Attribute encryption access control method for edge computing
A technology of attribute encryption and access control, applied in the field of data security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0035] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with specific examples.
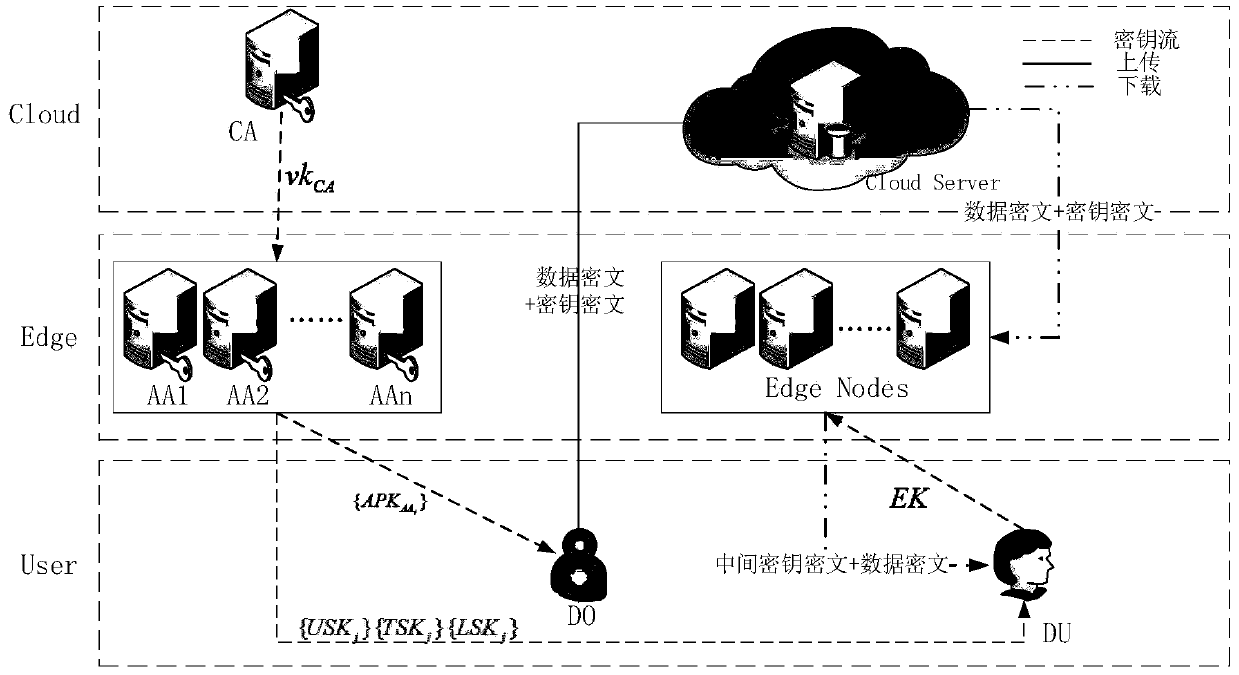
[0036] The system model of the present invention is as figure 1 As shown, the model consists of six entities, which are central authority (CA), cloud server (CSP), attribute authority (AA), edge node (EN), data owner (DO) and data user (DU). ). CA is responsible for user and AA authentication and authorization. Each AA is independent of each other and is responsible for managing the attributes in their respective domains, and generating and distributing the attribute private keys of DUs. CSP provides the capability of permanent storage. EN provides storage and computing capabilities. DO is responsible for formulation of access policy (A, ρ) and generation of ciphertext. DU is responsible for the decryption of the intermediate key ciphertext.
[0037] An edge computi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com