Secure cloud storage method based on SGX
A technology of cloud storage and cloud storage services, applied in the field of secure cloud storage based on SGX, can solve problems such as trusted authentication and key encapsulation, and achieve the effect of increasing difficulty, ensuring integrity and confidentiality, and ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
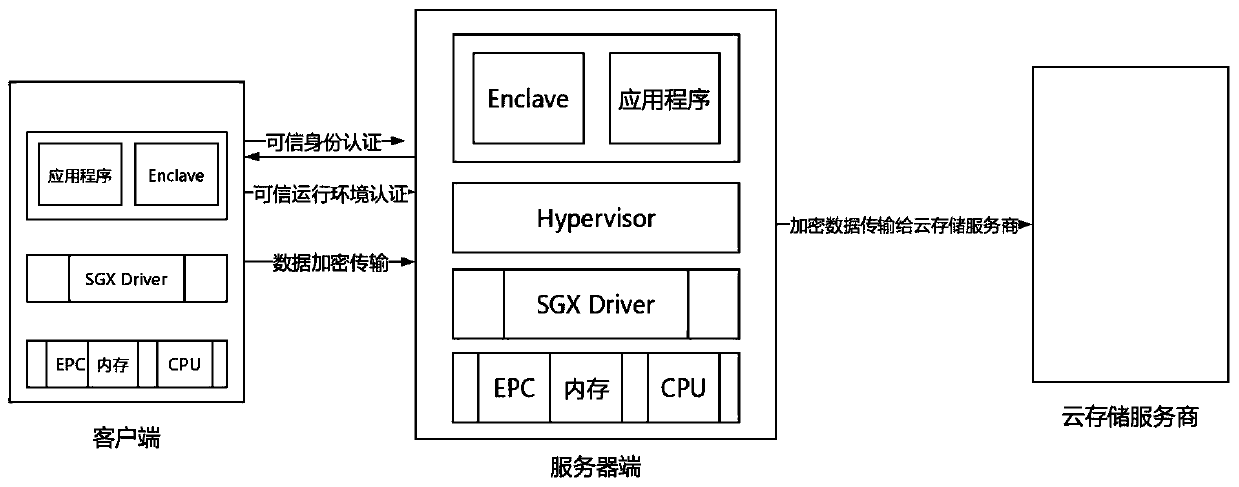
[0038] The SGX-based secure cloud storage method provided in this embodiment is applicable to a system based on the SGX-based client / server architecture, and the method includes:
[0039] A1. Trusted identity authentication steps: the client performs two-way authentication of the trusted identity with the server through the trusted identity authentication module of the server, and after completing the trusted identity authentication, the client establishes a session with the server.
[0040]The server receives the client's identity authentication request, calls the enclave's identity information and authentication request to the application enclave, and the application enclave calls the EREPORT command to generate a REPORT for the identity information and authentication request, and then uses the enclave's report key to generate a REPORT MAC, together with REPORT, is sent to the reference enclave. Refer to the enclave to verify its integrity and whether the enclave is in the s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More