Black hole attack defense method applied to route discovery
A black hole attack and routing technology, applied in the field of black hole attack defense, can solve the problems of low practical applicability and difficulties of trusted third parties, and achieve good adaptability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
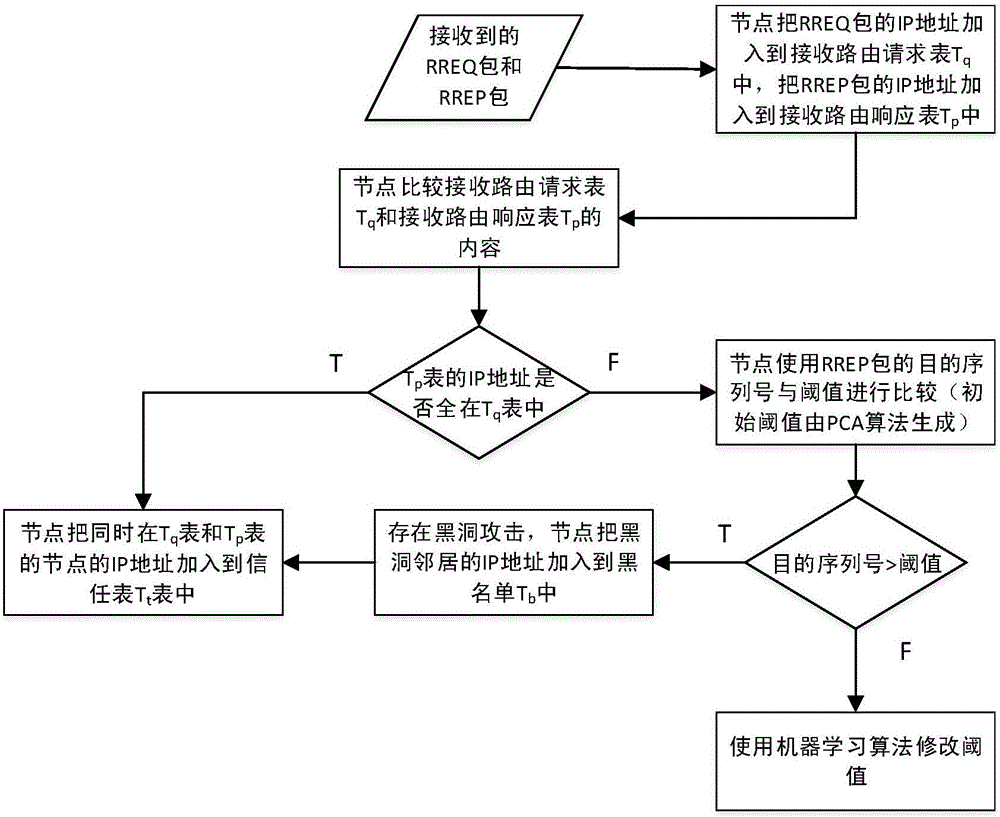
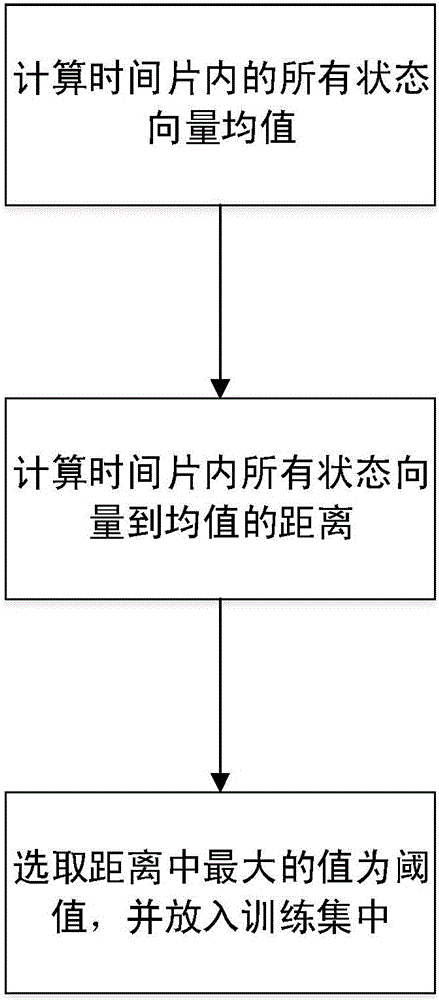
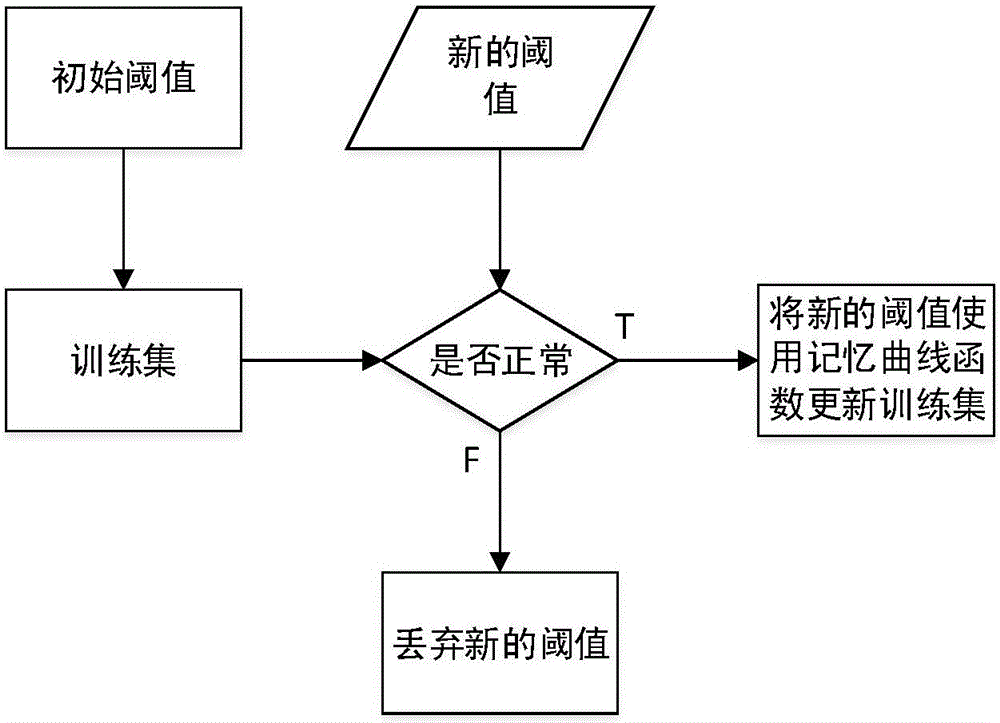
[0040] The present invention uses based on receiving routing request table T q and receive routing response table T p The comparison method obtains a set of suspicious nodes, and then uses the machine learning algorithm to obtain the threshold of the destination sequence number of the routing response packet, and then the source node compares the destination sequence number of the received routing response packet with the threshold to determine whether a black hole attack has occurred, and uses The comparison of the above two tables results in the black hole node.
[0041] The present invention receives the routing request table T q , Receive routing response table T p The knowledge of set theory and engineering optimization is applied in the step of comparison and the step of applying machine learning algorithm to dynamically calculate the serial number threshold, and the symbols used are shown in Table 1.
[0042]
[0043]
[0044] Note: 0
[0045] The present ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More