Verifiable and secure privacy amplification method based on quantum key distribution
A quantum key distribution, security and confidentiality technology, applied in the field of verifiable security and confidentiality enhancement, to achieve the effect of easy realization
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033] The present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
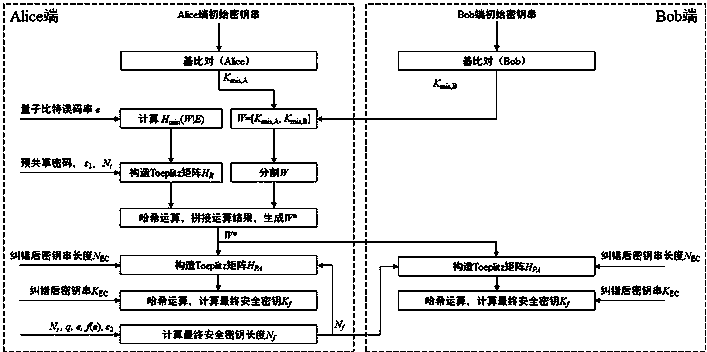
[0034] Such as figure 1 As shown, a verifiable security enhancement method for quantum key distribution of the present invention, the steps are:
[0035] S1: Generate an initial random number string W , the communication parties (Alice and Bob) respectively generate random number strings in the base comparison process of quantum key distribution K mis,A and K mis,B , then Alice combines the two into a random number string W =[ K mis,A , K mis,B ]:
[0036] S101: During the base comparison process of quantum key distribution, when the base selections of Alice and Bob are opposite to each other, the two parties respectively save the random bit strings detected at this time, expressed as K mis,A and K mis,B ;
[0037] S102: Bob will K mis,B Send to Alice;
[0038] S103: Alice's random number string K mis,A and K mi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More