Two-factor online transaction safety authentication method and system
A security authentication, two-factor technology, applied in the field of security authentication, can solve the problem of low security of short messages
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] In order to make the above-mentioned purposes, features and advantages of the present invention more obvious and understandable, some preferred embodiments are specially cited below, and in conjunction with the accompanying drawings, the detailed description is as follows:
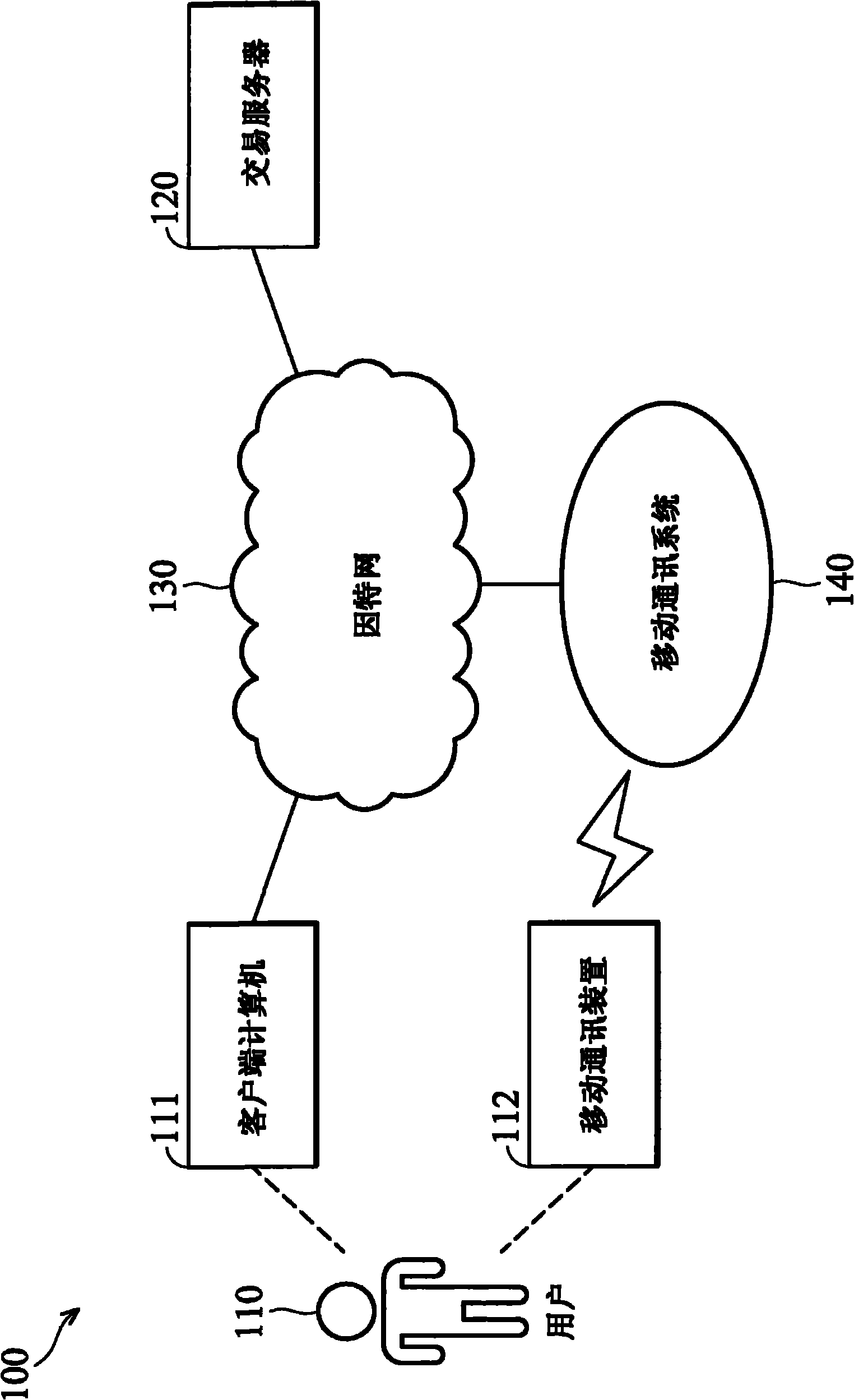
[0030] figure 1 It is a schematic diagram of a two-factor online transaction security authentication system according to an embodiment of the present invention. The two-factor online transaction security authentication system 100 includes an electronic device representing a user 110 - a client computer 111 and a mobile communication device 112 , and a transaction server 120 . Wherein the client computer 111 and the transaction server 120 are respectively connected to the Internet 130, and transmit data to each other through the Internet 130 to carry out information communication required for online transactions. In addition, the mobile communication device 112 is connected to the mobile communicatio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More