Terminal equipment access authentication method and system based on edge computing
A technology of edge computing and terminal equipment, applied in transmission systems, electrical components, etc., can solve problems such as limited computing and storage capabilities, low cost, and limited energy consumption
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0047] The technical solution of the present invention will be further described in detail below in conjunction with the accompanying drawings, but the protection scope of the present invention is not limited to the following description.
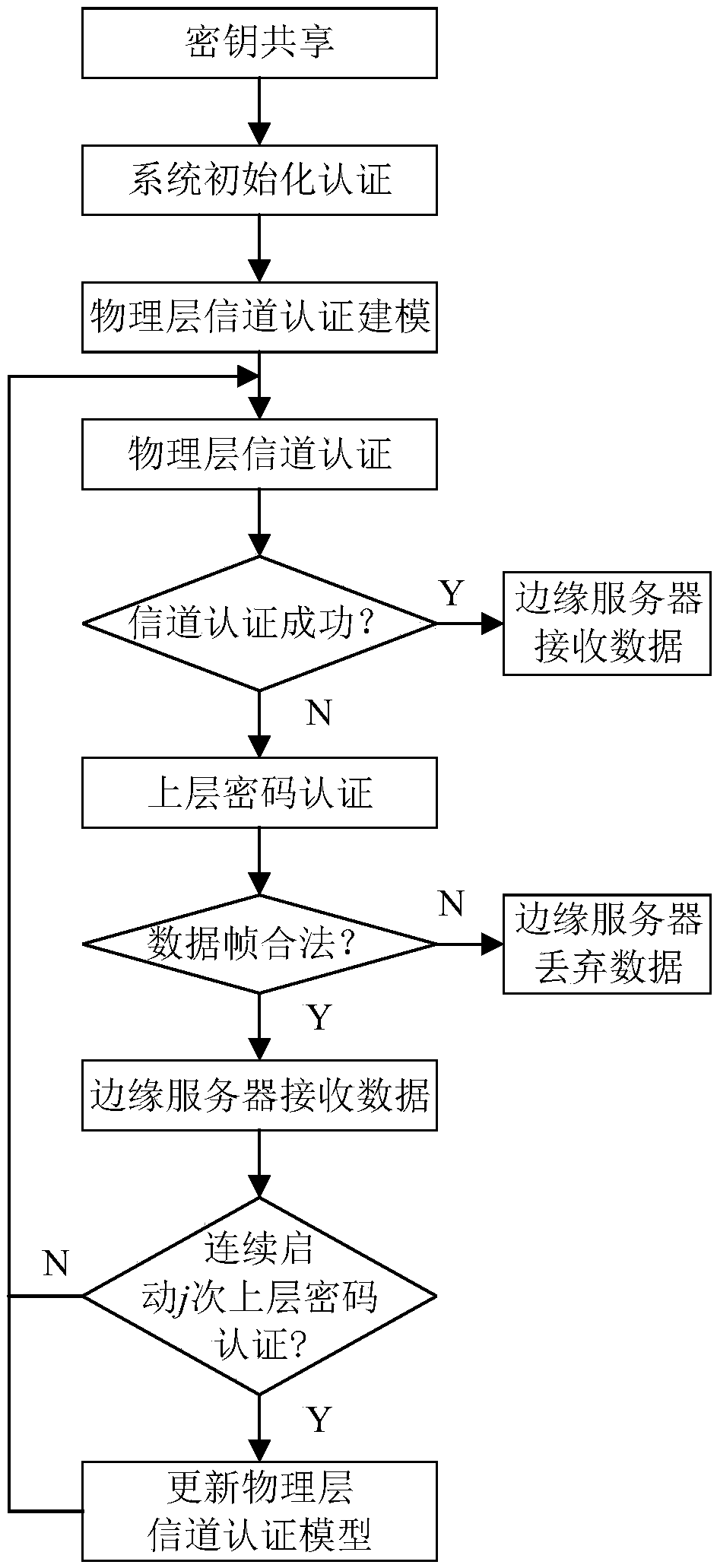
[0048] Such as figure 1 As shown, a terminal device access authentication method based on edge computing includes the following steps:
[0049]S1. Key sharing: the key is shared between the terminal device and the edge computing server through a secure channel;
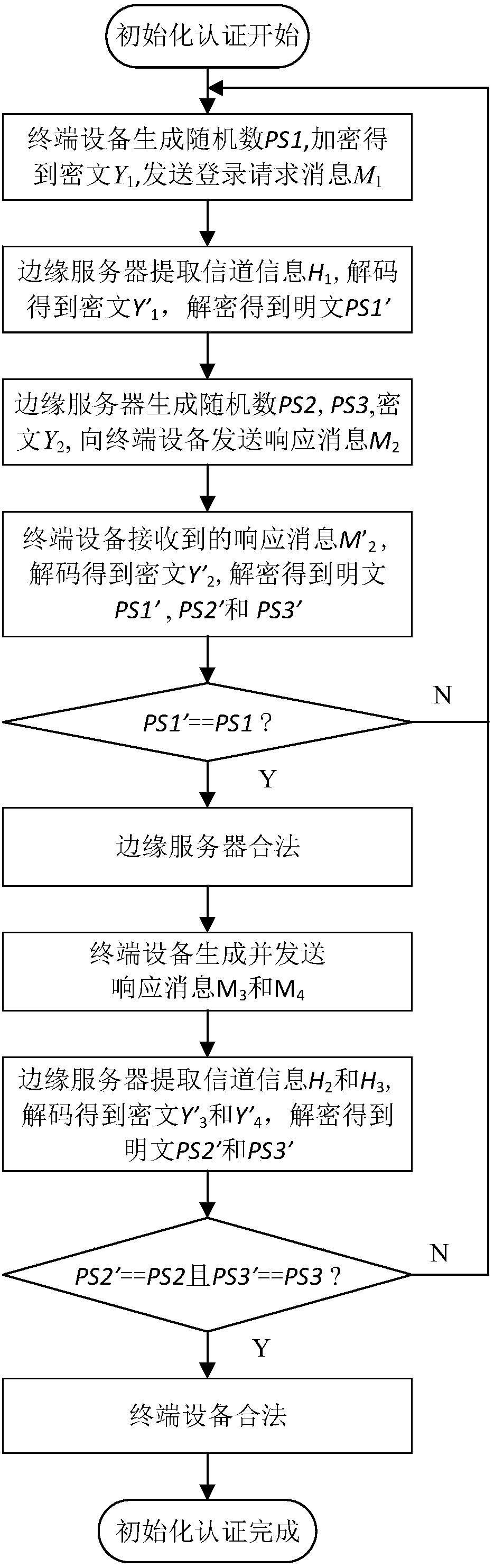
[0050] S2. System initialization authentication: The terminal device and the edge computing server complete mutual initial identity authentication through a lightweight cryptographic algorithm according to the key Key;
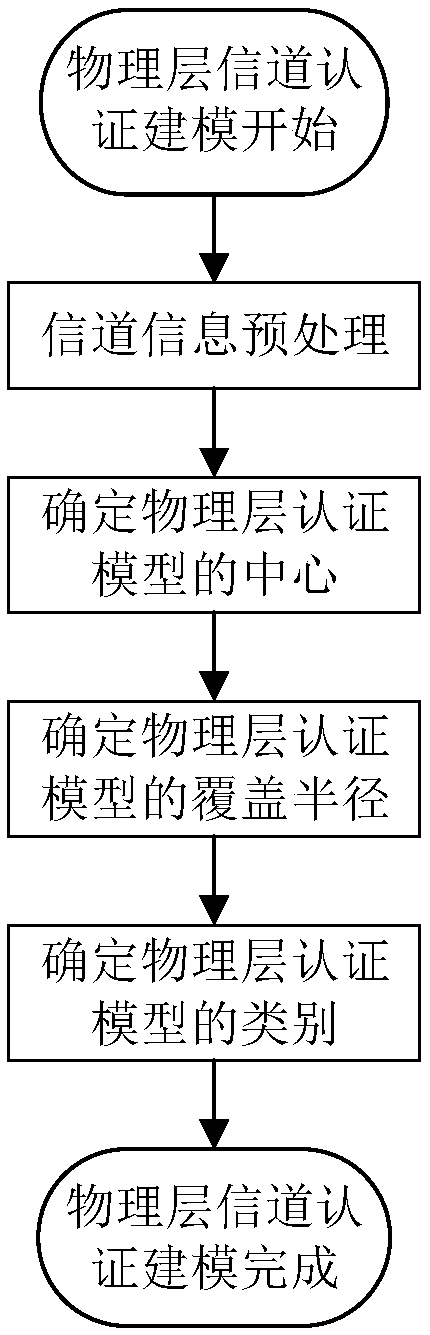
[0051] S3. Physical layer channel authentication modeling: the edge computing server establishes a physical layer channel authentication model based on the channel information collected during coherent time;
[0052] S4. Physical layer channel authentication: Acc...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More