Secure deletion method for data in solid-state disk on basis of flash memory
A data security and deletion method technology, applied in the direction of internal/peripheral computer component protection, etc., can solve the problems of overwriting affecting the life of flash memory and wear balance, data storage security of solid-state disk, and data cannot be safely deleted, etc., to improve the utilization of storage space efficiency, ensuring reliability and security, and ensuring the effect of data reliability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0035] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below can be combined with each other as long as they do not constitute a conflict with each other.
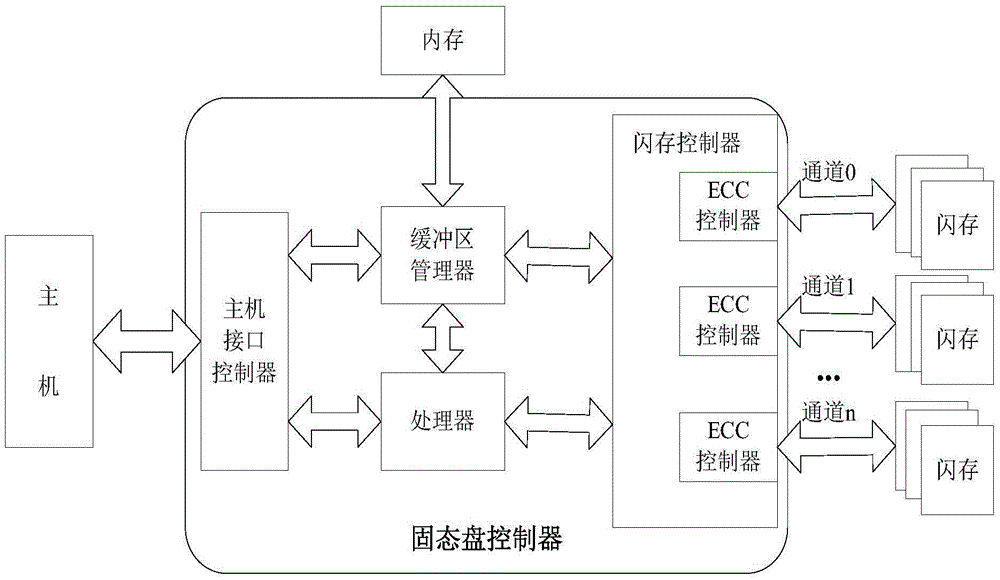
[0036] figure 1 It is a hardware structural diagram of the solid state disk of the present invention. Among them, the host interface controller implements protocol conversion and communicates with the host interface; the processor performs address allocation and mapping and task scheduling for the flash memory chip; the buffer manager is responsible for buffering the written data, sorting and m...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More