Method for achieving home credible networking based on safety pendent of smart home device
A technology of smart home equipment and security pendant, which is applied in the direction of public keys for secure communication, electrical components, and network interconnection. The effect of strong confidentiality
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
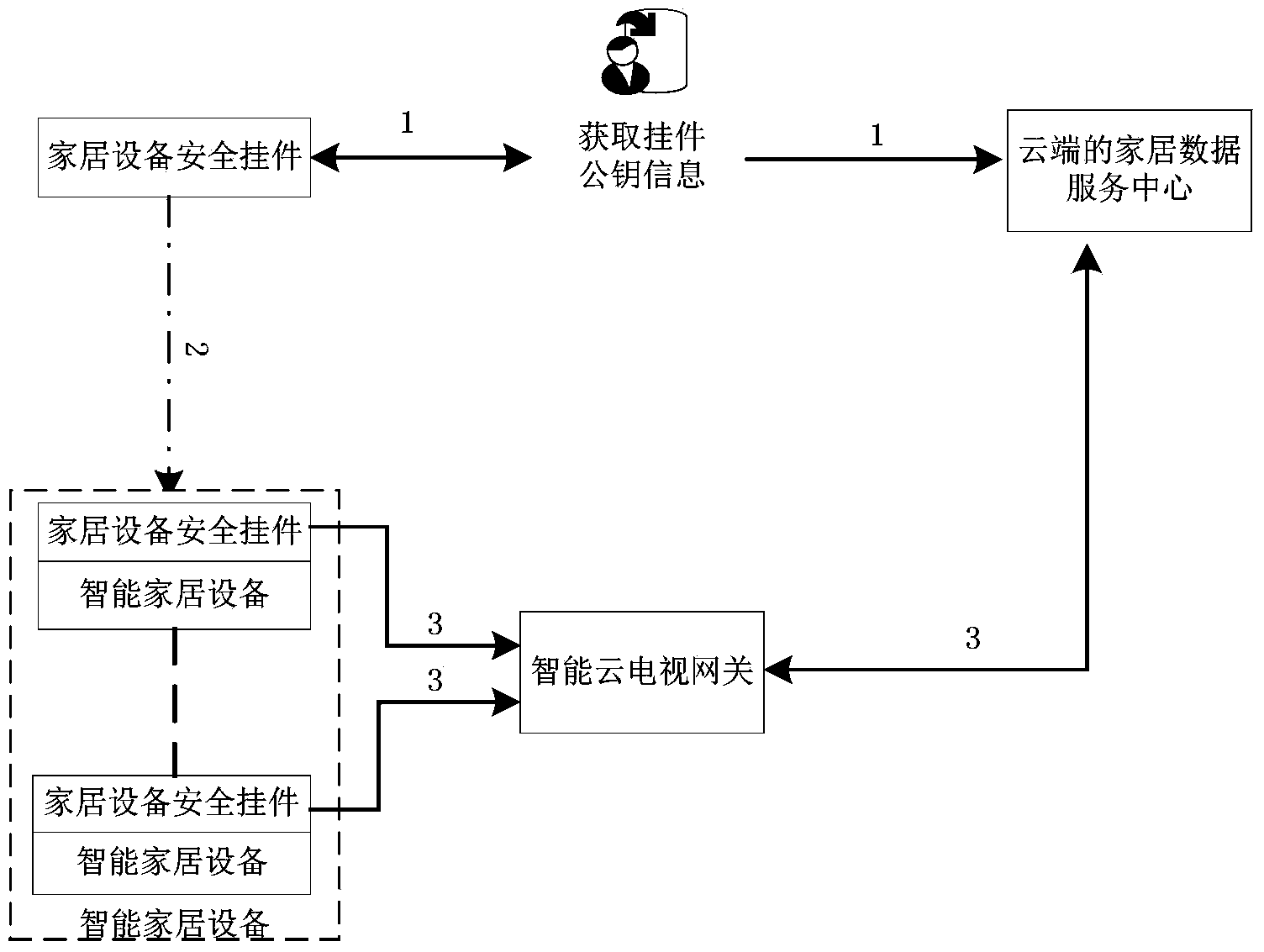
[0015] In order to make the purpose, advantages and technical solutions of the present invention clearer, through the following specific implementation, combined with the attached figure 1 , to further describe the present invention in detail.
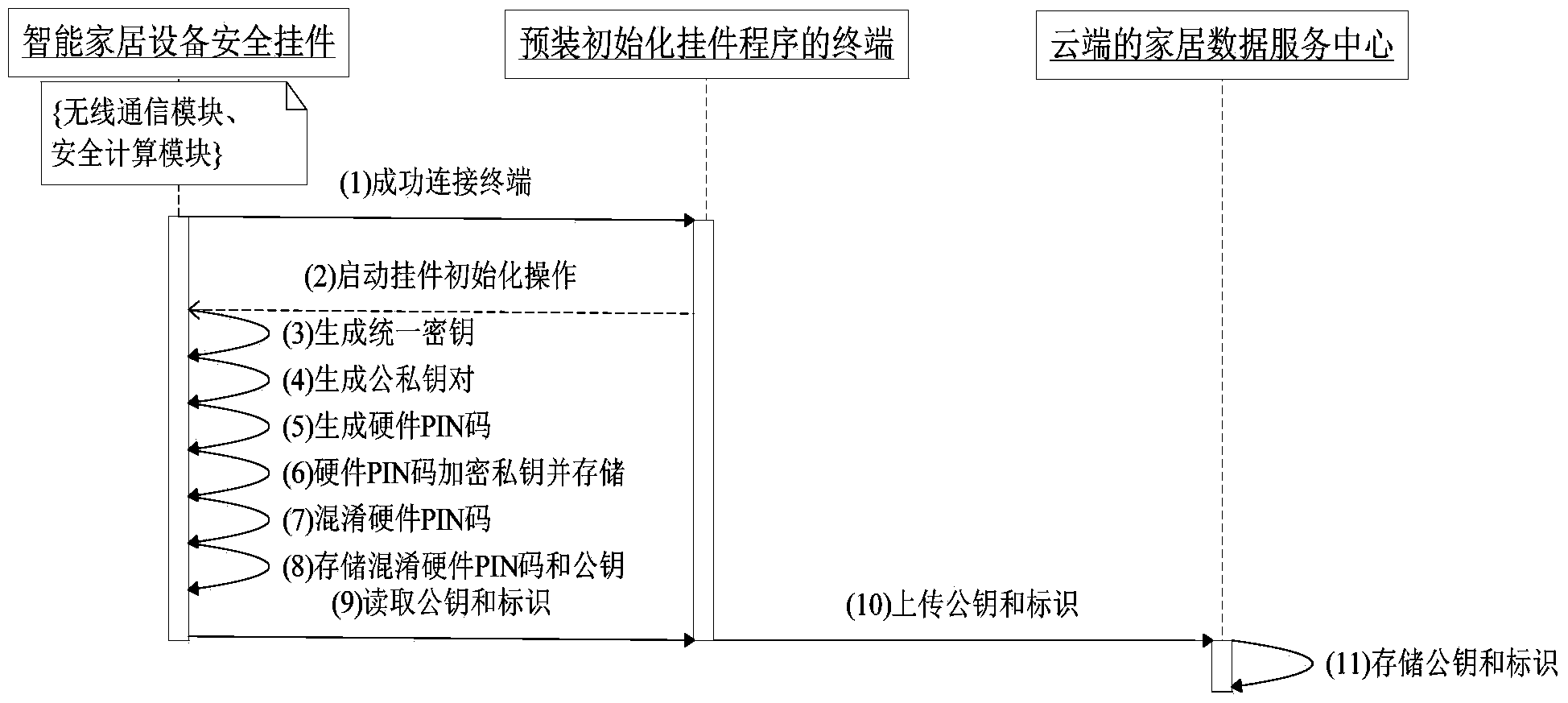
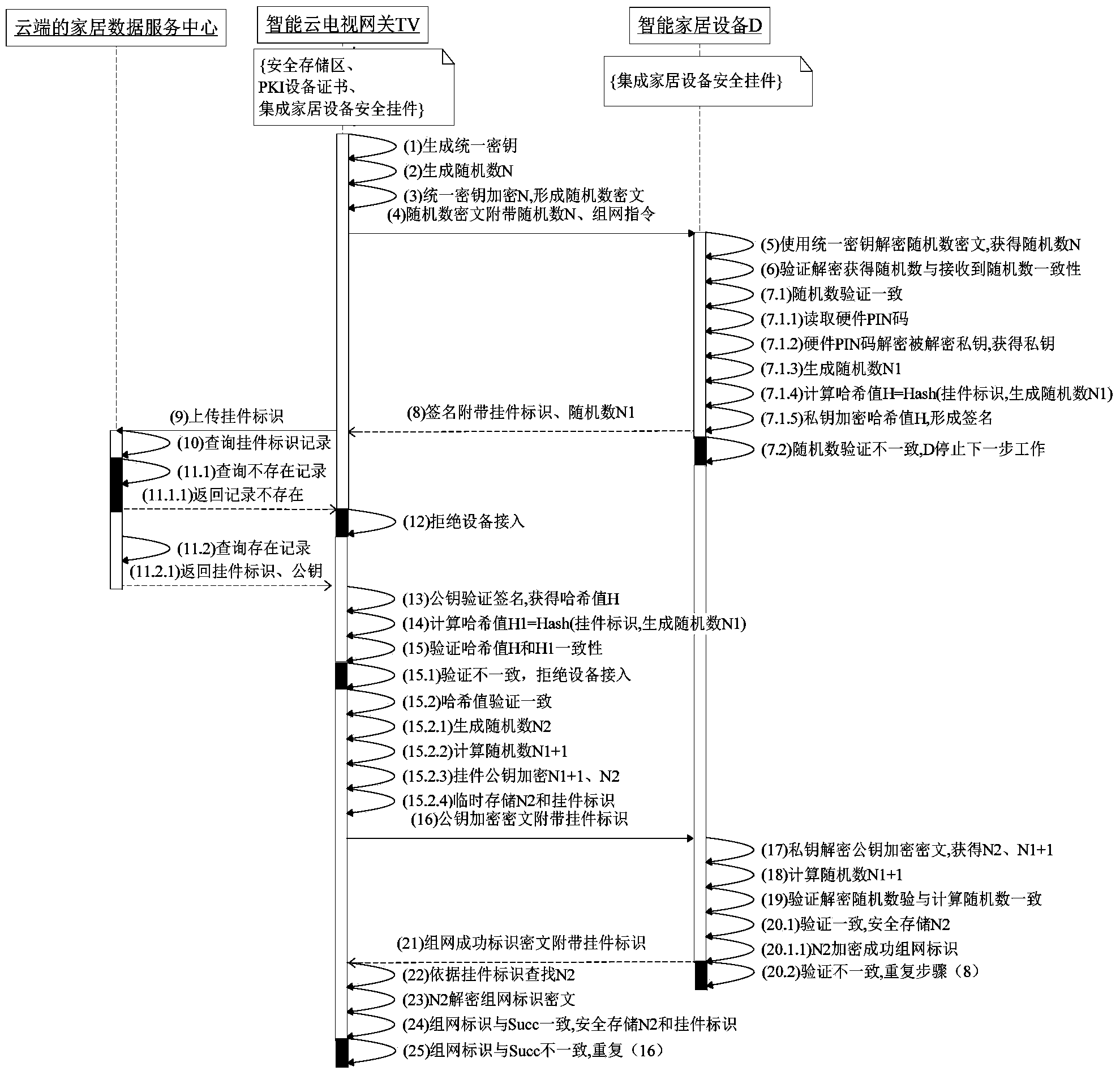
[0016] for figure 1 The overall framework of the scheme is described as a whole. In a nutshell, firstly, considering that users can conveniently complete the self-trusted networking of home devices and home gateways, the home device security pendant must obtain a public-private key pair [K D(pub) , K D(pri) ], hardware PIN code ((full name Personal Identification Number, referred to as PIN, is the identification password) and unified key K, and its public key K D(pub) Upload to the home data service center in the cloud, so as to complete the factory initialization of the home equipment security pendant; second, the user's smart home gateway and the home equipment integrated with the initialized home equipment security pendant, with t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com