Data tamper-proofing method, system and equipment based on base station information and storage medium
A base station information and anti-tampering technology, applied in the field of network security, can solve problems such as lagging of data acquisition points, bypassing of profit-seeking in the used dimension, failure to achieve defense, etc., to improve real-time performance, improve access security, and have a wide range of applications Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] Example embodiments will now be described more fully with reference to the accompanying drawings. Example embodiments may, however, be embodied in many forms and should not be construed as limited to the embodiments set forth herein. Rather, these embodiments are provided so that this disclosure will be thorough and complete, and will fully convey the concept of the example embodiments to those skilled in the art. The same reference numerals denote the same or similar structures in the drawings, and thus their repeated descriptions will be omitted.
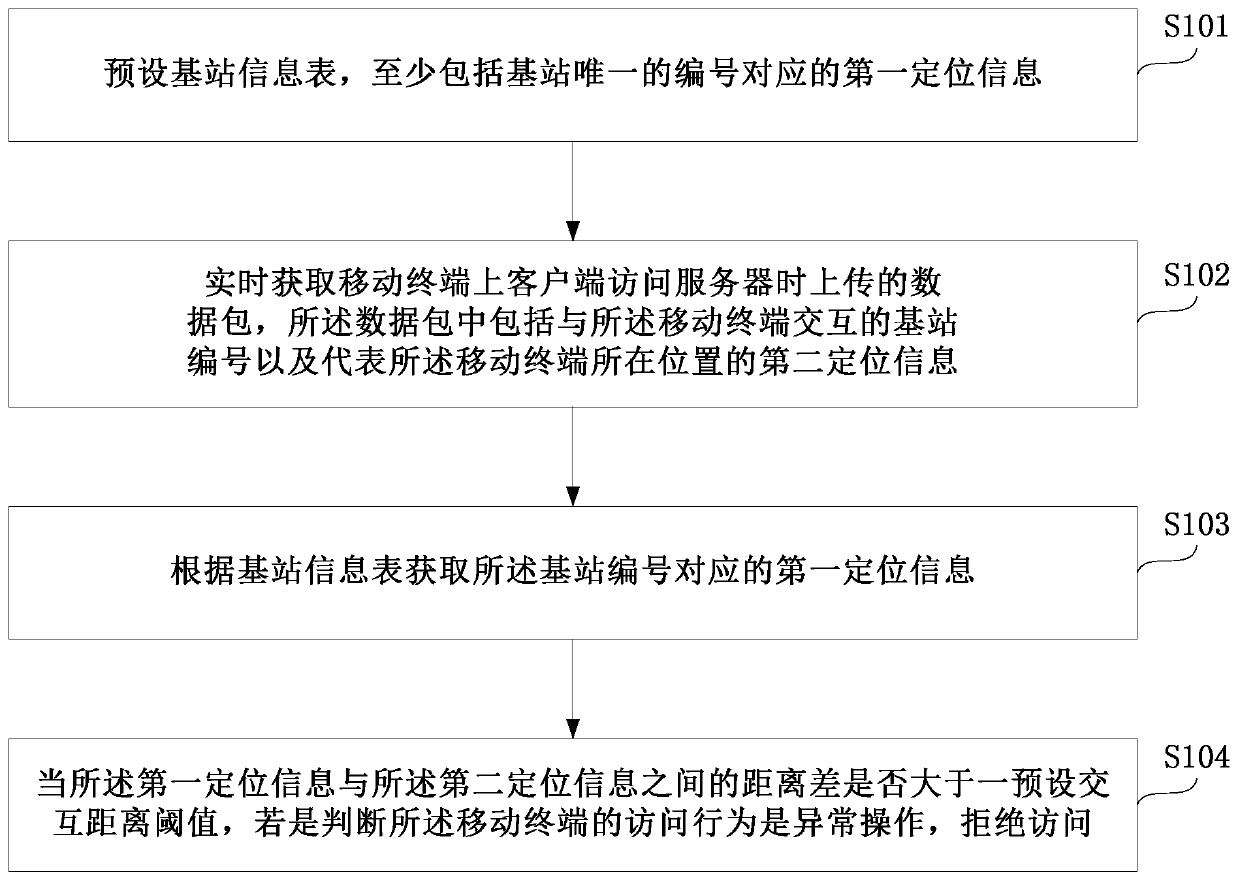
[0040] figure 1 It is a flow chart of the data tamper-proof method based on base station information in the present invention. Such as figure 1 As shown, the data tamper-proof method based on base station information of the present invention comprises the following steps:
[0041] S101. The preset base station information table includes at least first positioning information corresponding to the unique number of the bas...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap