Fine-grained searchable encryption method for fog computing
An encryption method and fine-grained technology, applied in the field of information security, to achieve the effect of lightweight searchable encryption and broad application prospects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0056] The present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
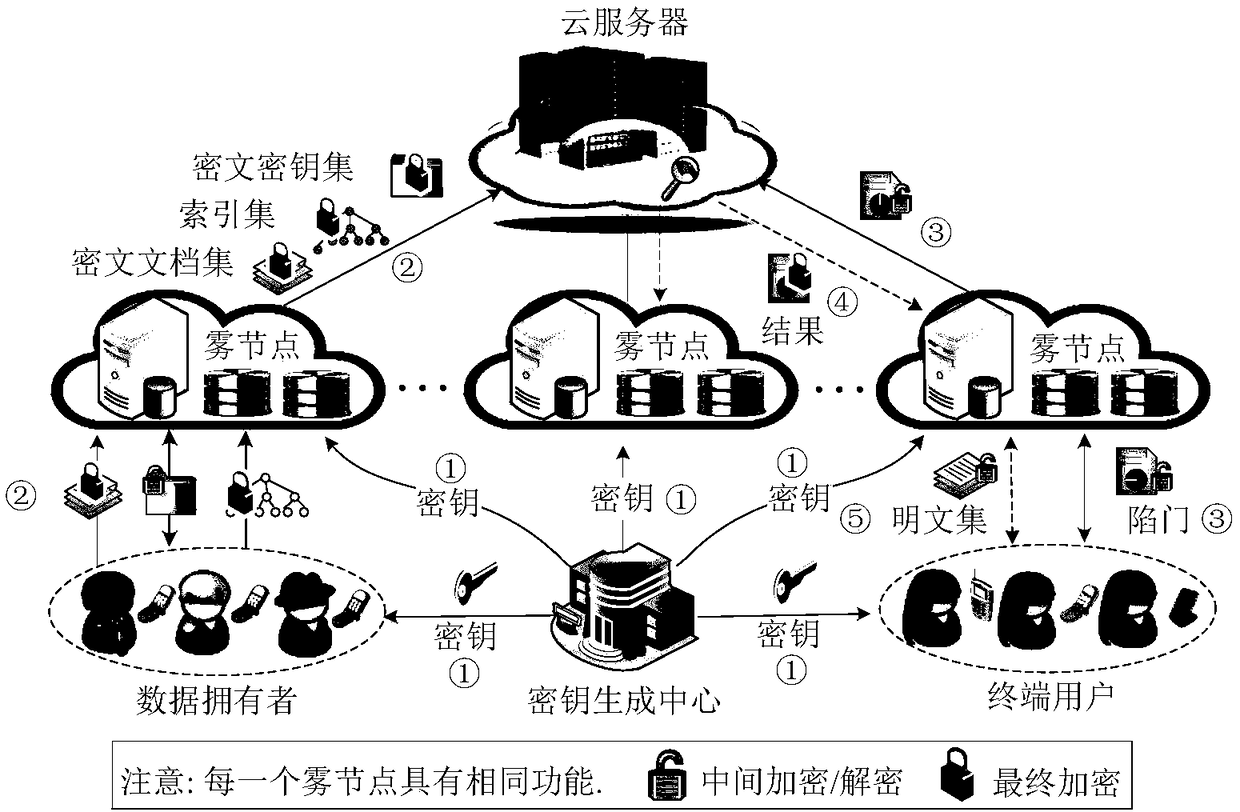
[0057] Such as figure 1 As shown, the present invention provides a fine-grained searchable encryption method for fog computing, comprising the following steps:
[0058] Step 1, system initialization: the key generation center KGC generates the public parameter pm and the master key msk according to the security parameter k, where:
[0059] public parameters
[0060] Master key msk=(x,y,{t i} i∈[1,n] );
[0061] where G is the additive cyclic group of order p, g 0 , g 1 are two different generators of G, G T is the p factorial cyclic group, e is the bilinear map G×G→G T , H 1 Indicates that the collection {0,1} * Mapped to the integer ring Z of order p p Hash function, x represents the first random number: x∈Z p , y represents the second random number: y∈Z p , t i Indicates the third random number: t i ∈ Z p , i∈[1,n] represent...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More