Traffic stealing account identification method and device
An identification method and account technology, applied in the field of communication, can solve problems such as low processing efficiency, inability to detect in advance, lack of classification and judgment rules, etc., to achieve the effect of narrowing the scope of analysis, reducing the possibility, and high processing efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0043] The specific embodiments of the present invention will be further described below in conjunction with the accompanying drawings. The following examples are only used to illustrate the technical solution of the present invention more clearly, but not to limit the protection scope of the present invention.
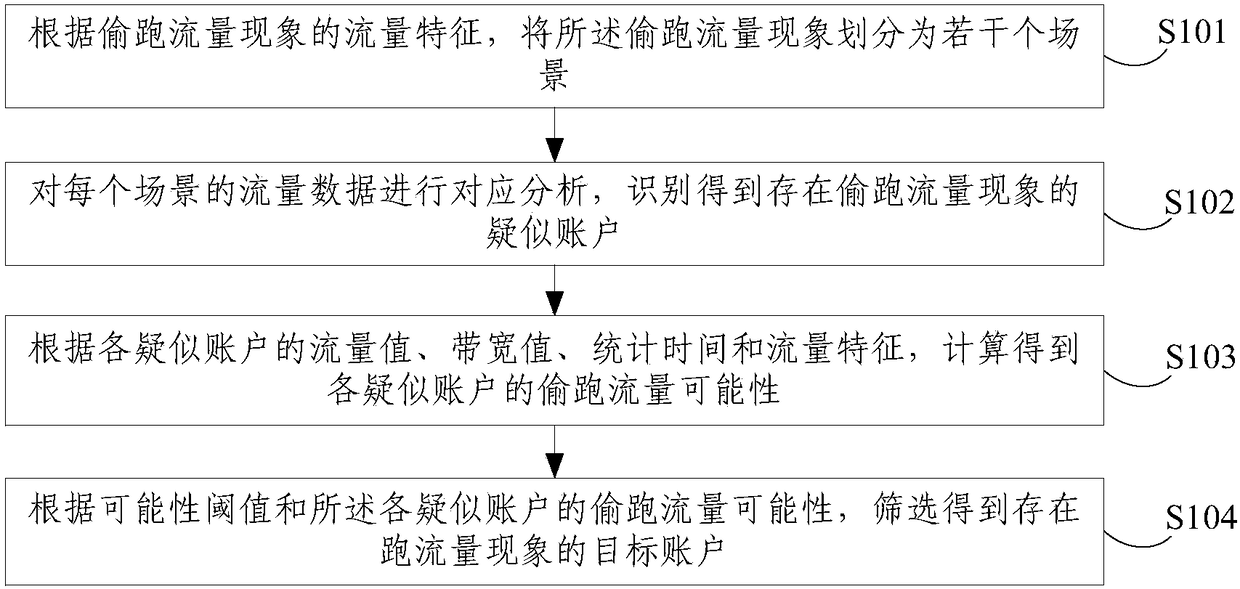
[0044] figure 1 It shows a schematic flowchart of a method for identifying stolen traffic accounts provided by this embodiment, including:
[0045] S101. Divide the sneaking traffic phenomenon into several scenarios according to traffic characteristics of the sneaking traffic phenomenon.
[0046] Wherein, the traffic characteristics include short-term bandwidth, data volume, traffic duration, traffic type, and different distributions of uplink and downlink traffic.
[0047] The scenario is a classification of sneak traffic phenomena according to different traffic characteristics, for example: sneak traffic phenomena caused by terminal function failures.
[0048] S1...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More