Book resource access control method based on ciphertext attribute authentication and threshold function
A resource access and control method technology, which is applied in the field of book resource access control based on ciphertext attribute authentication and threshold function, can solve the problems of reducing computing and communication overhead, easily revealing personal identity information, and high information sensitivity, so as to reduce computing and communication overhead, the effect of avoiding collusion attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
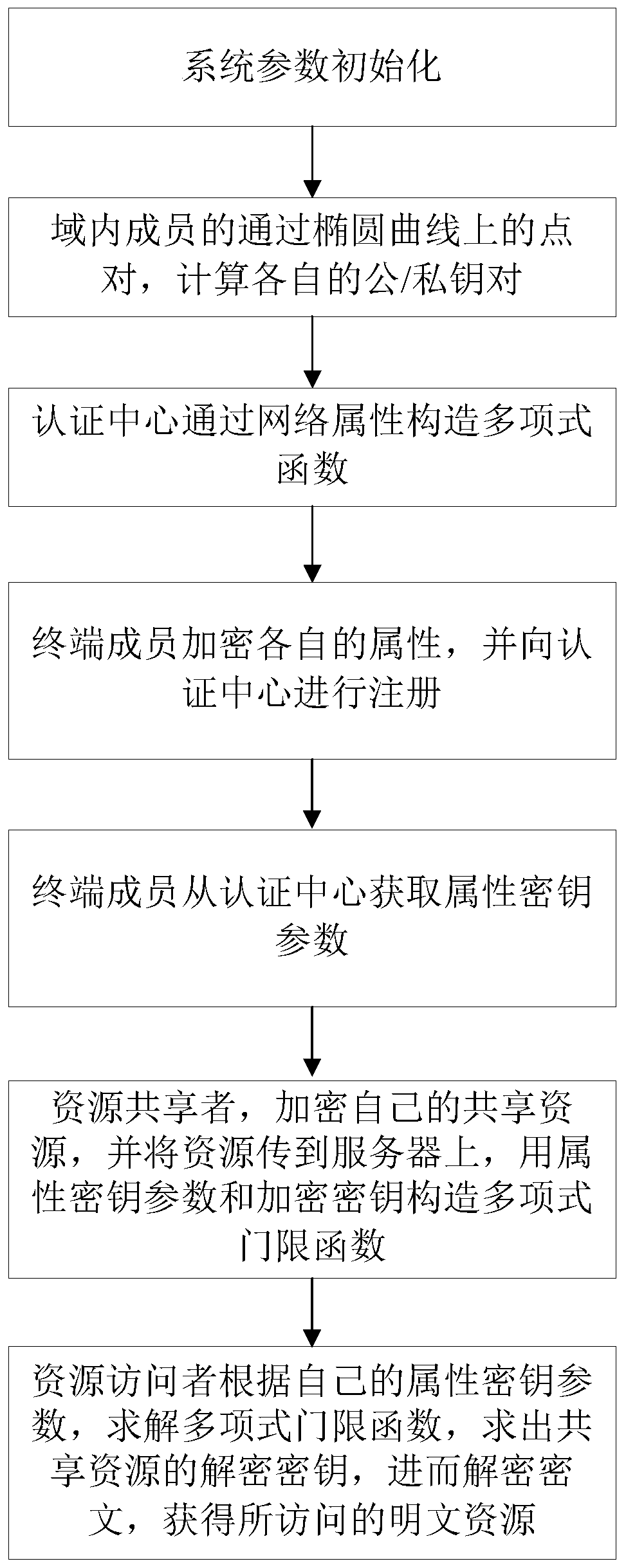
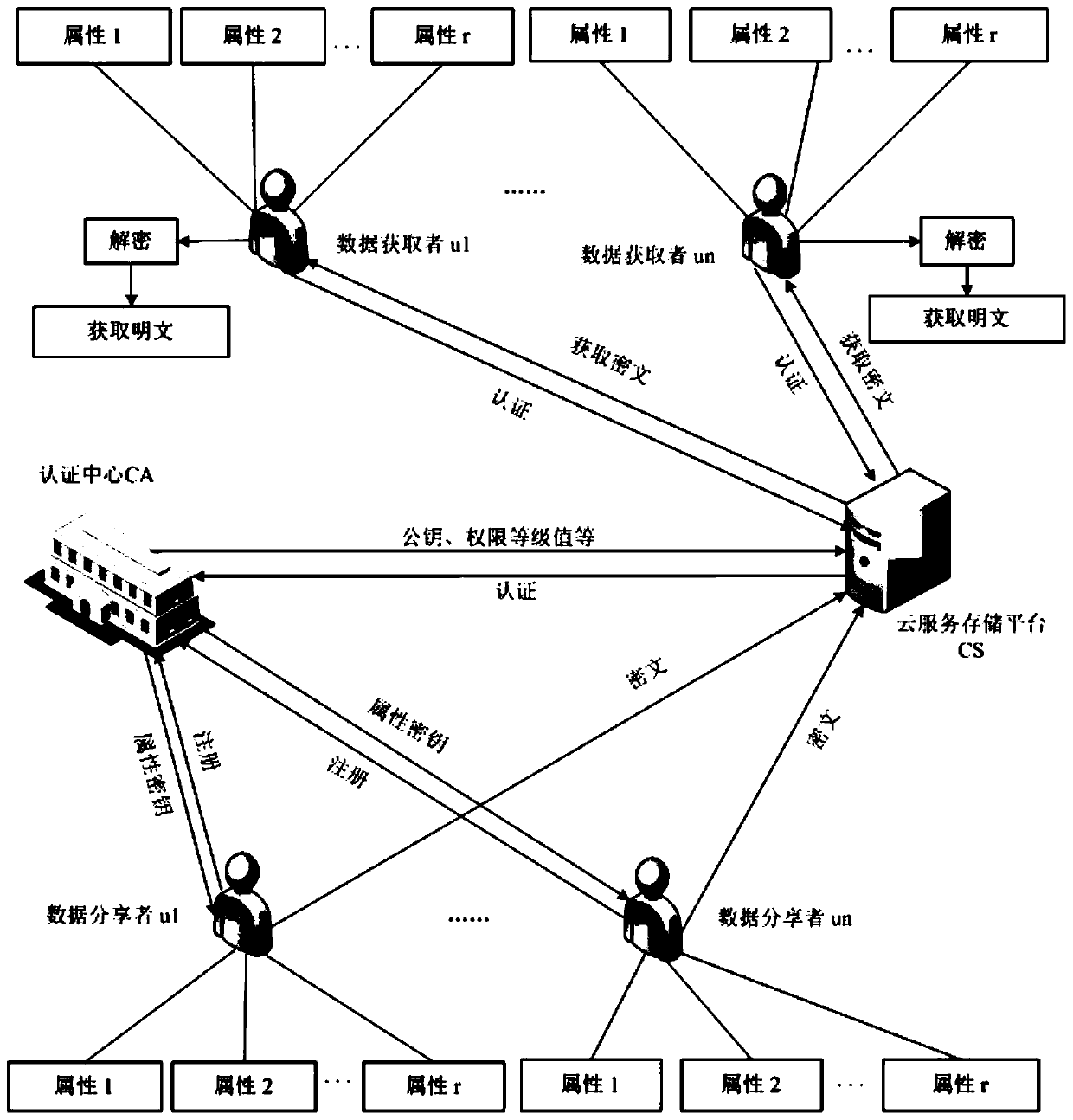
[0063] In the case of complex information sharing, the authentication center in the domain needs to authenticate the identity of the information sharing members, but when providing identity information, the identity information is easily leaked or stolen. For security reasons, while information sharing is multi-party authentication, personal identity privacy needs to be protected. When sharing information, it is also necessary to ensure the confidentiality, integrity and anti-disclosure of communication information, and only authorized members can share information. Aiming at this application background, the present invention proposes a book resource access control method based on ciphertext attribute authentication and threshold function, such as figure 1As shown, the steps are as follows: ① The terminal members participating in the sharing of information resources first perform parameter initialization and generate their own public / private key pairs respectively; Terminal m...
Embodiment 2
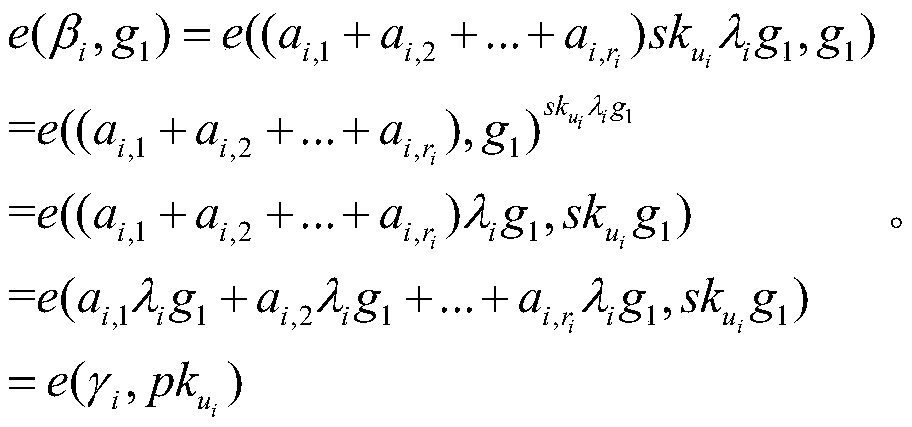
[0090] A book resource access control method based on ciphertext attribute authentication and threshold function, such as figure 1 As shown, in order to illustrate the content and implementation method of the present invention, a specific embodiment is provided. In this embodiment, for the convenience of example description, the maximum number of terminal members participating in information resource sharing is 10, and the entity set of terminal members is expressed as The set of corresponding entity terminal memberships is expressed as The authentication center CA defines the attribute set of all terminal members as Attr={A 1 ,A 2}, terminal member u i The attribute set of (1≤i≤10) is attr i ={a i,1 ,a i,2 ,a i,3}. The purpose of introducing details in this embodiment is not to limit the scope of the claims, but to help the understanding of the implementation method of the present invention. Those skilled in the art should understand that various modifications, cha...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More