Acoustic wave communication method
A communication method, sound wave technology, applied in the field of sound wave communication, can solve the problems of information transmission loss, vulnerability to environmental influence, user loss, etc., and achieve the effect of simple encryption and decryption method, increased difficulty of cracking, and good use effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
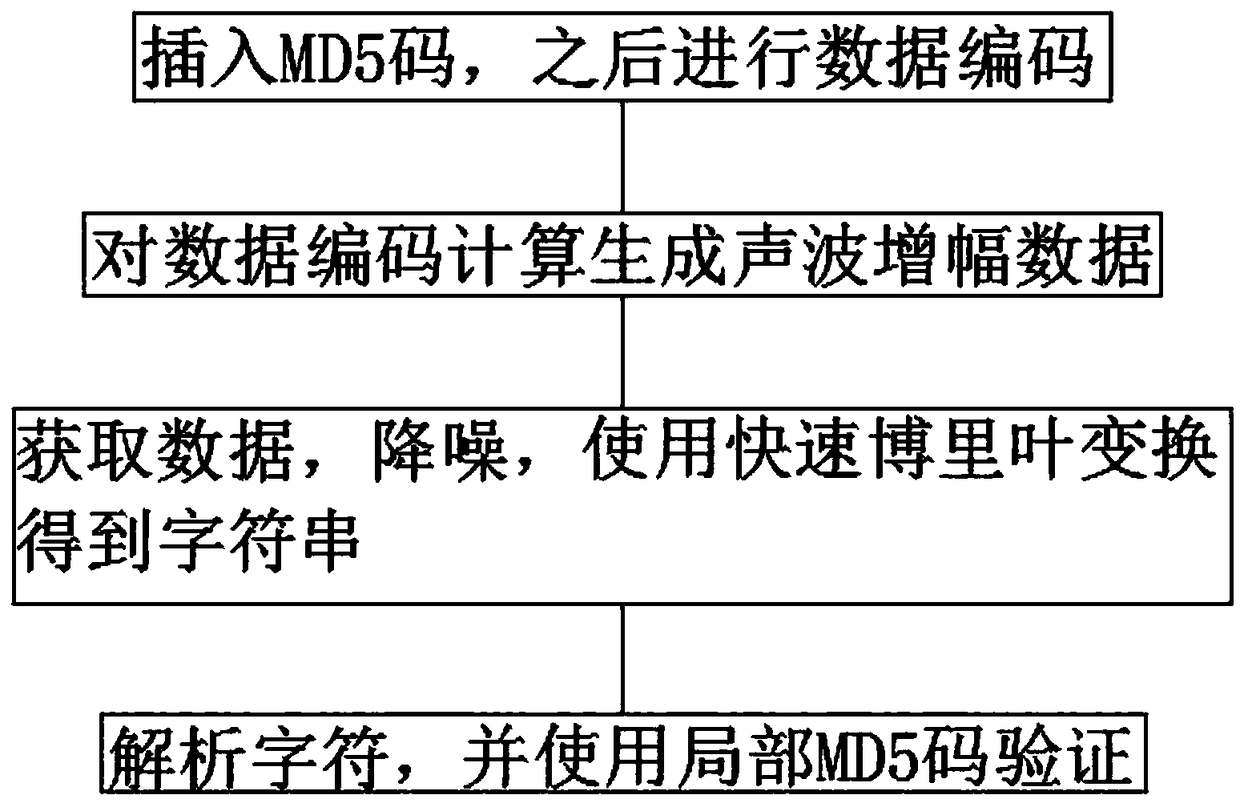
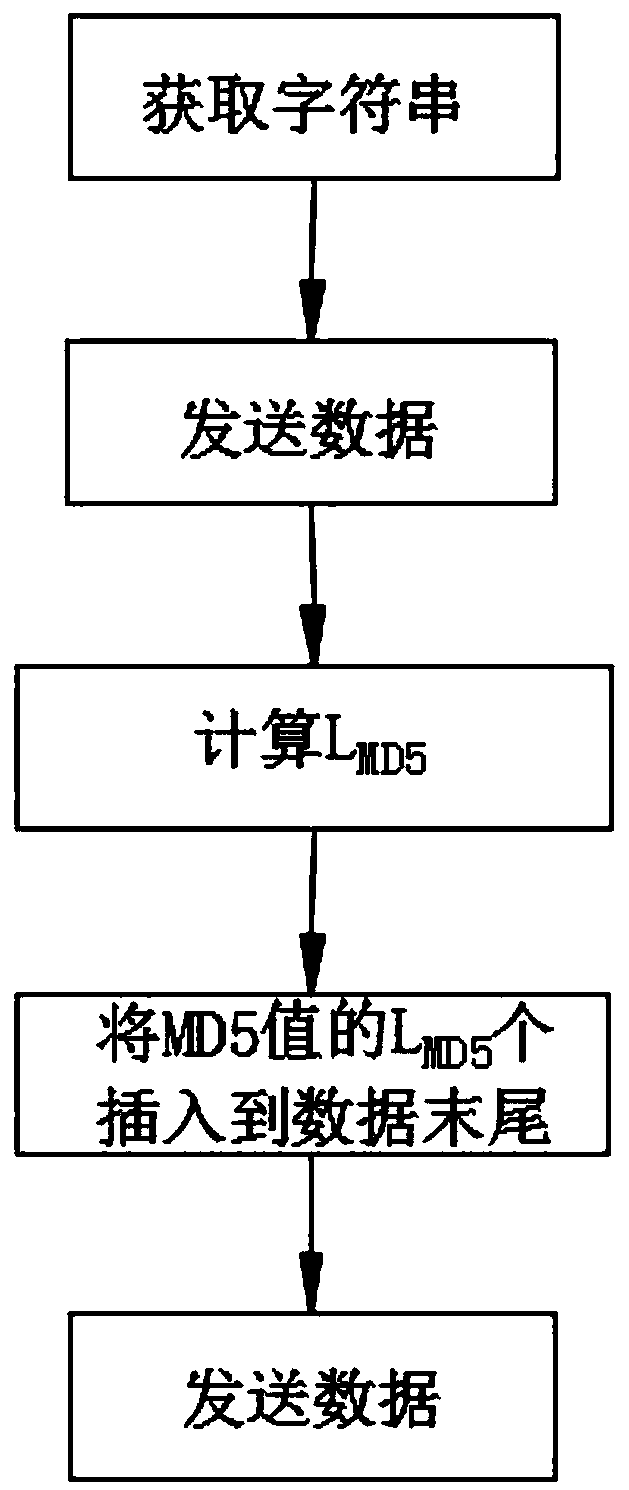
[0024] (1) Obtain the data to be transmitted, insert the MD5 code, and encode the data. First, check whether the data to be transmitted has illegal characters to ensure a valid character string. Then, preprocess the character string. The string is compressed, and finally, the acoustic amplitude data of the processed data is generated;
[0025] (2), calculate the amplification of each sound wave in the data encoding obtained in step (1), then superimpose to generate sound wave amplification data, and transmit, the amplitude data detection range is -32768-32767, after each transmission of 1 character Add an interruption time, the interruption time is 0.3s;
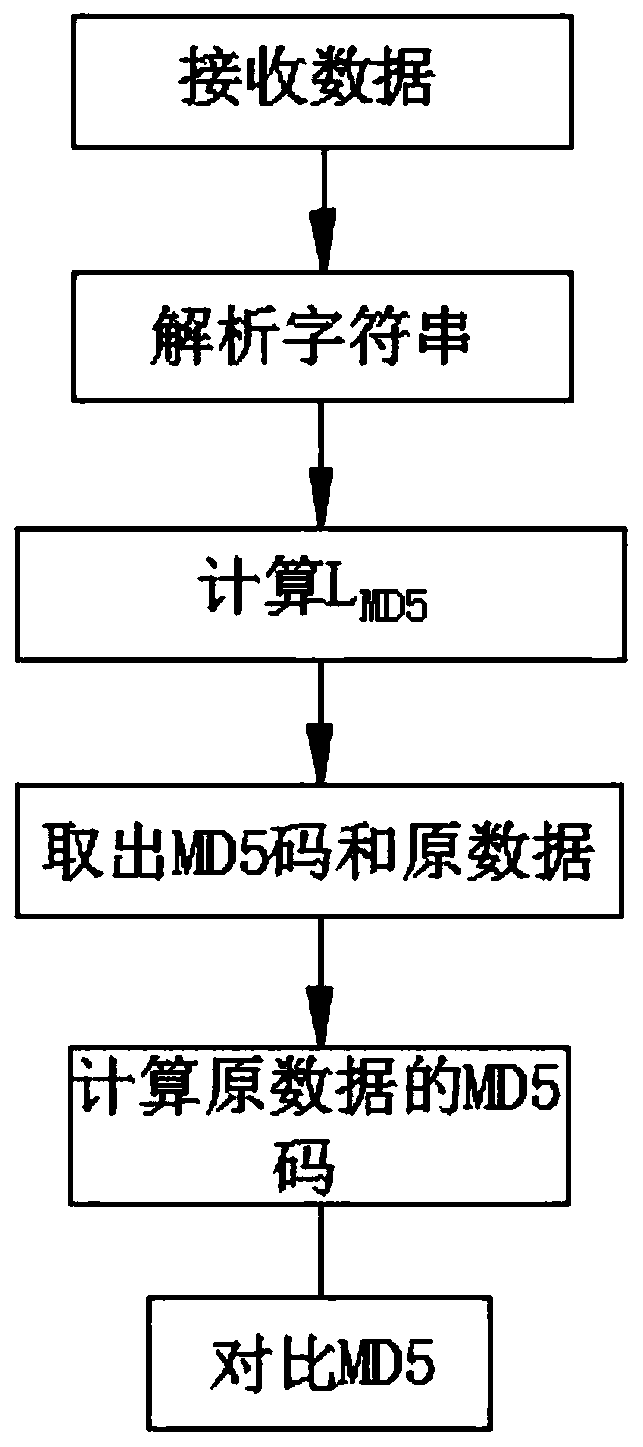
[0026] (3) Distribute the key through the central server, establish a secure channel, change the key randomly, and establish a secure channel to obtain the sound wave amplification data after noise reduction and interference. Second, use the fast Fourier transform calculation method, and then use the fast Fourier transform ...
Embodiment 2
[0034] (1) Obtain the data to be transmitted, insert the MD5 code, and encode the data. First, check whether the data to be transmitted has illegal characters to ensure a valid character string. Then, preprocess the character string. The string is compressed, and finally, the acoustic amplitude data of the processed data is generated;
[0035] (2), calculate the amplification of each sound wave in the data encoding obtained in step (1), then superimpose to generate sound wave amplification data, and transmit, the amplitude data detection range is -32768-32767, after each transmission of 1 character Add an interruption time, the interruption time is 0.3s;
[0036] (3) Distribute the key through the central server, establish a secure channel, change the key randomly, and establish a secure channel to obtain the sound wave amplification data after noise reduction and interference. Second, use the fast Fourier transform calculation method, and then use the fast Fourier transform ...
Embodiment 3
[0041] (1) Obtain the data to be transmitted, insert the MD5 code, and encode the data. First, check whether the data to be transmitted has illegal characters to ensure a valid character string. Then, preprocess the character string. The string is compressed, and finally, the acoustic amplitude data of the processed data is generated;
[0042](2), calculate the amplification of each sound wave in the data encoding obtained in step (1), then superimpose to generate sound wave amplification data, and transmit, the amplitude data detection range is -32768-32767, after each transmission of 1 character Add an interruption time, the interruption time is 0.3s;
[0043] (3) Distribute the key through the central server, establish a secure channel, change the key randomly, and establish a secure channel to obtain the sound wave amplification data after noise reduction and interference. Second, use the fast Fourier transform calculation method, and then use the fast Fourier transform t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More