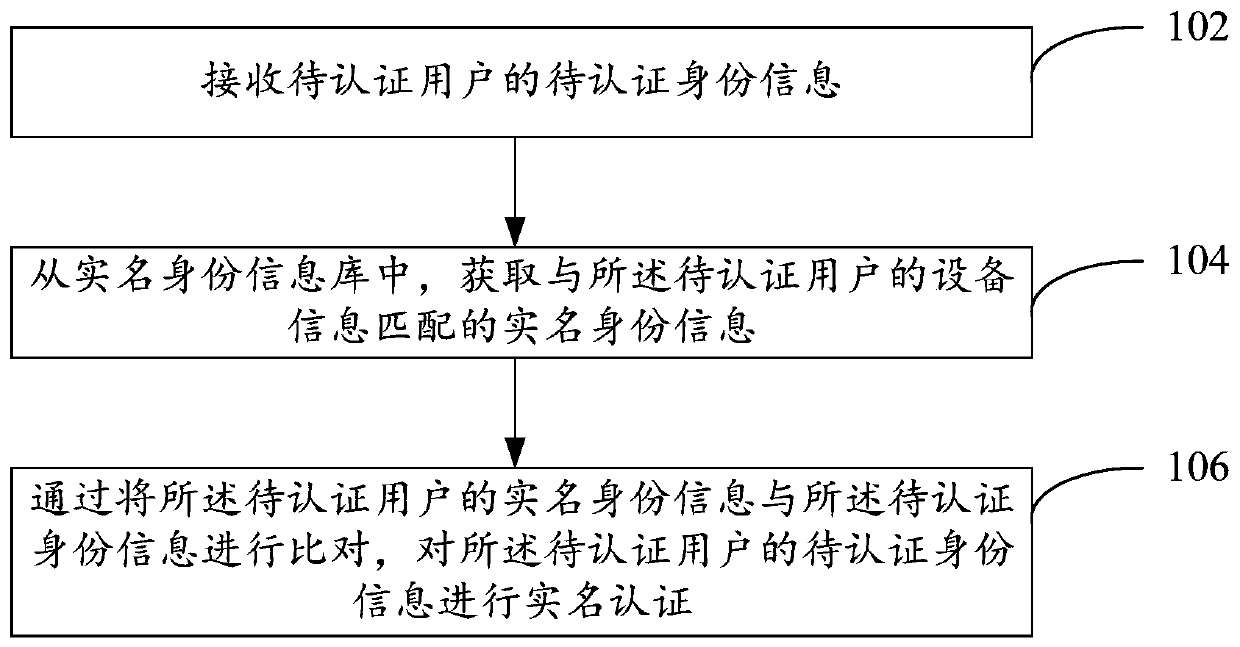
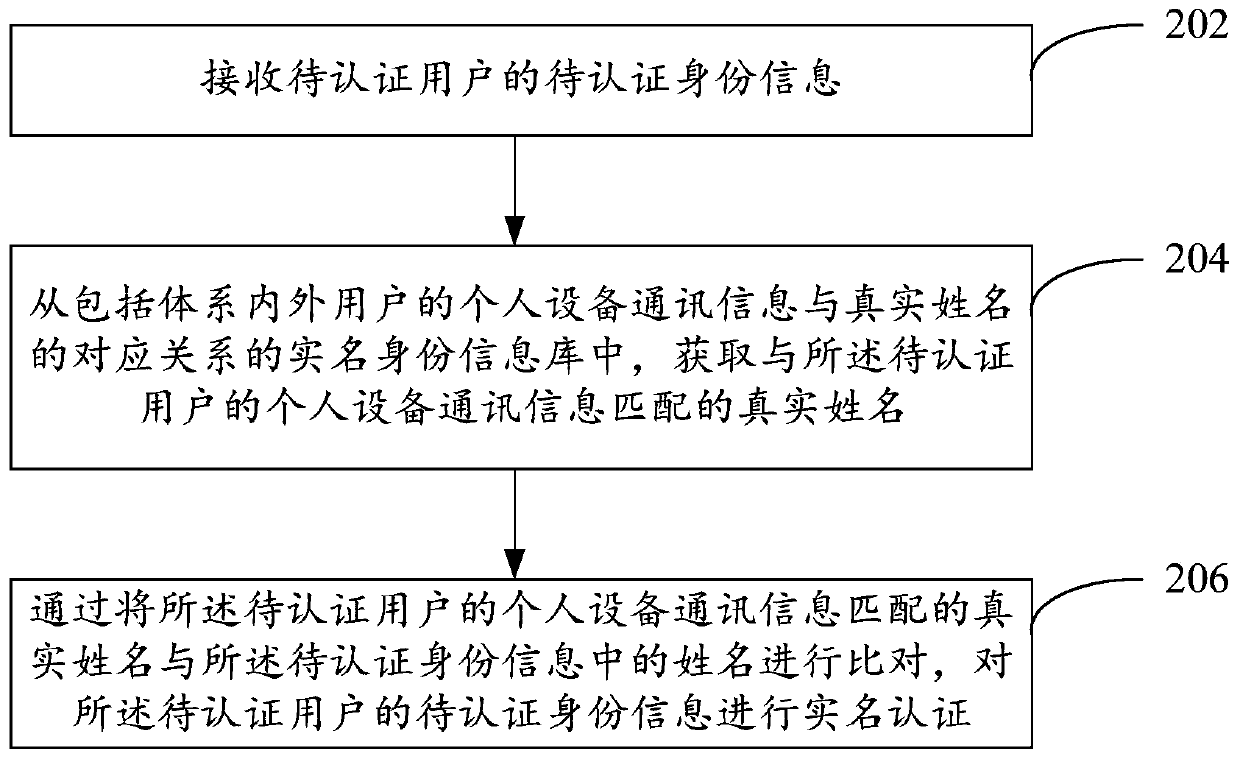
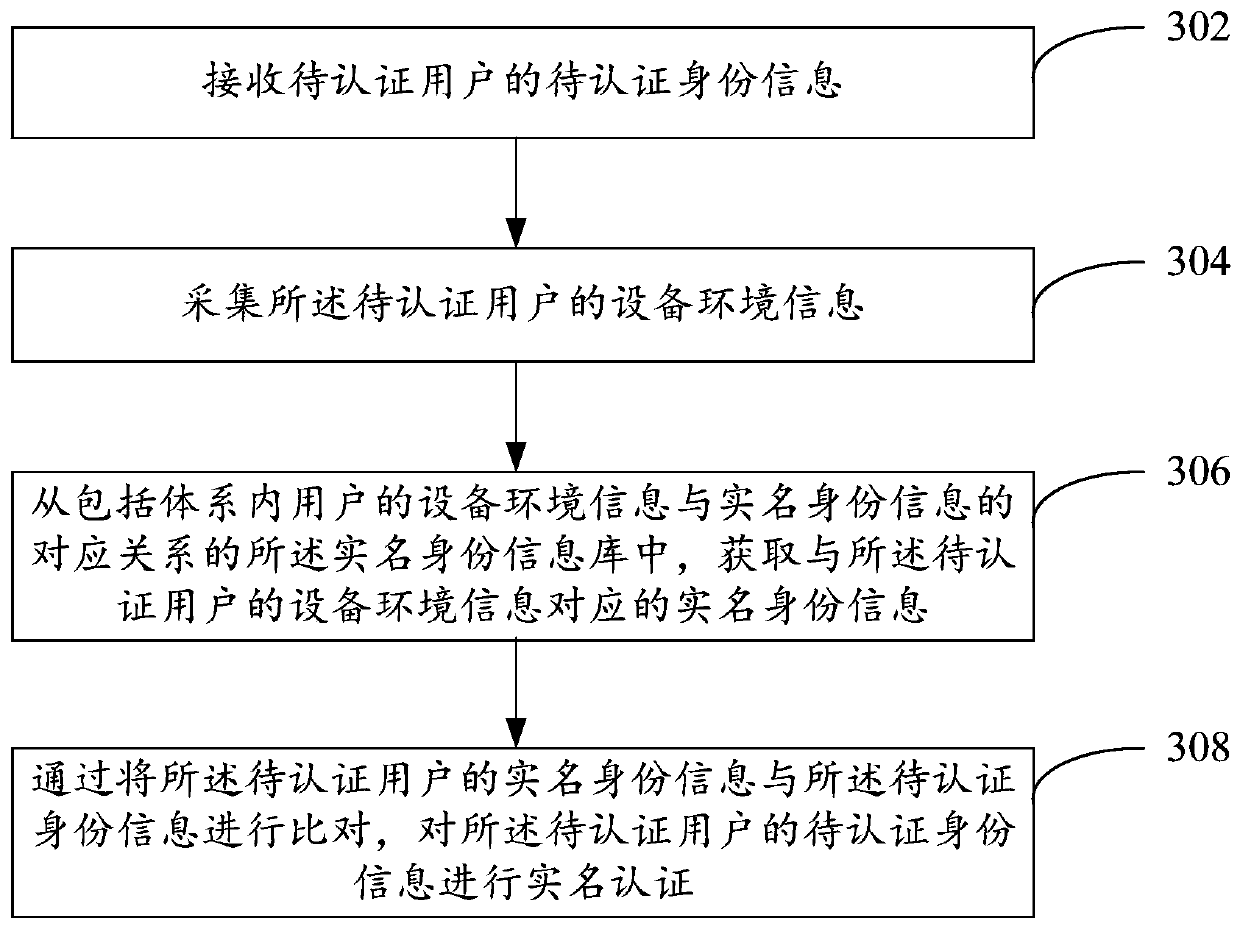
Real-name authentication method and device
A real-name authentication and real-name technology, applied in the computer field, can solve the problems of user trouble, complex authentication process, poor experience, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] In the following description, many specific details are explained in order to fully understand this specification. However, this specification can be implemented in many other ways different from those described herein, and those skilled in the art can make similar promotion without violating the connotation of this specification. Therefore, this specification is not limited by the specific implementation disclosed below.
[0040] The terms used in one or more embodiments of this specification are only for the purpose of describing specific embodiments, and are not intended to limit one or more embodiments of this specification. The singular forms of "a", "said" and "the" used in one or more embodiments of this specification and the appended claims are also intended to include plural forms, unless the context clearly indicates other meanings. It should also be understood that the term "and / or" used in one or more embodiments of this specification refers to and includes any...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More