Long-distance encryption method and device, management method and device, as well as encryption management method and device
A remote, key ciphertext technology, applied in transmission systems, electrical components, user identity/authority verification, etc., to reduce costs, improve satisfaction, and reduce costs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0060] In order to enable those skilled in the art to better understand the solutions of the embodiments of the present invention, the embodiments of the present invention will be further described in detail below in conjunction with the drawings and implementations.
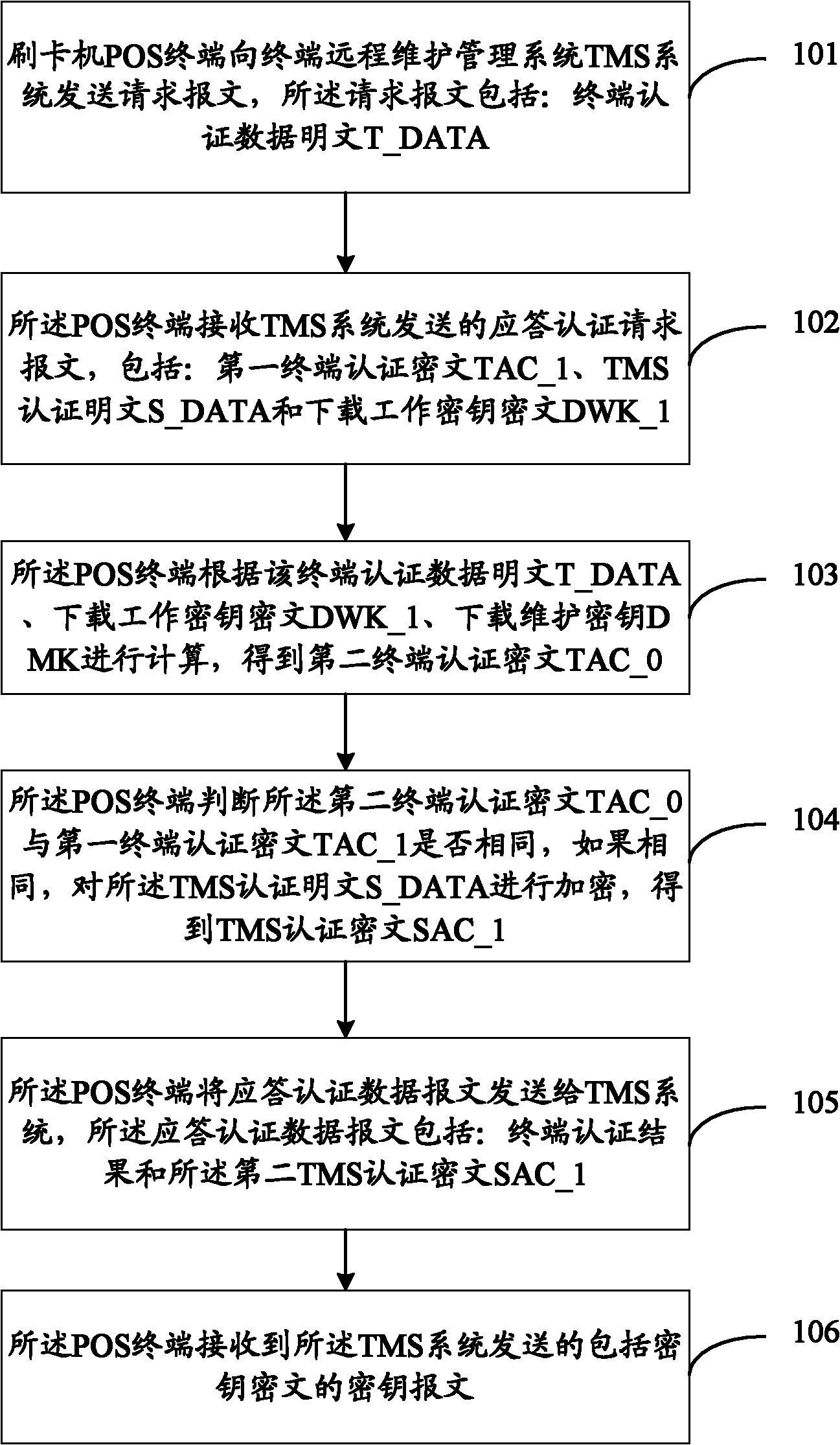
[0061] see also figure 1 , the present invention provides a flow chart of a remote encryption method, the method comprising:
[0062] Step 101: The POS terminal of the card reader sends a request message to the terminal remote maintenance management system TMS system, and the request message includes: terminal authentication data plaintext T_DATA;
[0063] Step 102: The POS terminal receives the response authentication request message sent by the TMS system, including: first terminal authentication ciphertext TAC_1, TMS authentication plaintext S_DATA and download work key ciphertext DWK_1;
[0064] Step 103: The POS terminal calculates according to the terminal authentication data plaintext T_DATA, the downloa...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More