Quantum secret sharing method capable of resisting intercept-resend attack, man-in-the-middle attack and entanglement attack
A quantum secret and man-in-the-middle technology, applied in the field of information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0021] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
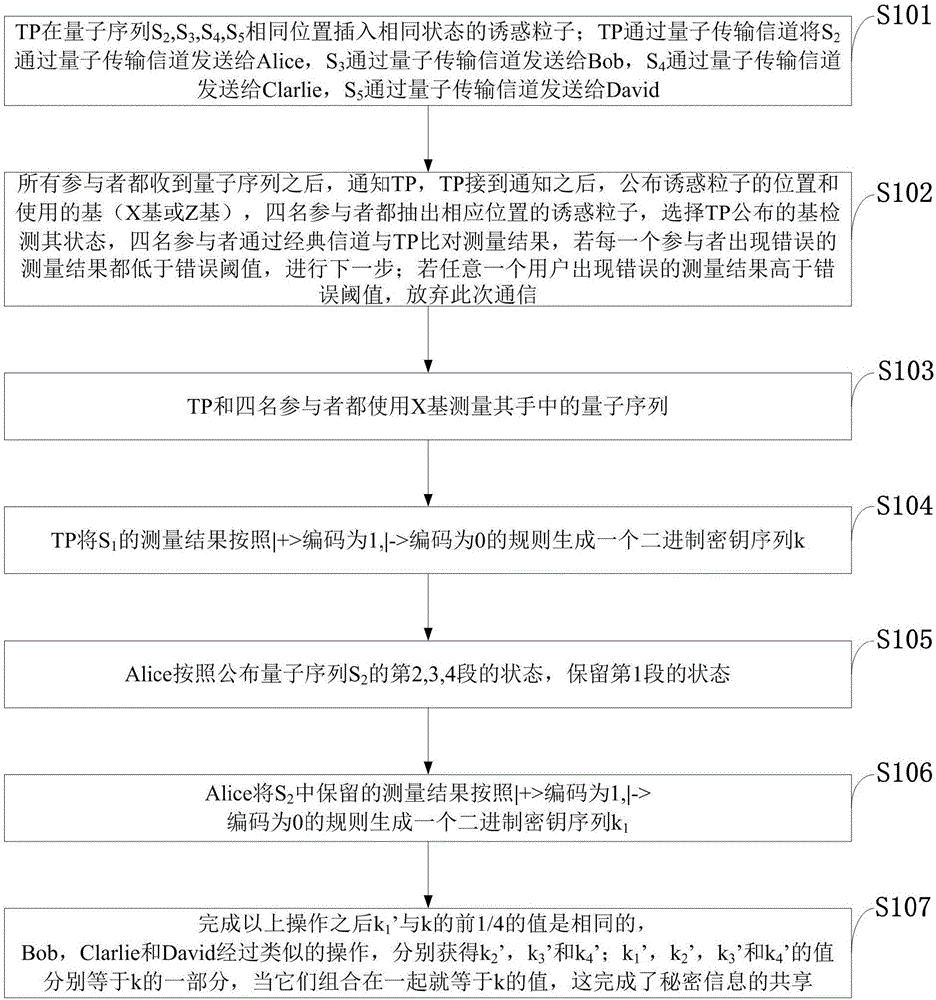
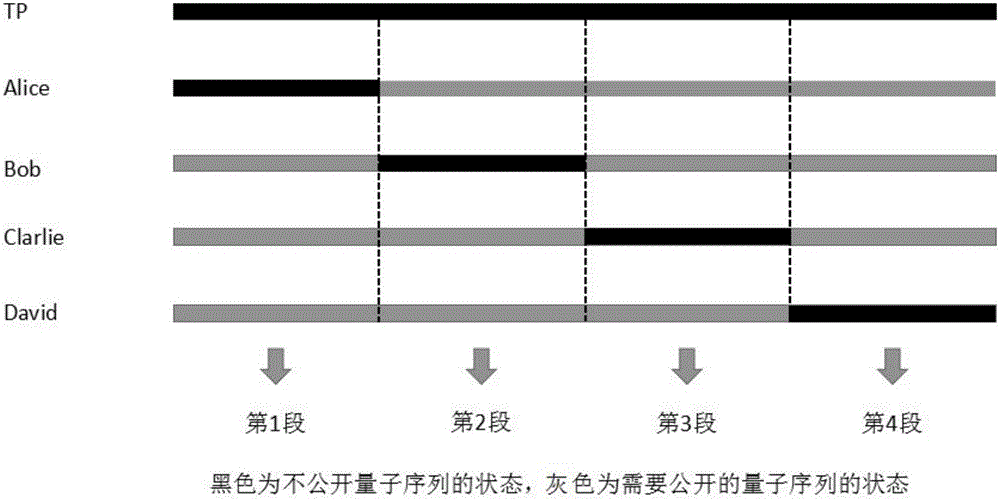
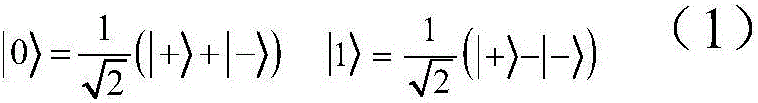
[0022] The secret sharing system proposed by the present invention is a (4,4) secret sharing protocol based on the five-particle GHZ state, that is, the secret information is distributed to 4 different participants, and when it is necessary to obtain the secret information, the 4 participants need to jointly Cooperation. After security analysis, the protocol can resist interception and retransmission attack, man-in-the-middle attack and entanglement attack, which proves the security of the protocol.
[0023] The application principle of the present invention will be described in detail below in conjunction with the accompa...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More