Data flow monitoring-based code reuse attack defending method and system
An attack defense system and code reuse technology, applied in the field of code reuse attack defense methods and systems based on data flow monitoring, can solve problems such as high overhead and data protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
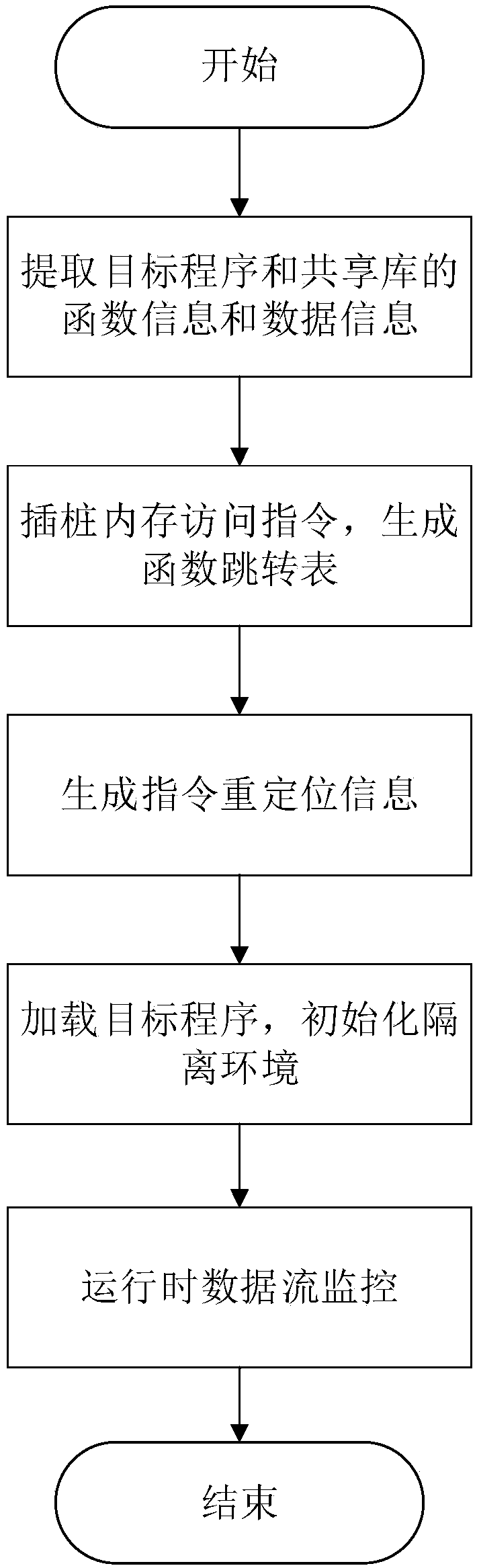
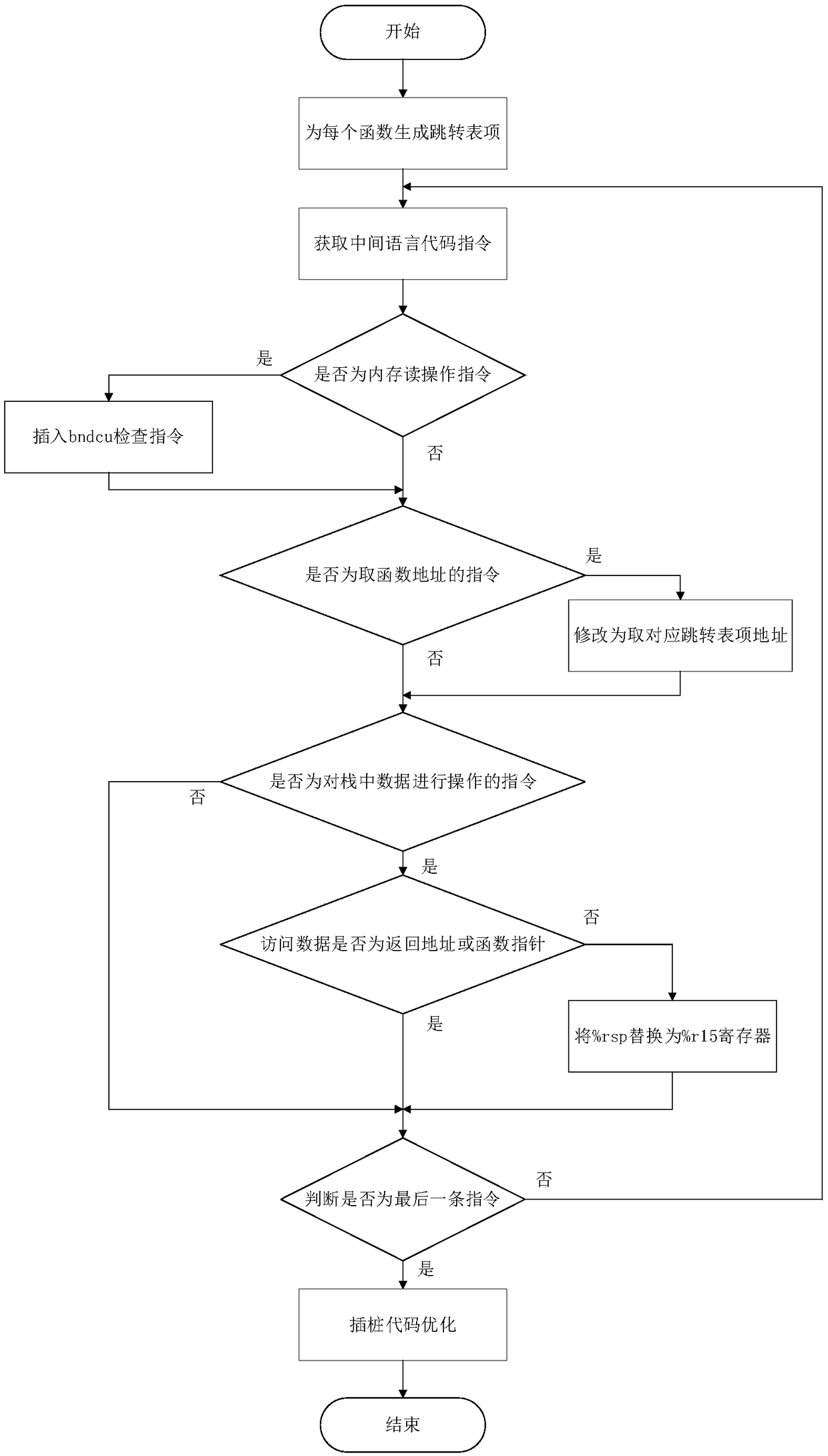
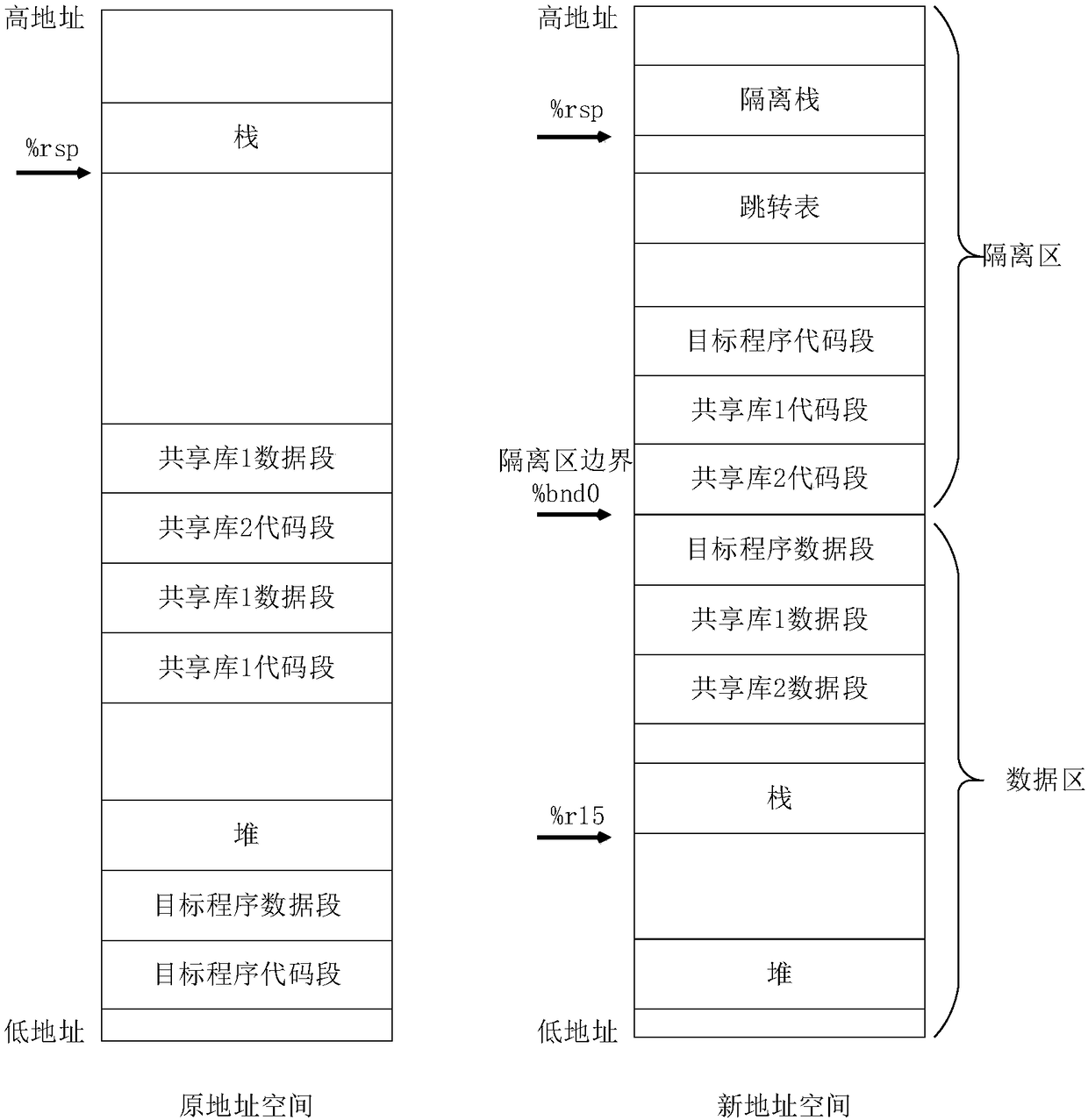
Method used
Image
Examples
Embodiment Construction
[0067] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below can be combined with each other as long as they do not constitute a conflict with each other.
[0068] This embodiment is implemented using the MPX instruction set. MPX (Memory Protection Extension) is a special instruction set on the X86_64 platform, which provides a set of boundary registers %bnd0-%bnd3, and a set of detection instructions, including bndcl, bndcu, etc. MPX is usually used to detect buffer overflow, data out of bounds, etc., and has the characteristics of high efficiency...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More