Internet of Things security agent data sharing module design method adopting a block chain technology
A security proxy and data sharing technology, which is applied in the field of IoT security proxy data sharing module design using blockchain technology, and can solve problems such as using revocation users and cloud server collusion attacks.
Active Publication Date: 2019-09-20
HANGZHOU YUNXIANG NETWORK TECH
View PDF23 Cites 10 Cited by
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
In order to ensure effective data sharing and user revocation, some scholars have proposed a system model using key policy-based attribute encryption and proxy re-encryption, however, this model is vulnerable to collusion attacks using revoked users and cloud servers
Method used
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
View moreImage
Smart Image Click on the blue labels to locate them in the text.
Smart ImageViewing Examples
Examples
Experimental program
Comparison scheme
Effect test
specific Embodiment
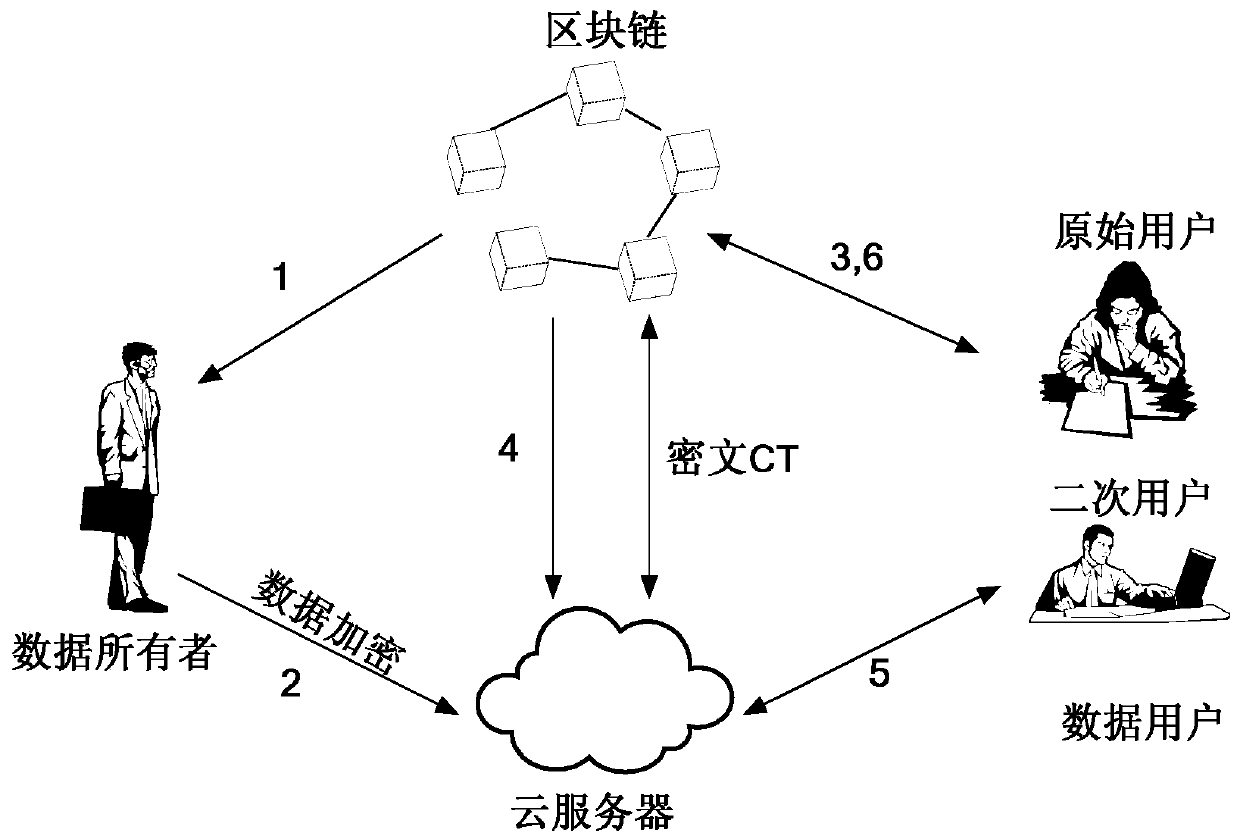
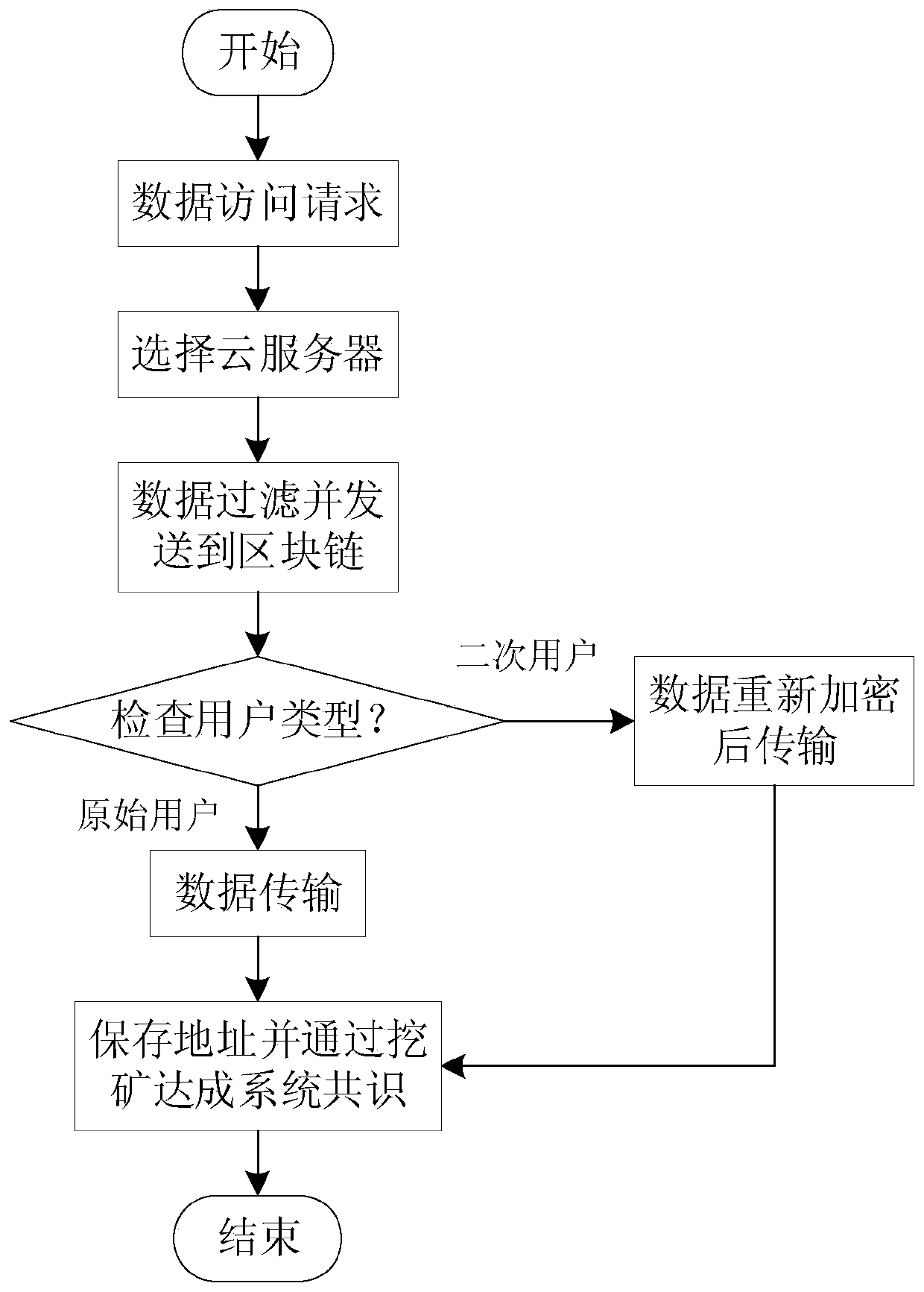
[0097] Such as figure 1 As shown, the Internet of Things data security sharing system of the present invention includes a blockchain network, a cloud server, a data owner and a data user. The data owner refers to the entity whose data is to be accessed, and the data can only be accessed when the private key of the data user corresponds to the attribute set specified by the data owner; the data user refers to the entity whose data is used by the system, and the data owner Both users and data users need to make predictions on the blockchain. The cloud server is a data repository, and all encrypted files are sent to the server through a secure channel.
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More PUM
 Login to View More
Login to View More Abstract
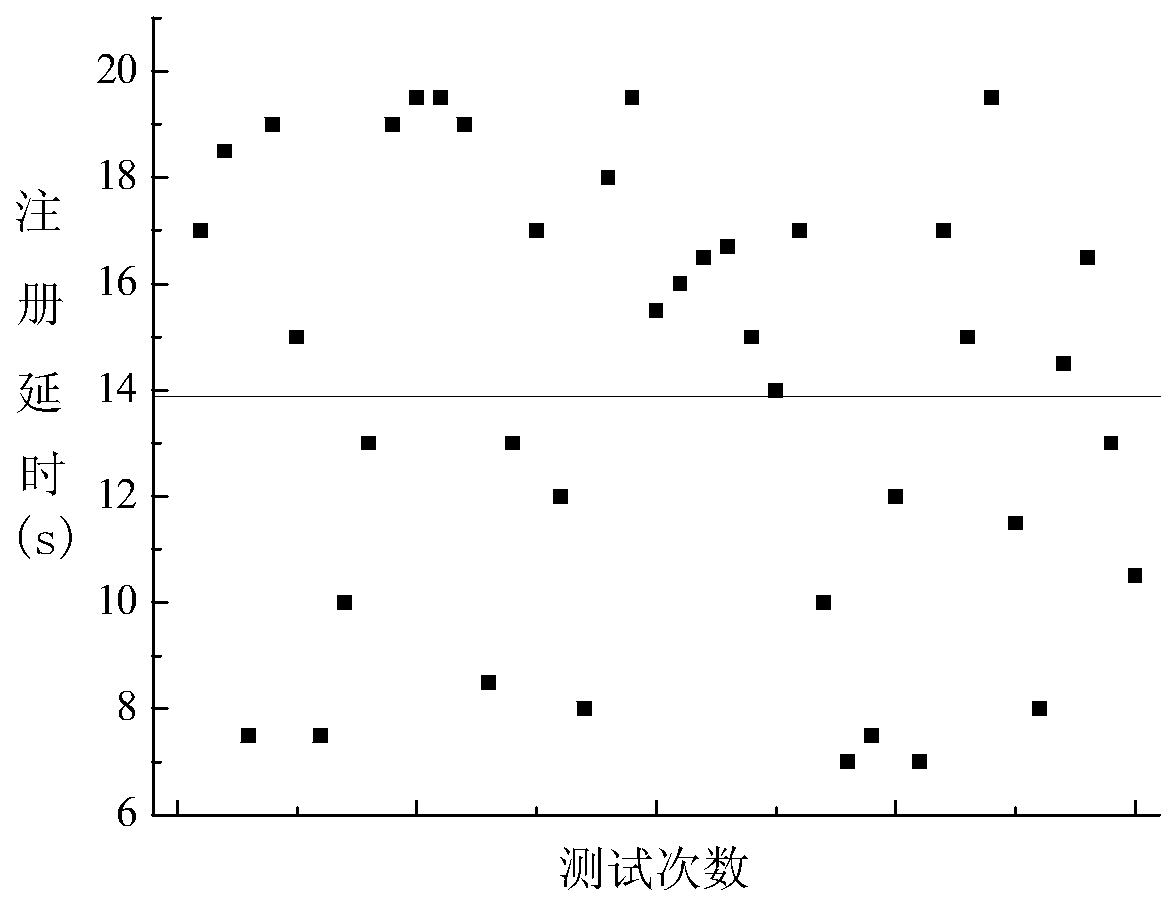
The invention discloses an Internet of Things security agent data sharing module design method adopting a block chain technology. A block chain network is integrated; a processing node serves as a proxy server; when the user is a registered member of the network, verification is carried out through a block chain network, a user can access data, the agent also re-encrypts the data by transforming the policy set during the process of sharing the data, the block chain network and the cloud server work cooperatively, and anti-collaboration scheme is ensured. According to the method and the system, fine-grained access control on the data is further realized, experimental results show that agent re-encryption increases delay, and the use of the block chain records all interactions among entities, so that dependence on a trusted third party is eliminated, and efficient and safe access to Internet of Things data is ensured.
Description
technical field [0001] The invention relates to a design method for a data sharing module of an Internet of Things security agent, in particular to a design method for a data sharing module of an Internet of Things security agent using block chain technology. Background technique [0002] Advances in wireless communication, embedded computing, actuation, and sensing have enabled devices to become interconnected entities in a cyber-physical world, the "Internet of Things." It is estimated that by 2030, the number of devices connected to the Internet will increase significantly compared with today, and the boundary between the physical world and the digital world will be significantly reduced. The Internet of Things is expected to fundamentally change the daily life mode of human beings, forming a new way of free interaction between people and people (H2H), machines and machines (M2M), and people and machines (H2M). The services provided by the Internet of Things that can ens...
Claims
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More Application Information
Patent Timeline
 Login to View More
Login to View More IPC IPC(8): H04L29/06H04L29/08H04L9/32H04L9/08
CPCH04L9/0869H04L9/3271H04L63/0227H04L63/0428H04L63/10H04L63/20H04L67/104
Inventor 黄步添周伟华闫凤喜陈建海杨正清刘振广
Owner HANGZHOU YUNXIANG NETWORK TECH