A node access and node authentication method based on edge computing
An edge computing and access method technology, applied to public keys for secure communication, user identity/authority verification, and key distribution, can solve problems such as user data and privacy threats, achieve enhanced security and reliability, and improve verification Efficiency, the effect of avoiding leakage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0032] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention clearer, the technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the drawings in the embodiments of the present invention. Obviously, the described embodiments It is a part of embodiments of the present invention, but not all embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without making creative efforts belong to the protection scope of the present invention.
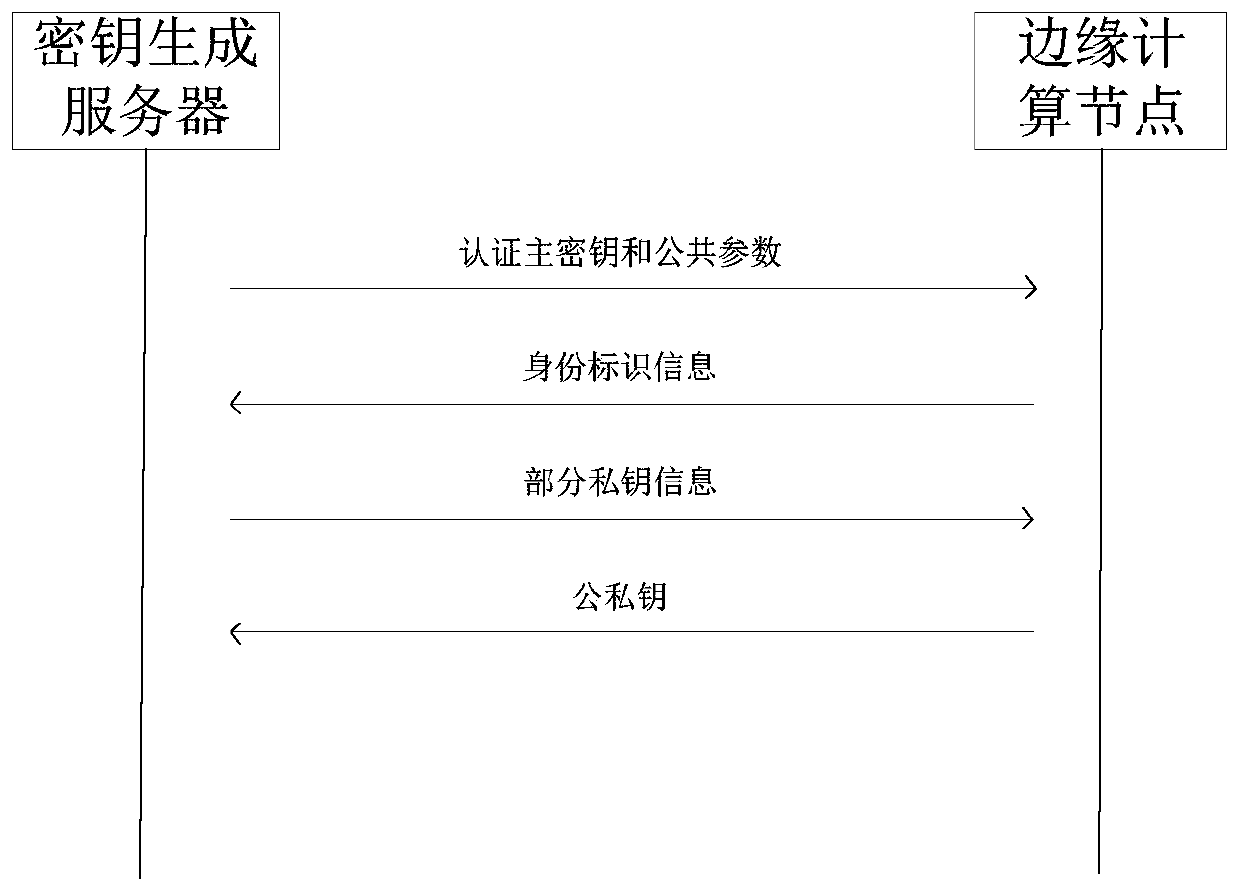
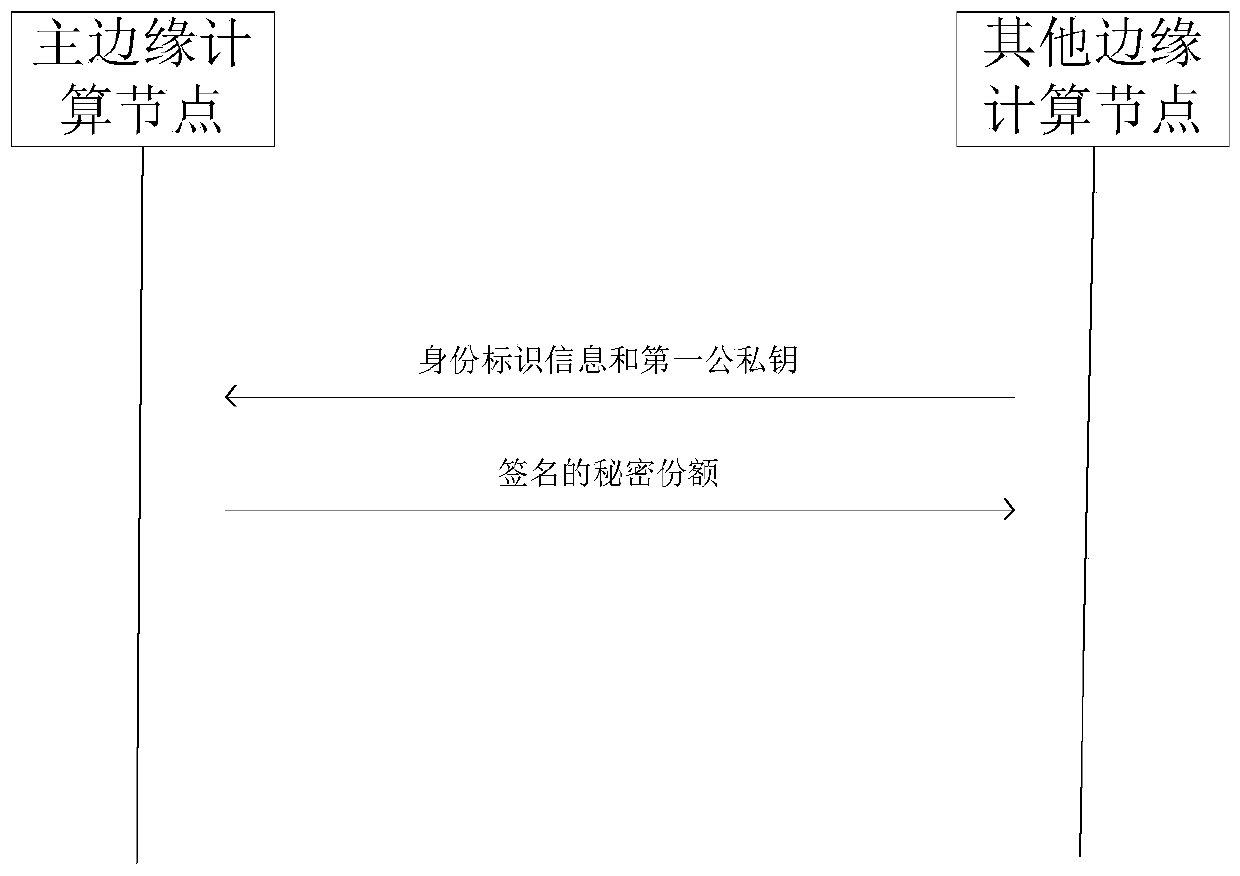
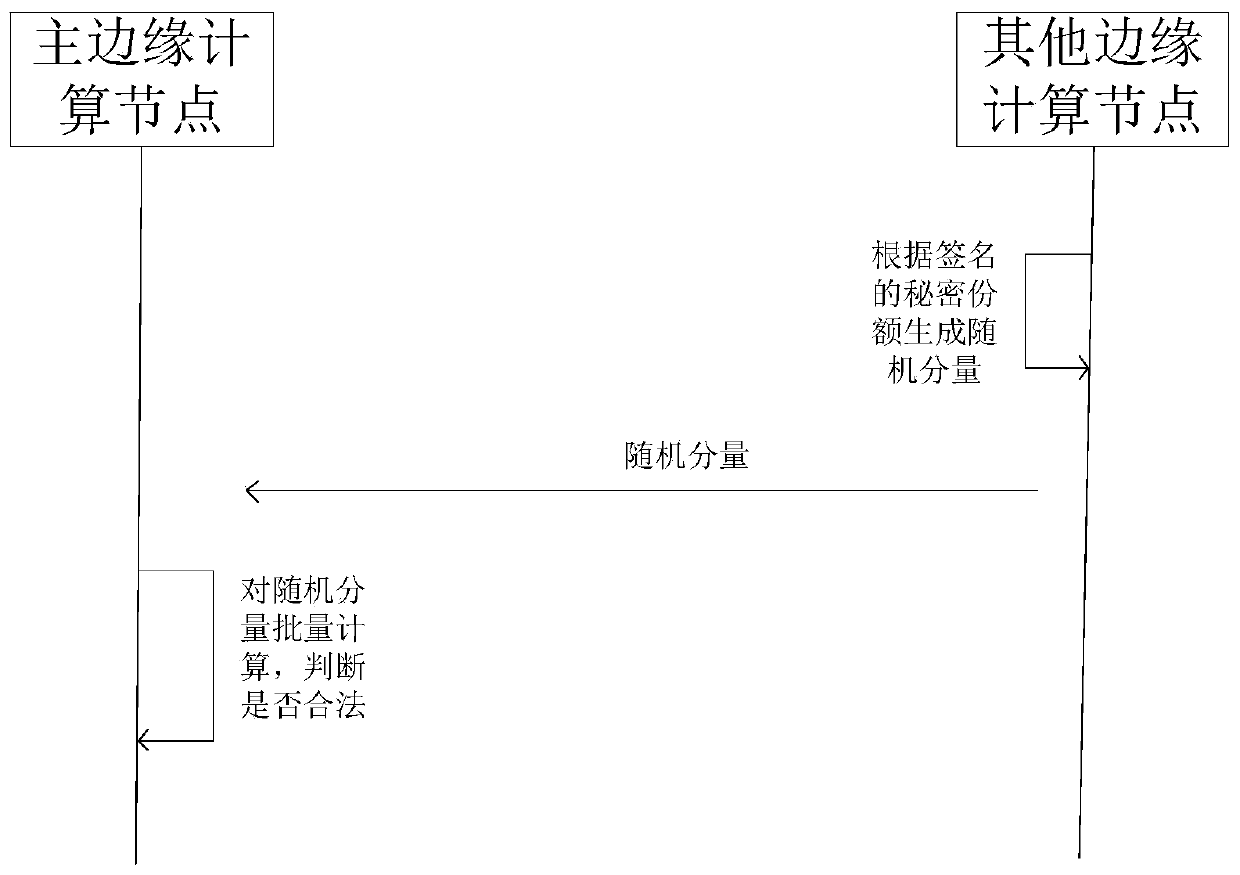
[0033] An embodiment of the present invention provides a node access and node authentication method based on edge computing, such as figure 1Shown is a schematic diagram of an application scenario of an embodiment of the present invention. The key generation server generates the authentication master key and public parameters according to the security p...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More