Picture camouflaging method, picture viewing method, system and terminal
A technology of pictures and original pictures, used in computer security devices, instruments, computing, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
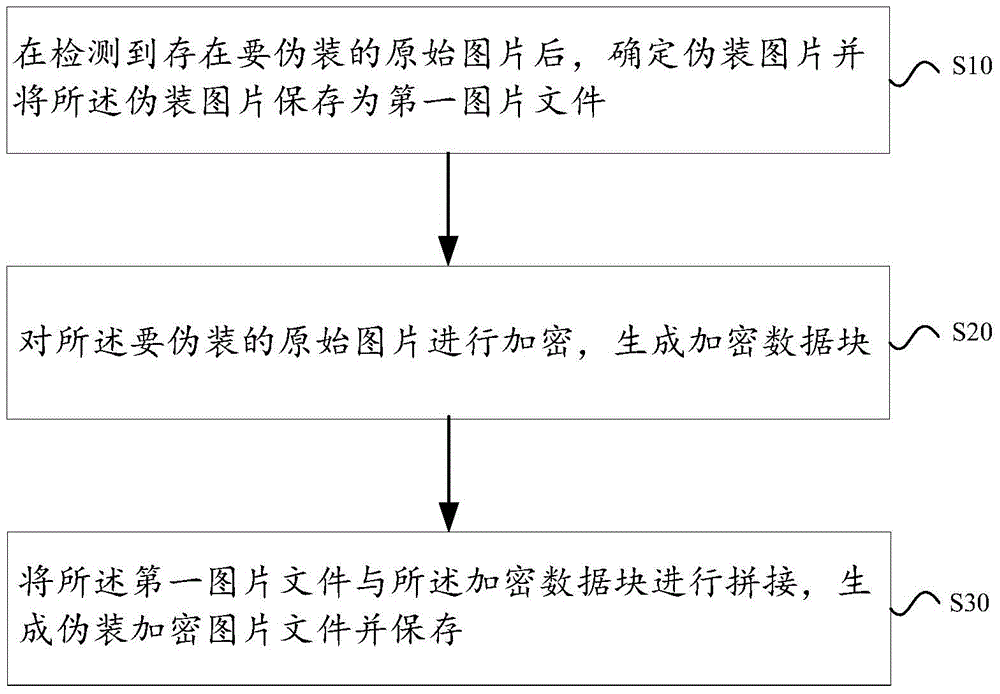
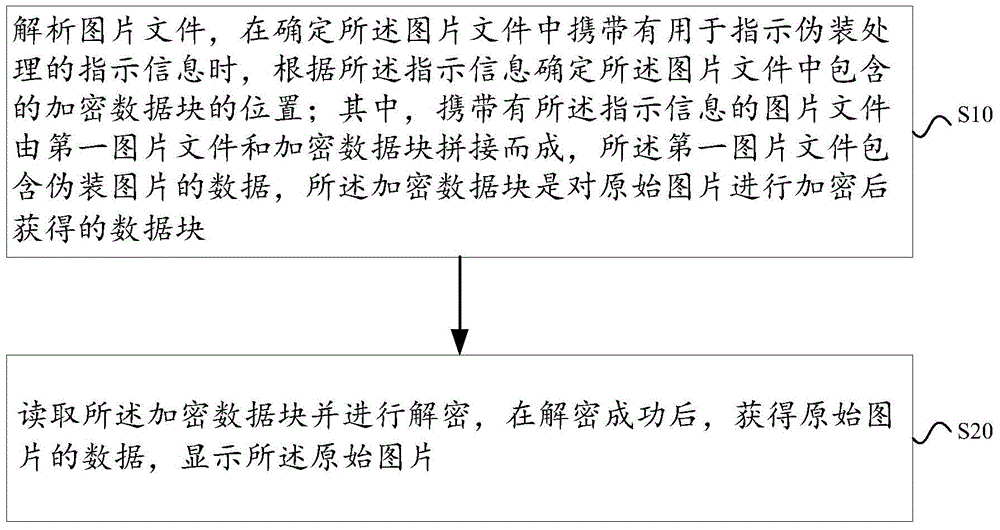
[0127] In order to make the purpose, technical solution and advantages of the present invention more clear, the embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined arbitrarily with each other.
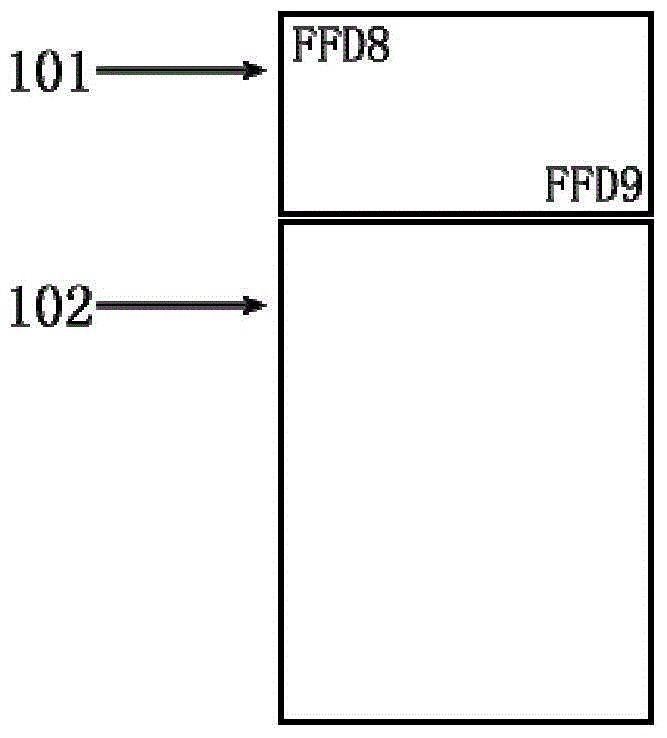
[0128] When the user wants to disguise a picture, the user sets a folder and sets a password, and the terminal monitors the folder. Once a picture file is found in this folder, it will automatically encrypt the original picture and disguise it as another picture; Alternatively, the user manually selects the original picture to be disguised, and after the selection, the terminal encrypts the original picture and disguises it as another picture.
[0129] The camouflaged picture file maintains the normal file format, so you can see the content of the picture using ordinary pictu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More