Hierarchical protection safety compliance inspection method and system based on big data
A big data and security technology, applied in the field of high-level protection, can solve the problems of poor inspection accuracy and increase the workload of manual evaluation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
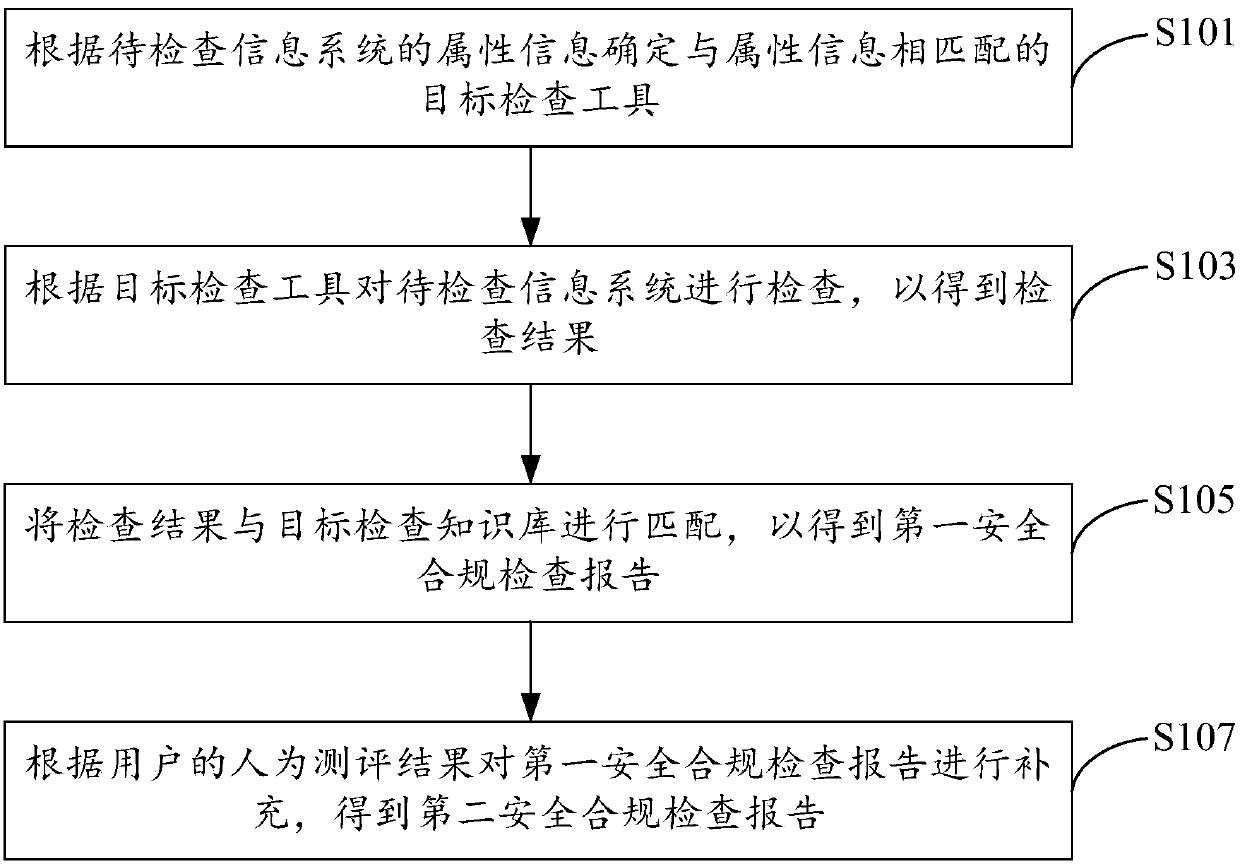
[0056] The embodiment of the present invention provides a big data-based hierarchical protection security compliance inspection method, refer to figure 1 , the method includes:
[0057] S101. Determine the target inspection tool that matches the attribute information according to the attribute information of the information system to be inspected, wherein the target inspection tool is a tool for performing hierarchical protection inspection on the information system to be inspected, and the attribute information includes: industry, name, inspection requirements ;
[0058] In the embodiment of the present invention, the big data-based hierarchical protection security compliance inspection method is specifically a method executed by the hierarchical protection security compliance inspection platform. When using the hierarchical protection security compliance inspection platform, the user needs to input the attribute information of the information system to be inspected, such as...
Embodiment 2
[0104] The embodiment of the present invention also provides a big data-based hierarchical protection security compliance inspection system, refer to Figure 4 , the system consists of:
[0105] The determining module 11 is configured to determine a target inspection tool that matches the attribute information according to the attribute information of the information system to be inspected, wherein the target inspection tool is a tool for performing hierarchical protection inspection on the information system to be inspected, and the attribute information includes: industry, name, check requirements;
[0106] The inspection module 12 is used to inspect the information system to be inspected according to the target inspection tool to obtain inspection results;
[0107] The matching module 13 is configured to match the inspection result with the target inspection knowledge base to obtain a first security compliance inspection report, wherein the target inspection knowledge base...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More