Authentication method and device
An authentication method and authentication device technology, applied in the field of information security, can solve problems such as limited protocols, exposure of mail services, and poor user experience, and achieve the effects of preventing brute force cracking, reducing security risks, and improving user experience.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
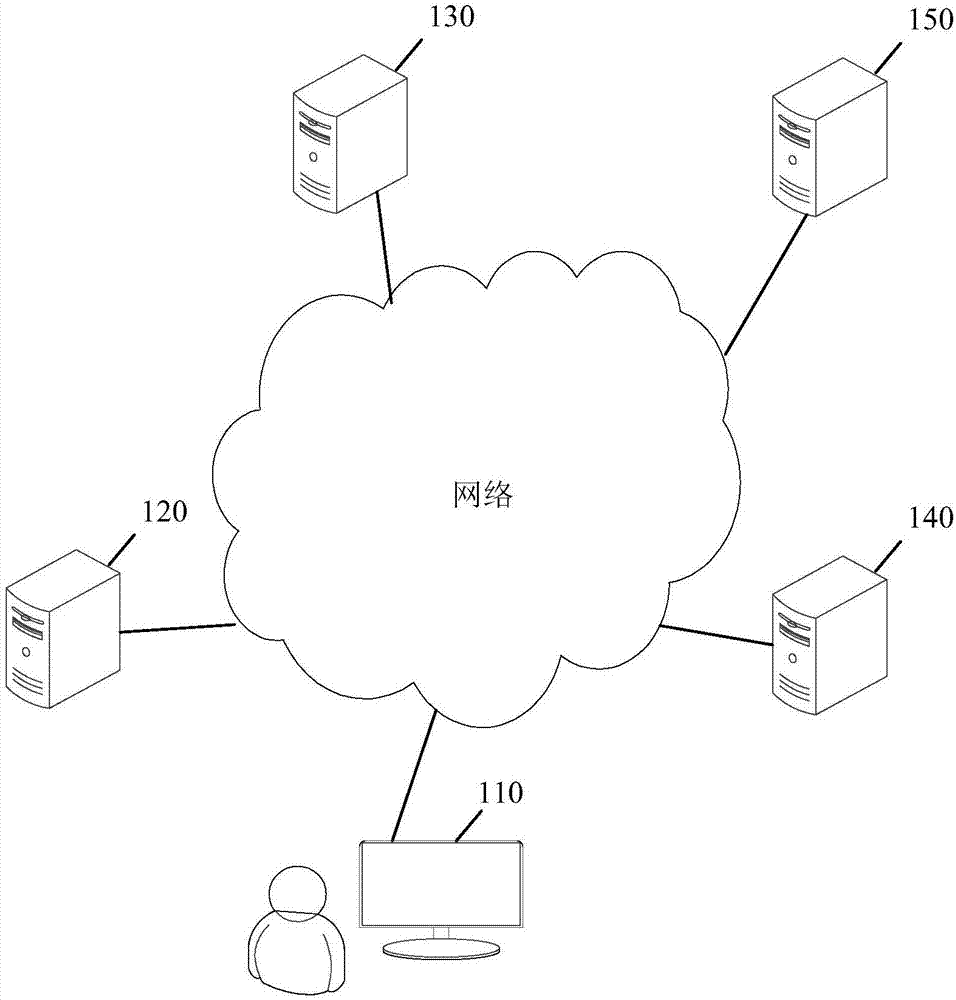
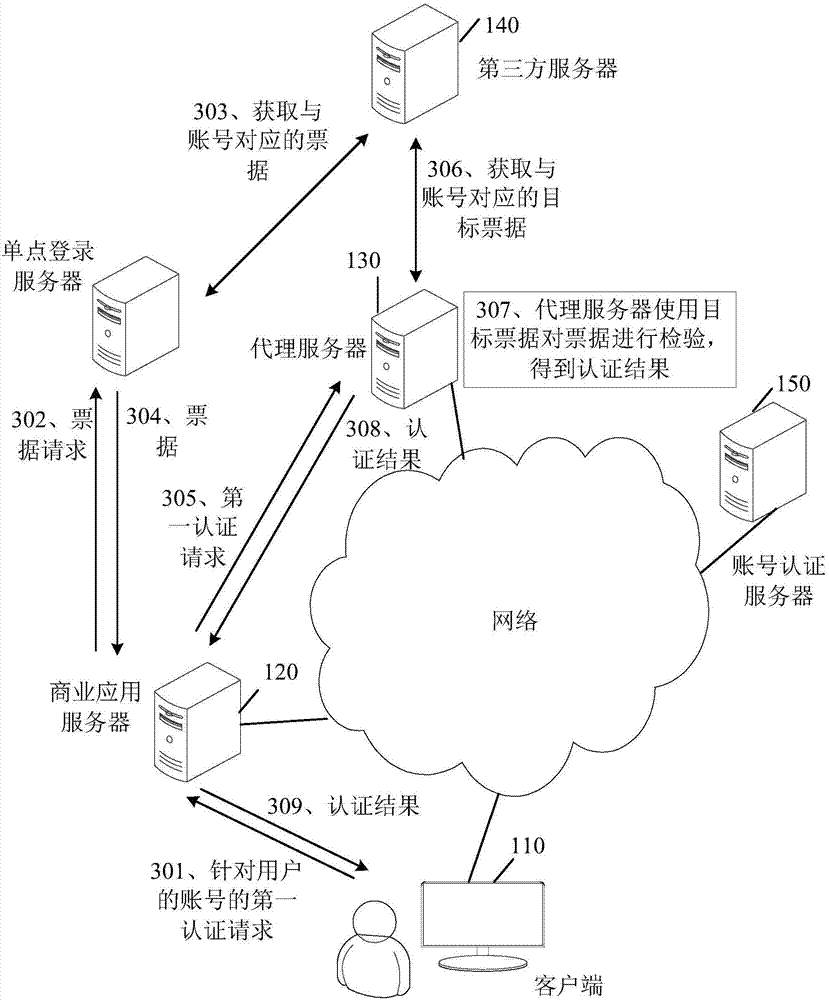
[0051] Reference will now be made in detail to the exemplary embodiments, examples of which are illustrated in the accompanying drawings. When the following description refers to the accompanying drawings, the same numerals in different drawings refer to the same or similar elements unless otherwise indicated. The implementations described in the following exemplary examples do not represent all implementations consistent with the present disclosure. Rather, they are merely examples of apparatuses and methods consistent with aspects of the present disclosure as recited in the appended claims.
[0052] Enterprise-level SSO is one of the commonly used business integration solutions for enterprises. Users want to connect Outlook to SSO services. However, due to the closed nature of Microsoft's commercial products, it is difficult for Outlook to access SSO services based on Microsoft's OWA mail server. This has the following problems: Problems: a) The user needs to enter the accoun...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More