-peer computing network is provided. figure 1 is a structural block diagram of an authentication system based on a peer-to-peer computing network according to an embodiment of the present invention, such as figure 1 As shown, the system includes: a super node 4, the structure of which is described below.
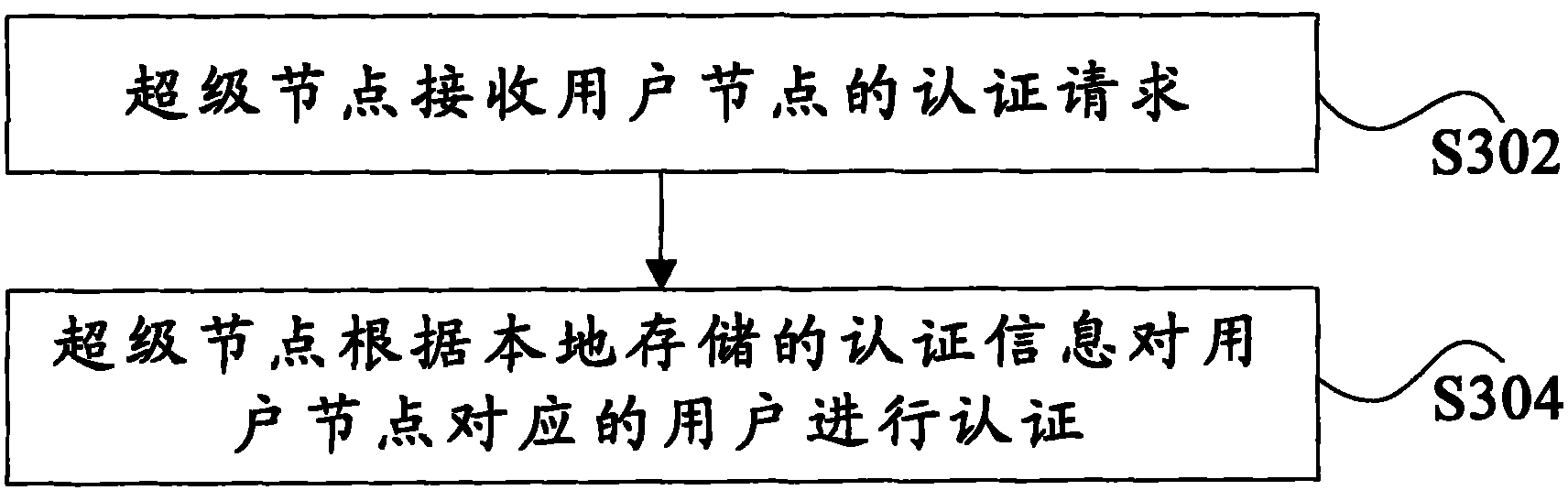
[0030] The super node 4 is configured to receive the authentication request from the user node, and authenticate the user corresponding to the user node according to the locally stored authentication information.
[0031] Preferably, the system also includes: a regist...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More