Generating cryptographic checksums
An encryption verification and generator technology, applied in encryption devices with shift registers/memory, user identity/authority verification, transmission systems, etc., can solve problems such as database space consumption, and achieve the effect of less storage space
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0047] The present invention will now be described more fully hereinafter with reference to the accompanying drawings, in which specific embodiments of the invention are shown. This invention may, however, be embodied in many different forms and should not be construed as limited to the embodiments set forth herein. Rather, these embodiments are given by way of example so that this disclosure will be thorough and complete, and will fully convey the scope of the invention to those skilled in the art.
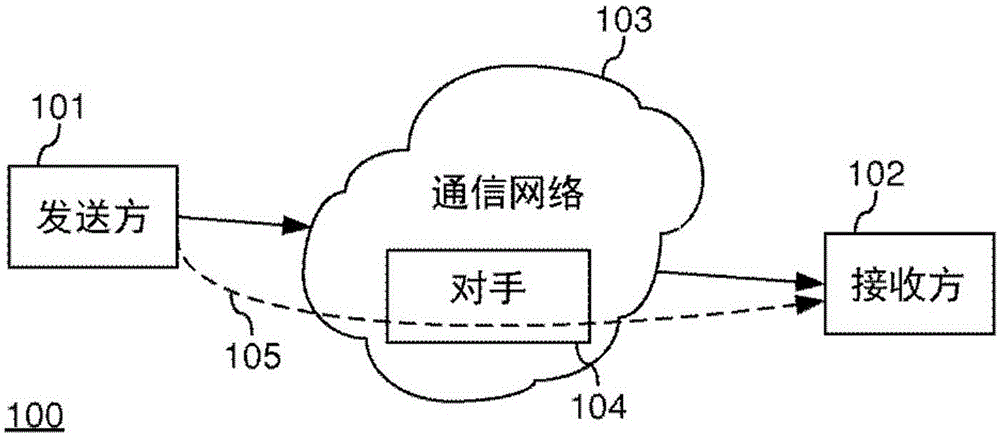
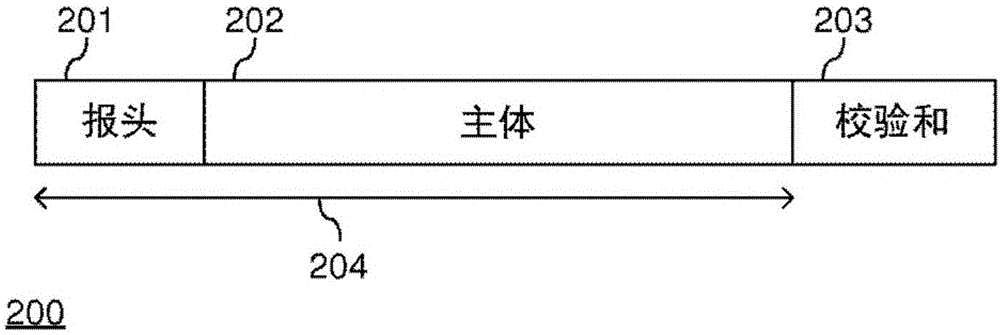
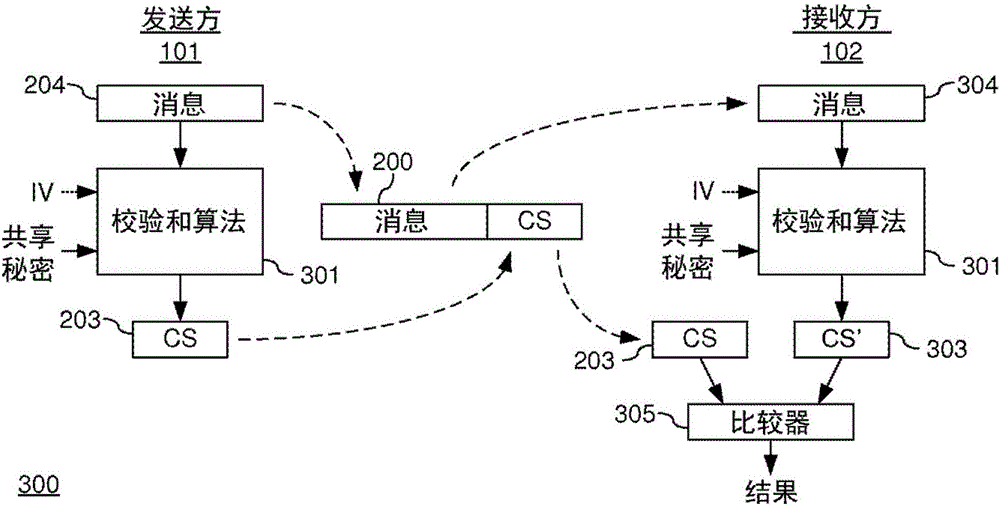
[0048] exist figure 1 In , a communication system 100 is shown comprising a sender 101 and a receiver 102 configured to communicate over a communication network 103 . Specifically, sender 101 is configured to send message 105 and receiver 102 is configured to receive message 105 . Preferably, the sender 101 and the receiver 102 are configured to send and receive messages. The sender 101 and the receiver 102 may be any type of device capable of communicating through the communi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More