Device and method for authenticating a user
A technology for authenticating users and devices, applied in digital data authentication, character and pattern recognition, instruments, etc., to reduce the risk of security breaches
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0044] The present invention will now be described more fully hereinafter with reference to the accompanying drawings, in which certain embodiments of the invention are shown. However, this invention may be embodied in many different forms and should not be construed as limited to the embodiments set forth herein. Rather, these embodiments are given by way of example so that this disclosure will be thorough and complete, and will fully convey the scope of the invention to those skilled in the art.
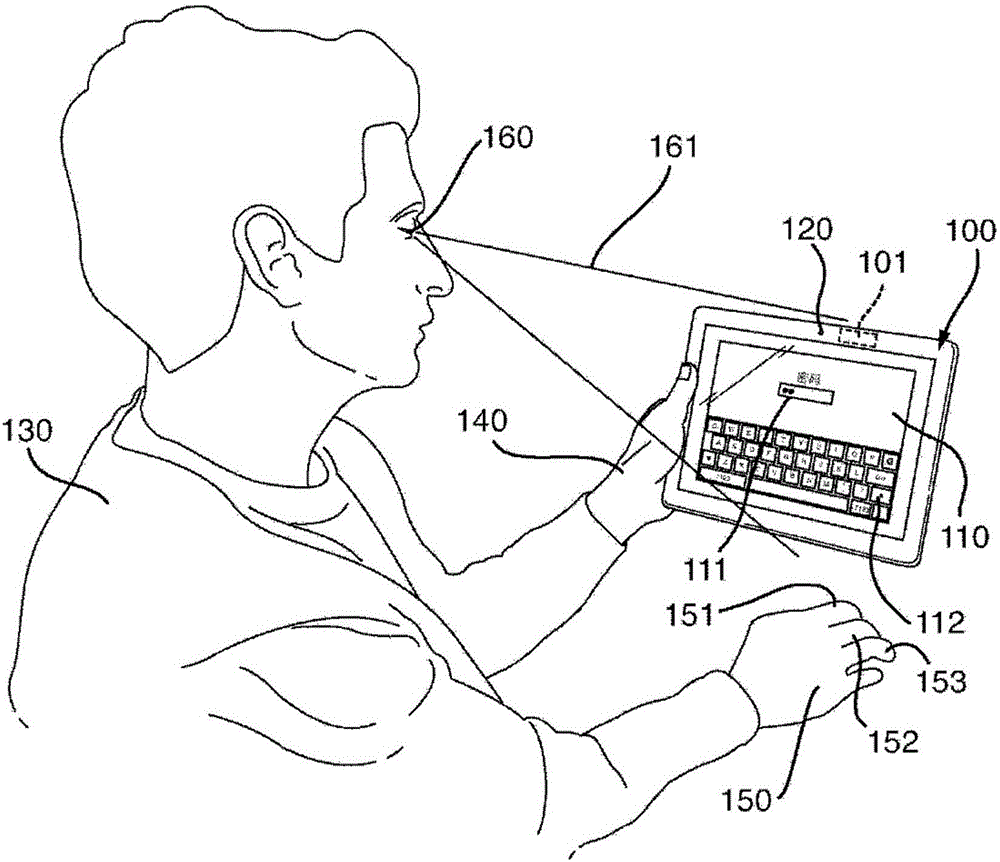
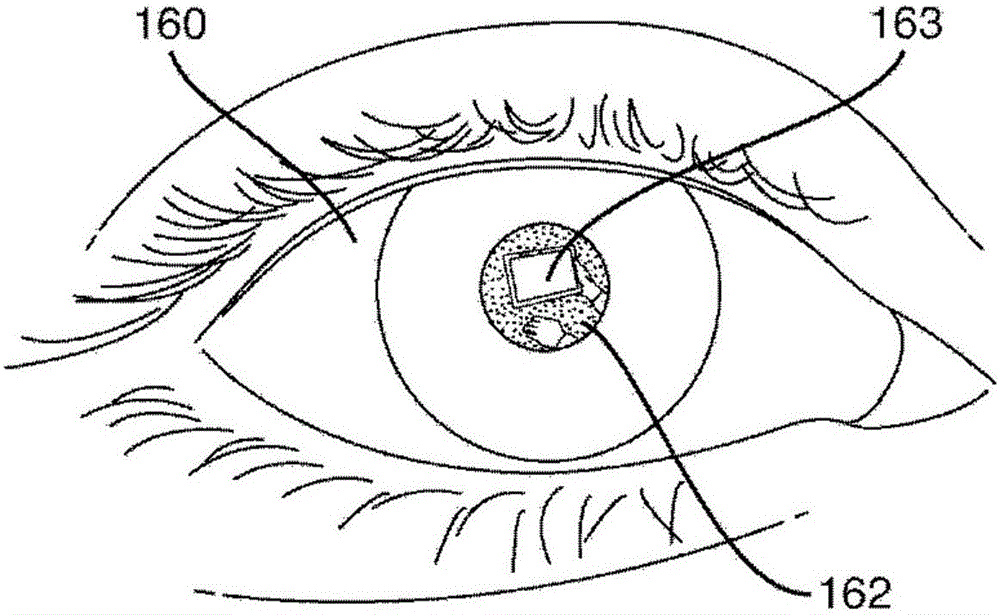
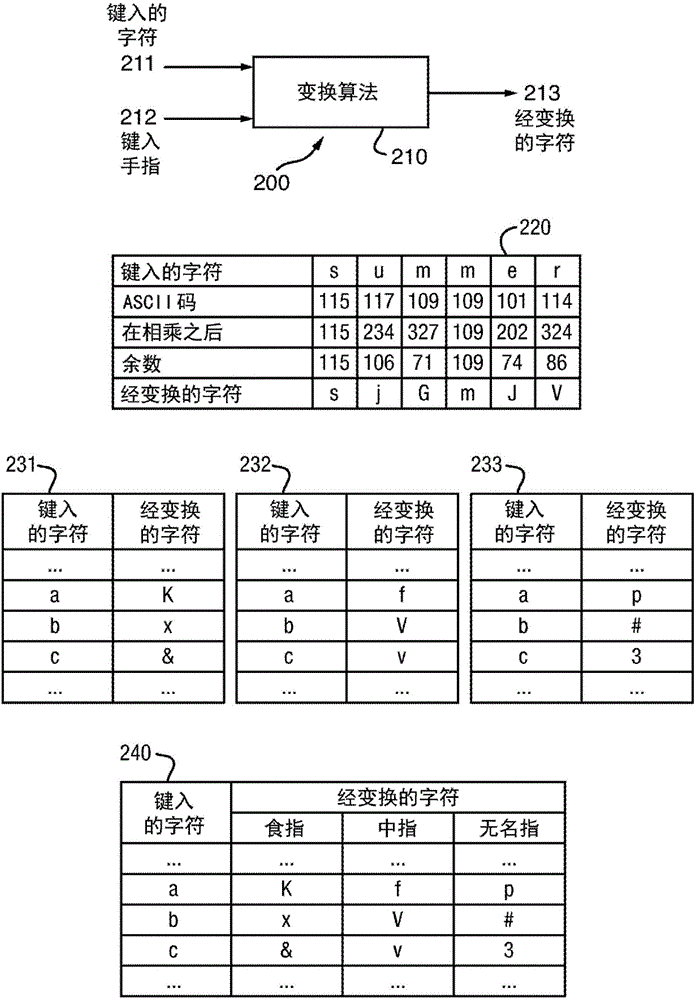
[0045] exist Figure 1a In , an apparatus 100 for authenticating a user 130 is shown, according to an embodiment of the invention. exist Figure 1a A device 100 , shown as a tablet computer, includes a processing device 101 , a touch screen 110 as a display, and a front camera 120 . Touchscreen 110 may serve as an output device for device 100 (ie, for displaying graphical content such as user interface elements (eg, virtual buttons or keys, pictures, text snippets, fields for ente...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com