Although Kirin can detect application permission extraction information during installation, Kirin still has some obvious deficiencies: First, the result error rate is high, and Kirin identifies sensitive resources, functional requirements,
resource security requirements and
security system limitations of the application There are errors and difficulties in other factors, and the final result is not accurate; second, Kirin does not provide solutions, but only prompts users to a certain extent, and does not provide in-depth ability to solve problems; problems, cannot bring flexible
processing methods, and play a very limited role in user
authority control[0008] First, with the increasingly complex security environment of the Android system, although the original
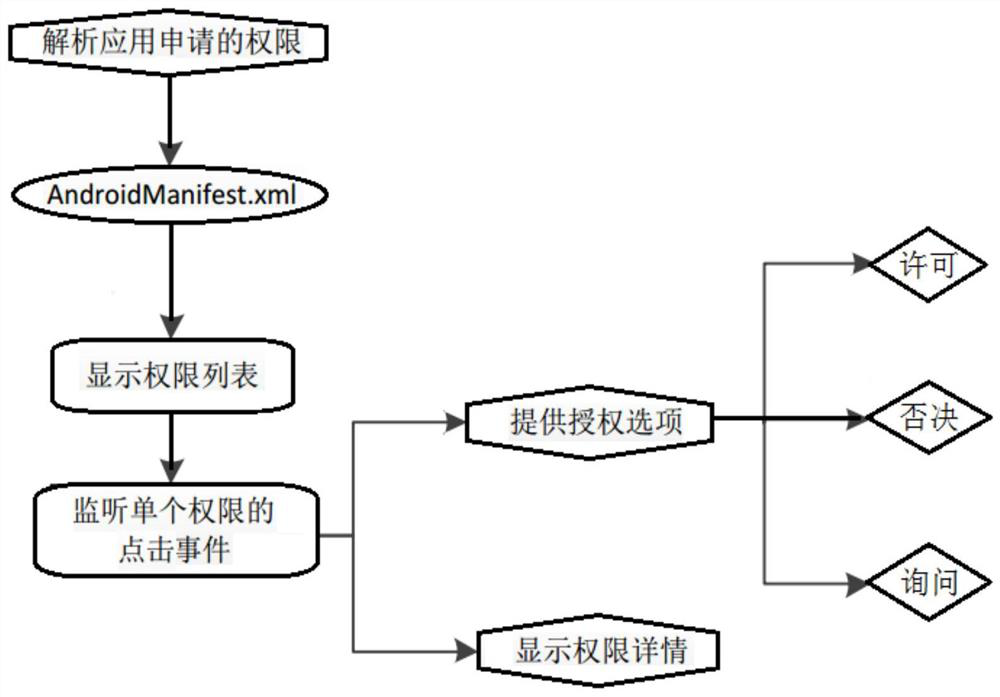
permission system has played a significant role, it has gradually exposed a large number of problems. When installing an application, the coarse-grained
authorization management strategy reads and parses the application in the configuration file. Permission information is displayed to the user on the installation page for the user to view and confirm. Two buttons, Install and Cancel, are provided on the interface. When the user clicks Install, it means that the application adopts all permissions and enters the installation process. When the user clicks Cancel, it means Deny all permissions, cancel the application installation request directly, and the user is still in a very passive position of choosing one or the other
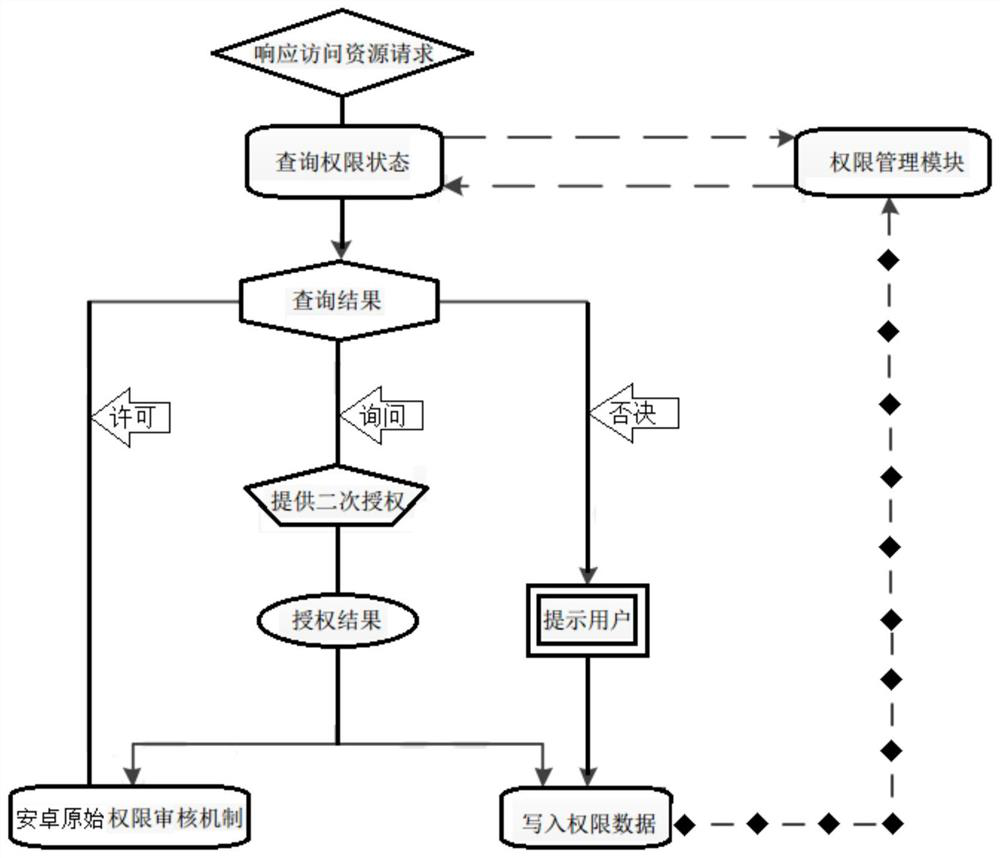
[0009] The second is that the distribution of permissions in the existing technology cannot be dynamically set. In the original Android system, all permissions can only be checked and confirmed during installation. Second Chance for Change
[0010] The third is that in the existing technology, users choose whether to install the application or not only depends on the degree of their urgent needs, do not understand the meaning of permissions, and have no direct
perception of the security risk of permissions.
The analysis of permissions is too few and professional. Ordinary users can neither understand the meaning of permissions, nor do they know whether
application security is guaranteed. There is nothing that can be used as a reference for users. The hidden dangers brought by permission security are not considered at all. The permission
control system The function of the can not play a real role
[0011] Fourth, the existing technology is centered on developers, and there are insufficient permissions system documents. Developers often focus on function realization and ignore the importance of permission applications. In addition to being careless when writing code, the bigger reason is that they themselves have limited understanding of permissions. , there is no comprehensive
documentation to help
The emergence of redundant permissions is a favorable condition for malicious applications to use to
attack. Accessing important resources and private information of applications through permissions will eventually bring losses to users. The reason is that developers lack understanding of permissions and lack of professional knowledge. Numerous permissions cannot clearly distinguish the corresponding relationship between actual functions and permissions, resulting in misuse and abuse of permissions
[0012] Fifth, the existing technology does not detect the security risks that may be caused by combined permissions. In addition to a single permission that can bring security risks, the use of multiple permissions is also one of the characteristics of
malware[0013] Sixth, the existing technology cannot accurately identify the security
risk level of the application program. When the application program is installed, the user can only see the
list of permissions applied for by the program. For ordinary users without professional background, the auxiliary information during installation is too formal and has no real Solve the problem
[0014] Seventh, the existing technology lacks reasonable suggestions and security defense strategies. In the existing Android original installation system, the user can only choose to install or cancel after seeing the permission
list. When Disturbed by the
Potential Impact of Permissions, There Is No Better Choice
Once the user urgently needs to adopt the application, there is no reasonable solution in the actual
scenario, only to choose to install or cancel
 Login to View More
Login to View More  Login to View More
Login to View More