Method and device for detecting malicious software
A malware and software technology, applied in the field of communication networks, which can solve problems such as inability to effectively detect ransomware
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
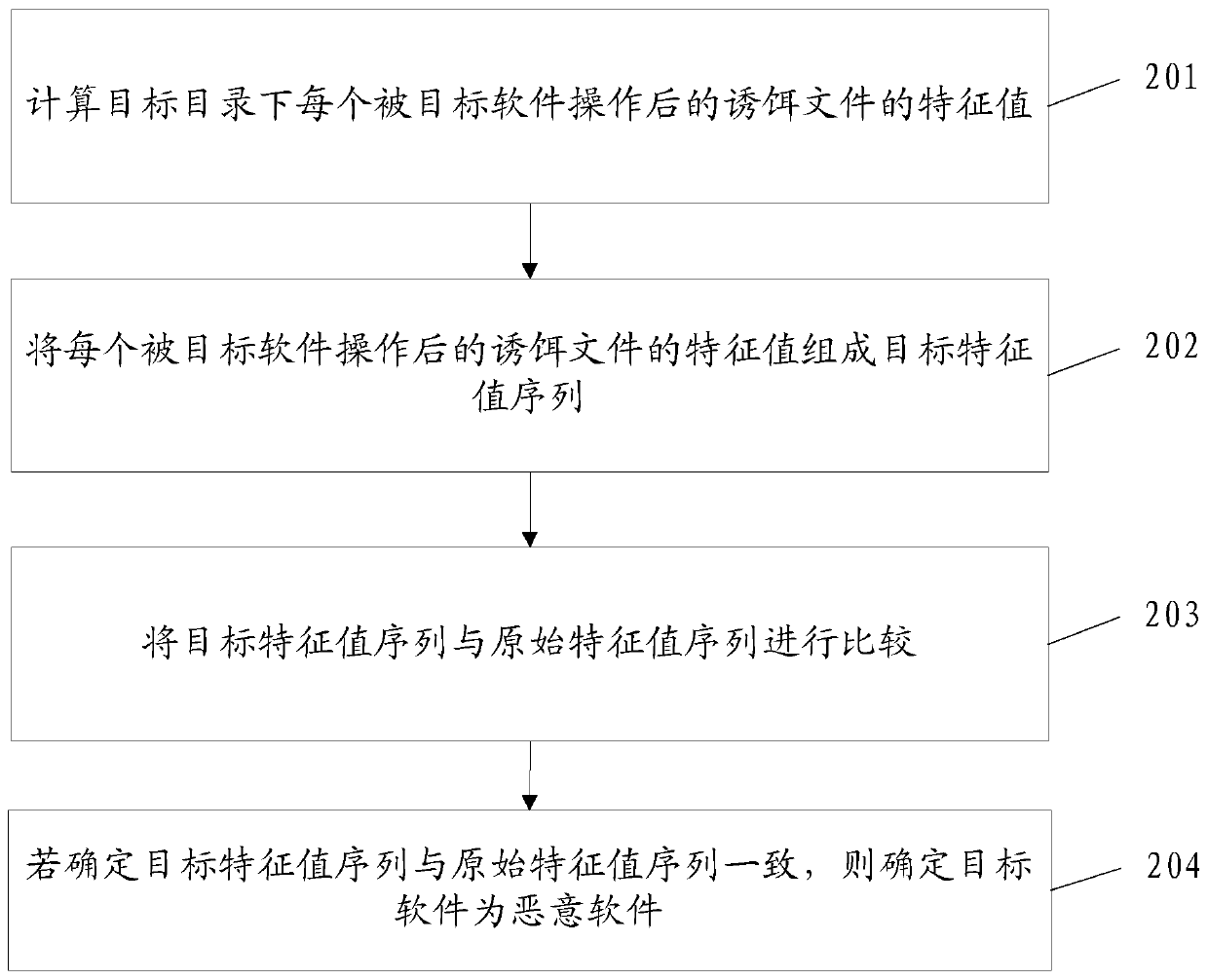
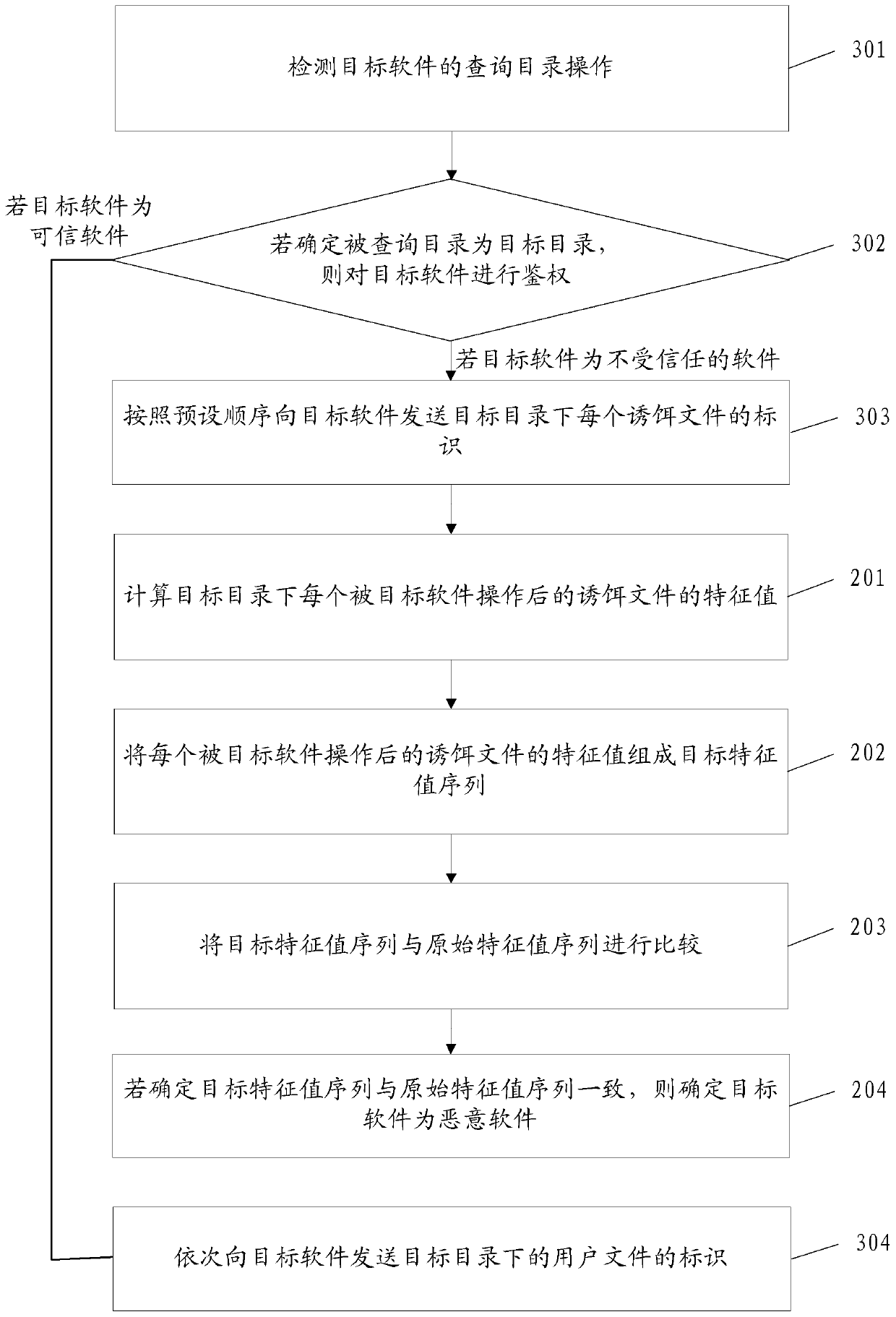
[0025] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the drawings in the embodiments of the present invention.
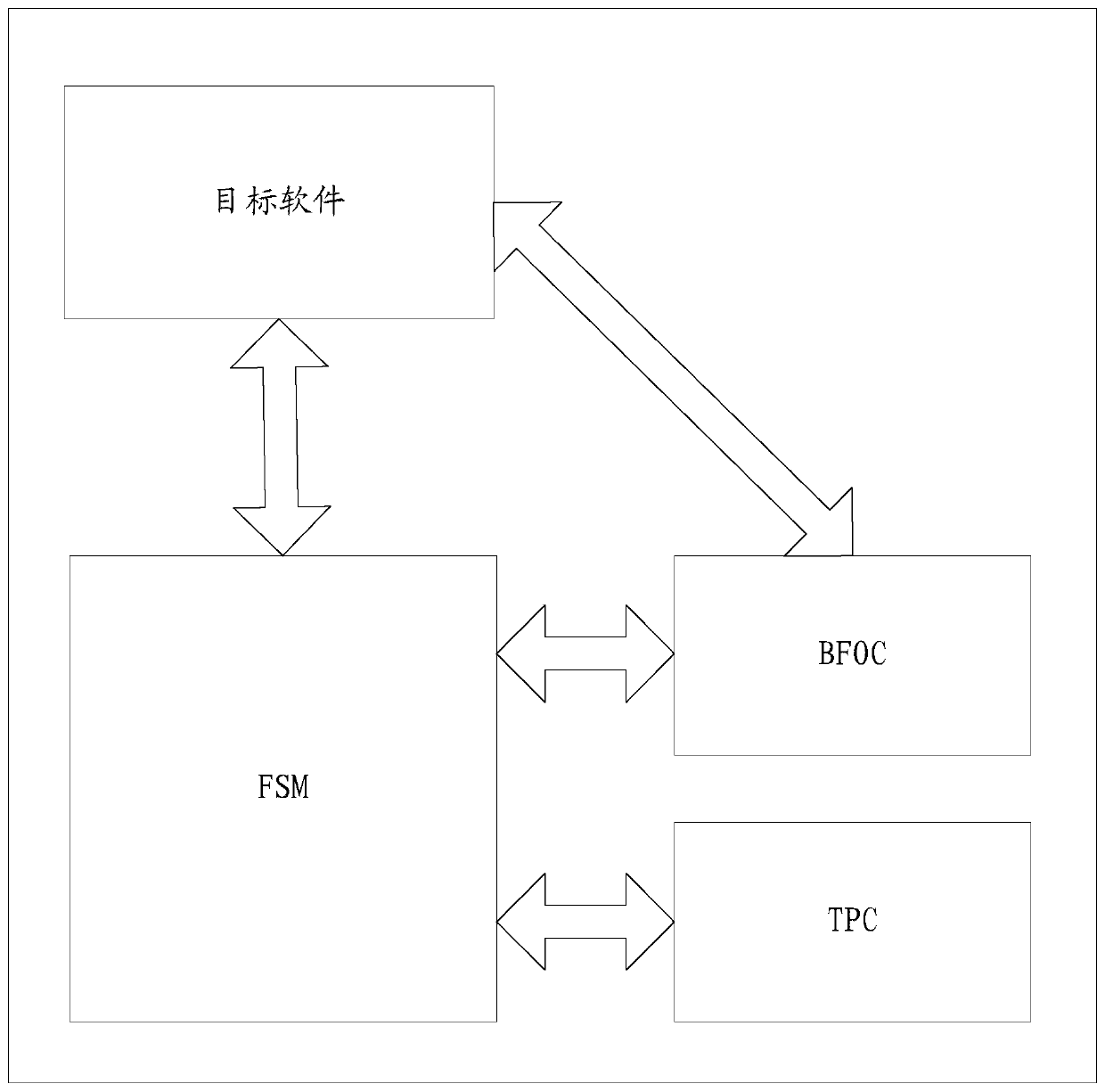
[0026] The method for detecting malicious software provided by the embodiment of the present invention is applied to a terminal, and the schematic diagram of the logical structure of the terminal is as follows figure 1 As shown, the terminal includes: Bait File Operation Checker (Bait File Operation Checker, hereinafter referred to as BFOC), Trusted Process Checker (Trusted Process Checker, hereinafter referred to as TPC), File System Monitor (File System Monitor, hereinafter referred to as FSM) ) and the target software. Among them, the FSM can communicate with the target software, BFOC, and TPC respectively, and the BFOC can communicate with the target software.
[0027] In addition, corresponding files are stored in each directory of the terminal. By calculating each file...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com