Method and device for loading code signatures to applications
An application and code technology, applied in the Internet field, can solve the problems of user terminal security threats, code signature tampering, and unclear attribution of applications, so as to avoid malicious tampering or theft of code signatures, prevent private key leakage, and ensure security. Effects of dissemination and use
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0053] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
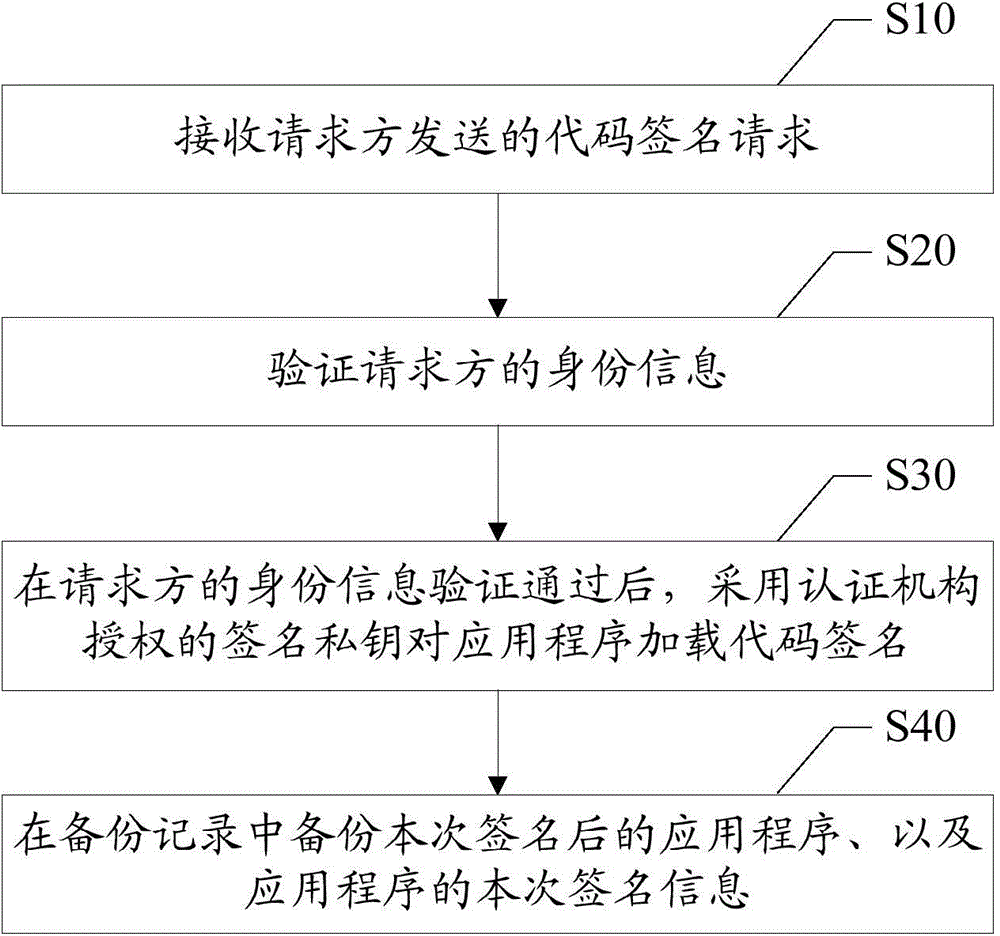
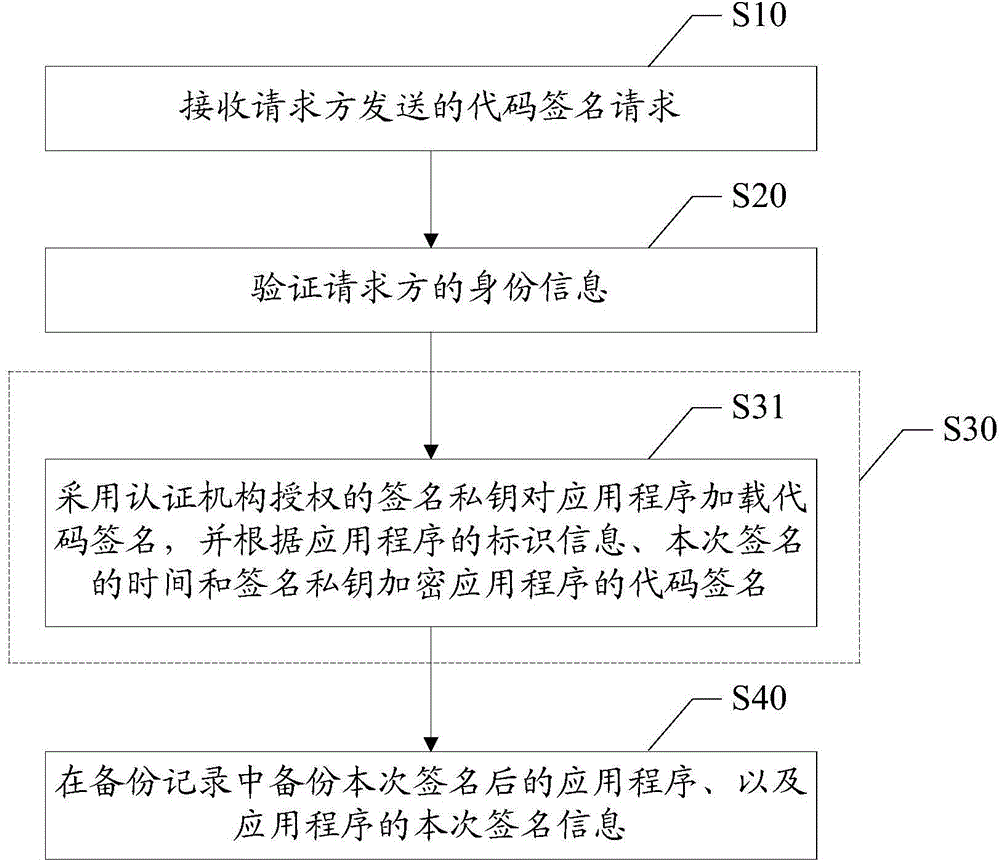
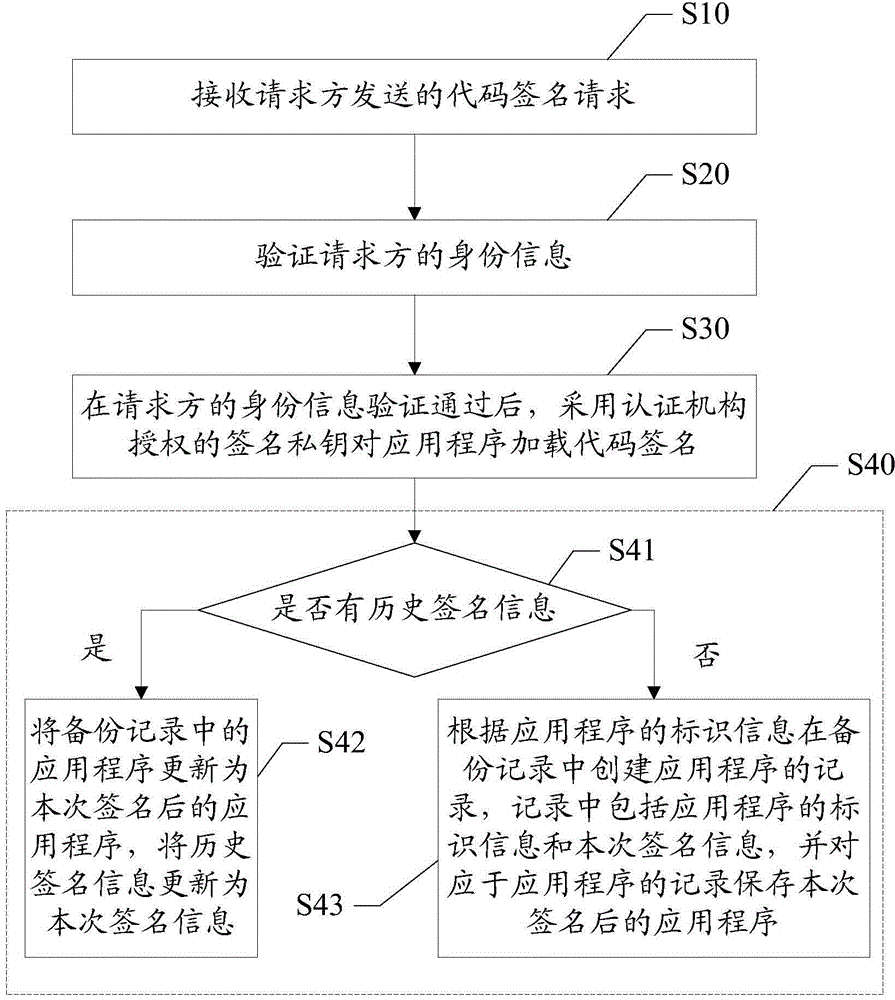
[0054] like figure 1 as shown, figure 1 A flow chart of the first embodiment of the method for loading a code signature for an application program of the present invention. The method for loading code signatures for applications proposed in this embodiment includes:
[0055] Step S10, receiving the code signing request sent by the requesting party;
[0056] In this embodiment, in order to improve the security of the code signature, the code signature for the application program to be released is implemented uniformly through the server. Specifically, the application publisher needs to send a code signing request to the server as a request before publishing the application, and the code signing request includes the identity information of the requesting party and the application to be signed. The requester may conn...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More