Method and system for preventing sensitive information from leakage
A sensitive information and algorithm technology, applied in the field of information security, can solve problems such as increasing the risk of log leakage, and achieve the effect of preventing leakage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be described in further detail below in conjunction with specific embodiments and with reference to the accompanying drawings. However, those skilled in the art know that the present invention is not limited to the drawings and the following embodiments.
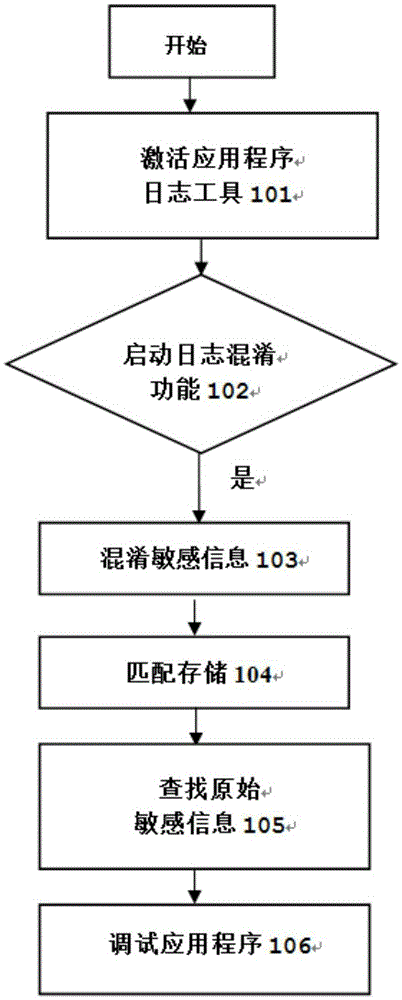
[0035] figure 1 It is a flowchart of a method for log obfuscation according to an embodiment of the present invention.
[0036] Step 101, before the client terminal runs the application program, the terminal user activates the log tool of the application program.
[0037] In this step, the application program installed on the client includes the application program interface. When the user needs to run a certain application program, the user selects the application program and displays the application program interface of the application program on the terminal screen. There is a button of the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More