Multi-dimensional cheating bait implement system and method based on honey pot technology
A honeypot technology and a technology for realizing a system, which are applied in the field of multi-dimensional decoy decoy implementation systems based on honeypot technology, can solve the problem of lack of deception methods in multiple dimensions and layer by layer, and achieve reasonable structure settings, simple implementation methods, and guaranteed safe effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
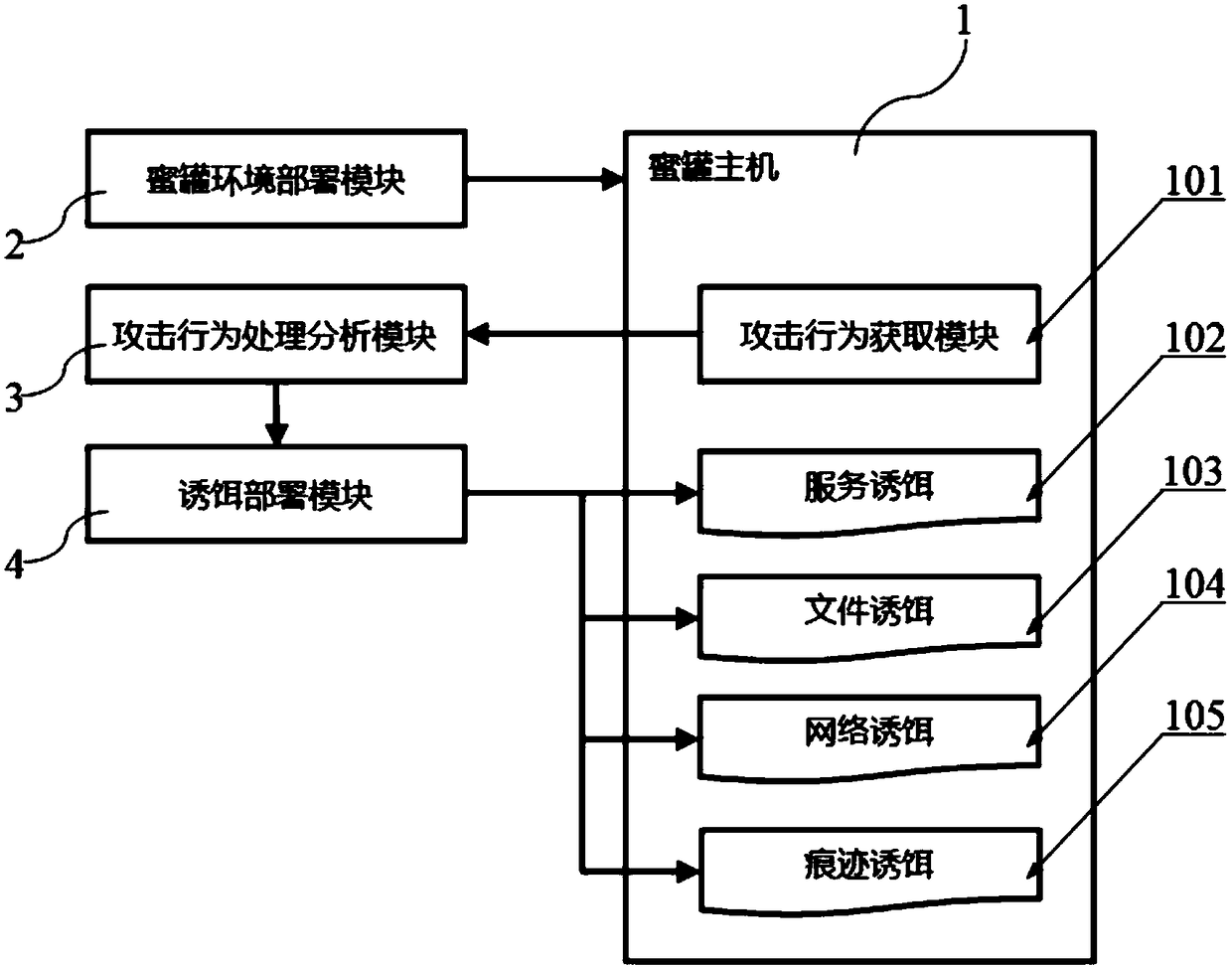
[0035] see figure 1 , a multi-dimensional deception decoy implementation system based on honeypot technology, including a honeypot host 1, a honeypot environment deployment module 2, an attack behavior processing analysis module 3 and a decoy deployment module 4, and an attack behavior acquisition module is set in the honeypot host 1 101 and a honeypot, wherein the honeypot includes a service bait 102, a file bait 103, a network bait 104 and a trace bait 105;
[0036] The honeypot environment deployment module 2 is connected to the honeypot host 1, the attack behavior acquisition module 101 is connected to the attack behavior processing and analysis module 3, and the attack behavior processing and analysis module 3 is connected to the decoy deployment Module 4, the decoy deployment module 4 is connected to the honeypot.
Embodiment 2
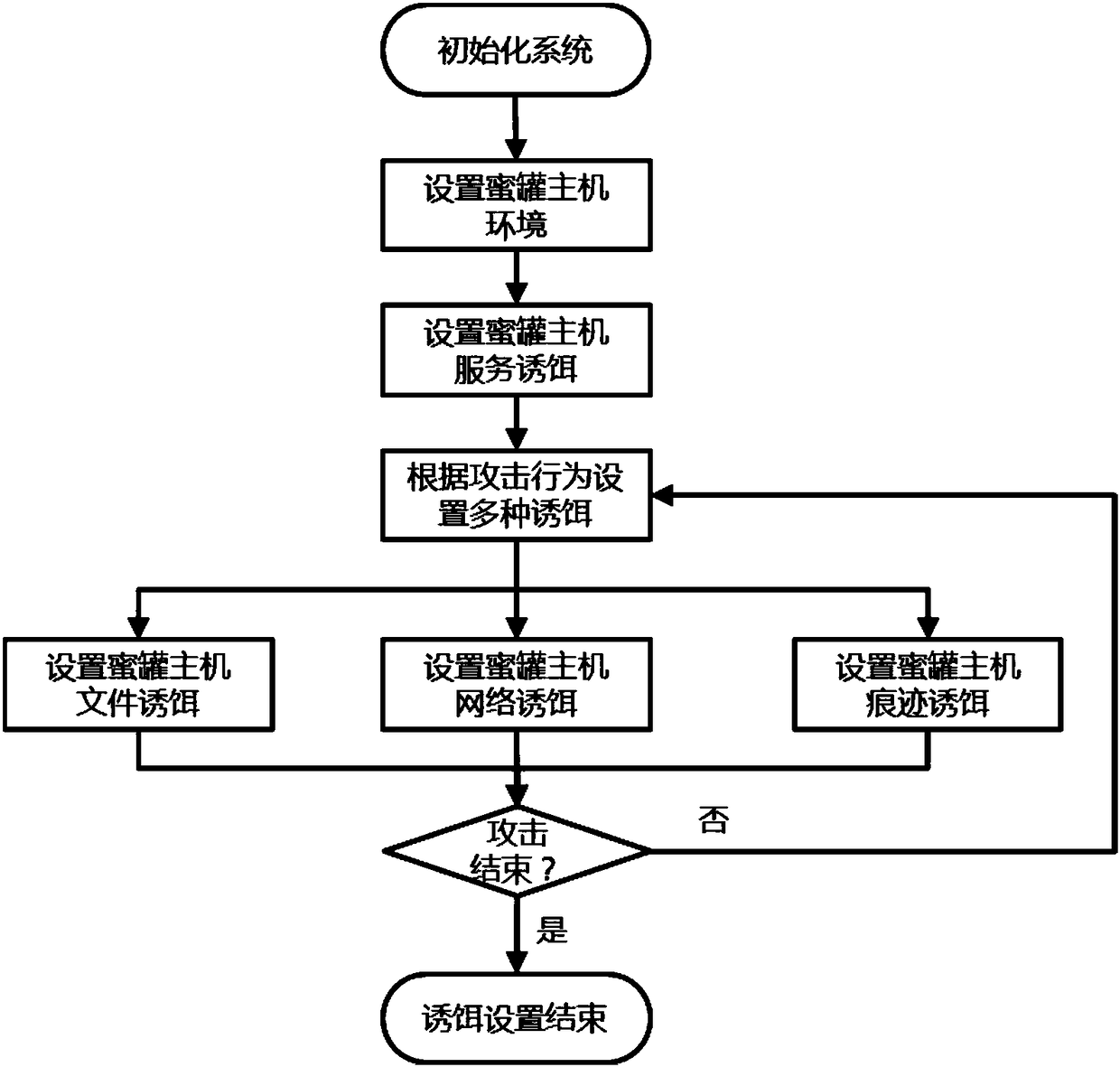
[0038] This embodiment is modified on the basis of the first embodiment. see figure 1 and figure 2 , a multi-dimensional deception decoy implementation system based on honeypot technology, including a honeypot host 1, a honeypot environment deployment module 2, an attack behavior processing analysis module 3 and a decoy deployment module 4, and an attack behavior acquisition module is set in the honeypot host 1 101 and a honeypot, wherein the honeypot includes a service bait 102, a file bait 103, a network bait 104 and a trace bait 105;
[0039] The honeypot environment deployment module 2 is connected to the honeypot host 1, the attack behavior acquisition module 101 is connected to the attack behavior processing and analysis module 3, and the attack behavior processing and analysis module 3 is connected to the decoy deployment Module 4, the decoy deployment module 4 is connected to the honeypot.
[0040] In this preferred embodiment, the honeypot host 1 is dynamically pr...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More