Vulnerability detection method and device, electronic equipment and computer readable storage medium
A technology of vulnerability detection and the system under test, which is applied in the field of network security, can solve the problems of incompleteness and low accuracy of vulnerability detection, and achieve the effect of high accuracy and comprehensive vulnerability detection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
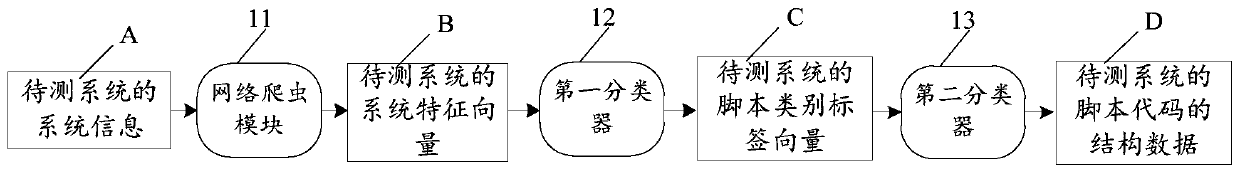
Image
Examples
Embodiment Construction
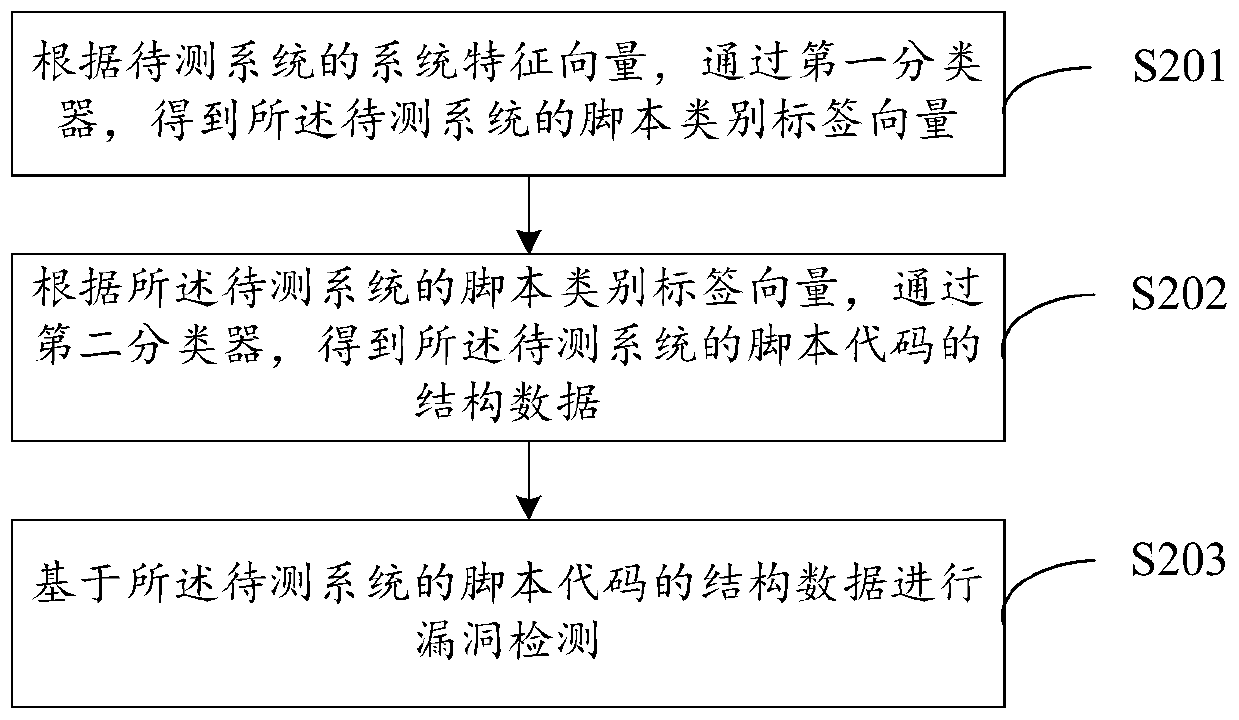
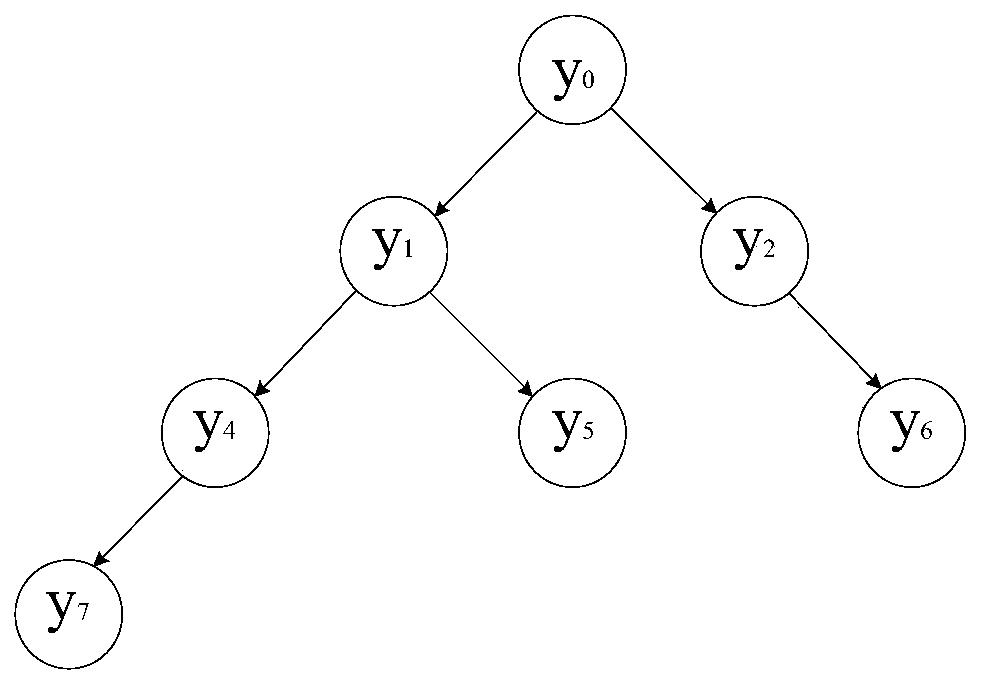
[0031] The following will clearly and completely describe the technical solutions in the embodiments of the application with reference to the drawings in the embodiments of the application. Apparently, the described embodiments are only some, not all, embodiments of the application. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
[0032] Application overview
[0033] With the wide application of Web systems in various business fields on the Internet, various Web security vulnerabilities have brought great security threats. It is a necessary measure to ensure the security of the Web system to determine whether there are loopholes in the Web system through testing. Currently, detection methods for web system vulnerabilities mainly include methods based on web crawlers, text mining methods, attack trees, attack graphs, and...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More