Method and apparatus for controlling access in next generation mobile communication system
A wireless communication system and access type technology, which is applied in security devices, access restrictions, wireless communication, etc., can solve problems such as failure to make a determination, and achieve the effect of improving system throughput
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
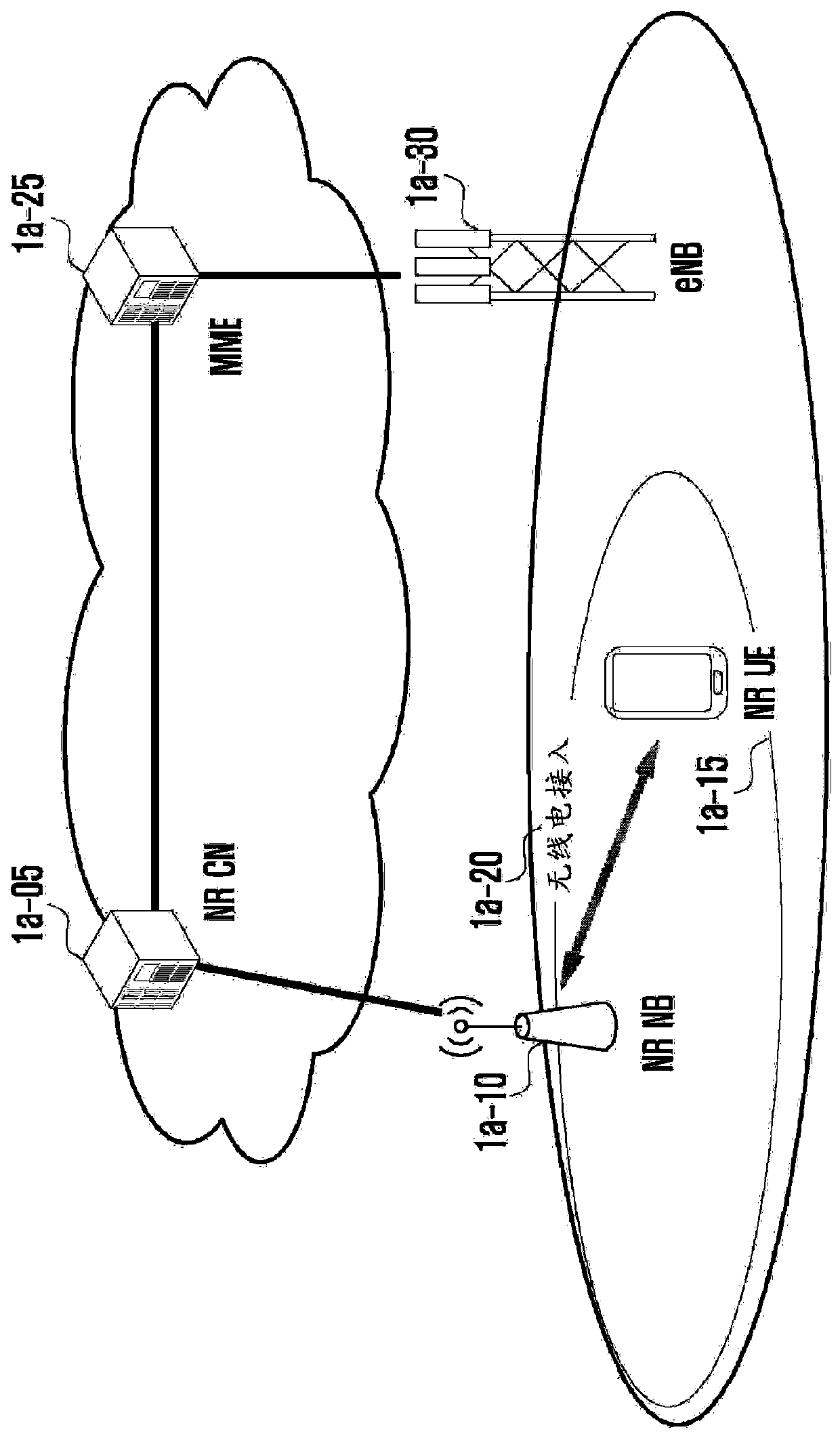
[0111] Figure 1A is a diagram showing the architecture of a next-generation mobile communication system according to an embodiment of the present disclosure.
[0112] refer to Figure 1A , the radio access network 1a-20 of the next generation mobile communication system includes a New Radio Node B (NRNB) 1a-10 and a New Radio Core Network (New Radio Core Network, NR CN) 1a-05. New Radio User Equipment (hereinafter referred to as New Radio User Equipment (NR UE) or simply UE) 1a-15 is connected to an external network via NR NB 1a-10 and NR CN1a-05.
[0113] exist Figure 1A Among them, NR NB 1a-10 corresponds to the evolved Node B (evolved Node B, eNB) in the traditional LTE system. NR UEs 1a-15 are connected to NR NBs that can provide services better than legacy eNBs. In a next-generation mobile communication system where all user traffic is served through a shared channel, entities are required to collect UE-specific status information (such as buffer status, power headroom...
Embodiment 1-1
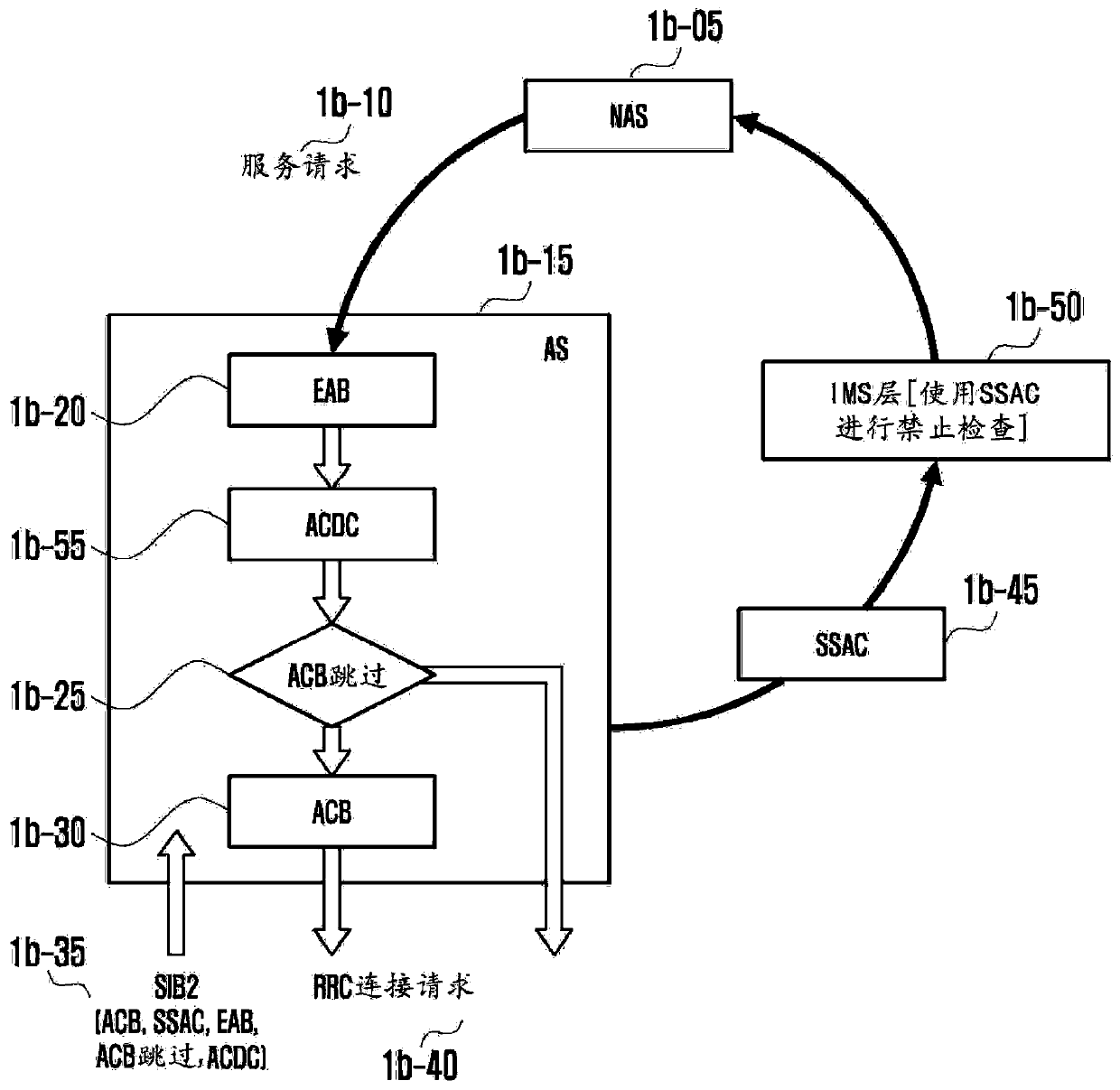
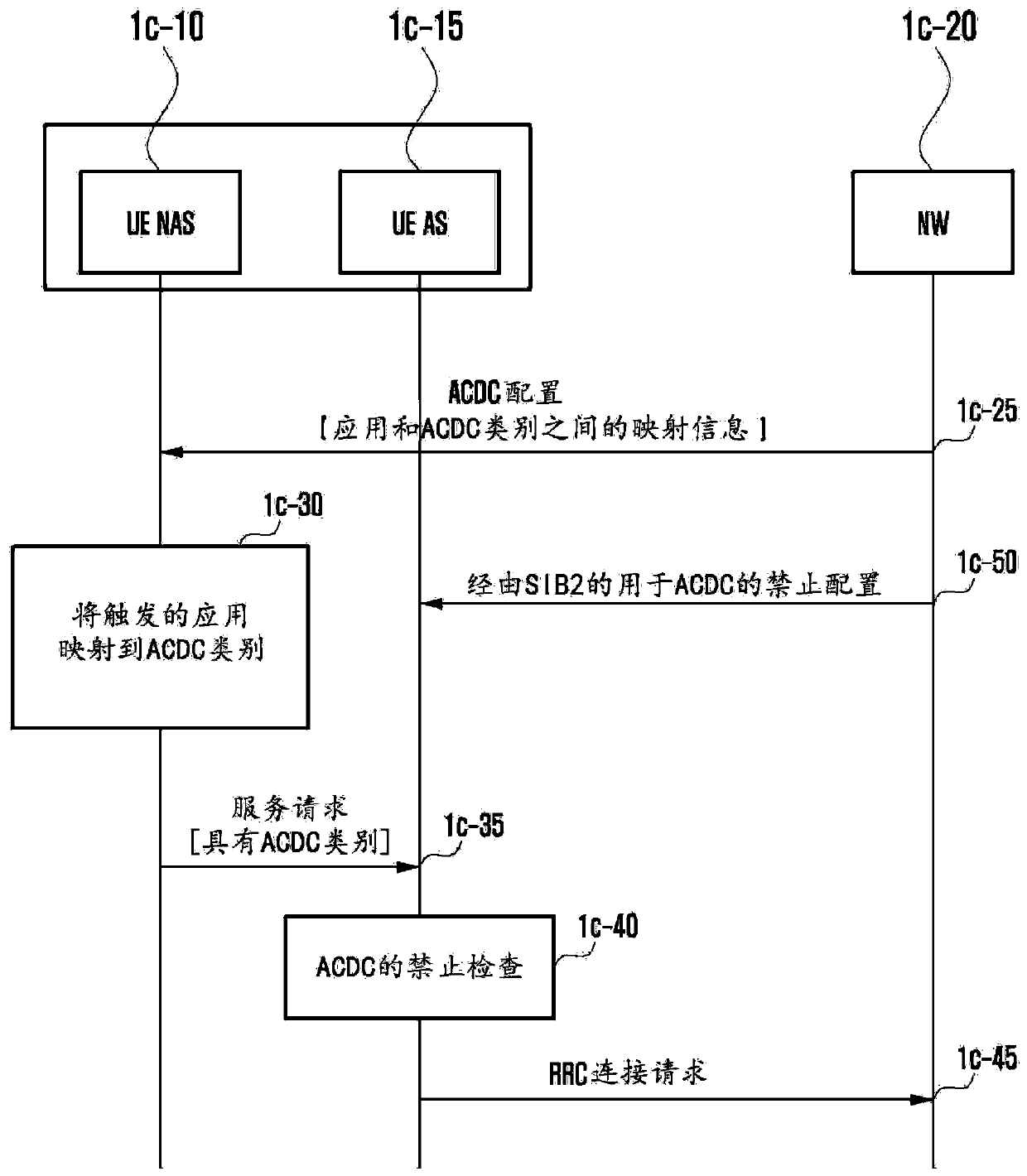
[0126] The present disclosure proposes a method for mapping access triggered by UE NAS to a specific category. In embodiment 1-1, UE NAS maps access to a category.
[0127] In embodiment 1-1, access is mapped to at least one standardized access category. Furthermore, access may not be mapped to any subcategory of the non-standardized access category provided by the network. In the present disclosure, classes provided by the network to which to map accesses are assigned at least one predetermined priority. The triggered access is mapped to the class with the highest priority among the classes to which the access can be mapped. In this disclosure, the category corresponding to "Urgent" belongs to the set of categories with the highest priority. The class corresponding to "high priority access" may belong to the set of classes with the highest priority. High-priority access means mobile communication operator-only access or public office-only access, such as police and firefi...
Embodiment 1-2
[0147] In embodiments 1-2, the UE NAS maps the access to a standardized access class and additionally to a non-standardized access class to which the access may be mapped. In this disclosure, the service request sent by the UE NAS to the UE AS includes information indicating the standardized access category, because the triggered access should be mapped to a standardized access category. At operation 1f-05, the UE AS does not provide the access class list. Therefore, the operation of determining whether an access can be mapped to one of the non-standardized access classes at operation If-25 is not performed based on the non-standardized access classes included in the list. For example, UENAS determines whether there is a non-standardized access class based only on information about the non-standardized access class that the network can support provided through NAS signaling or application layer signaling.
[0148] In embodiments 1-2, the UE NAS may send both standardized and ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More