Intelligent model information leakage degree evaluation method and system, medium and equipment
An information leakage and degree of technology, applied in the field of network security, can solve the problems of limited attack types, model construction equivalent proxy models, and few models, and achieve the effect of rapid feedback and high evaluation accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0066] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0067] Aiming at the problems existing in the prior art, the present invention provides a method, system, medium, and equipment for assessing the degree of information leakage of an intelligent model. The present invention will be described in detail below in conjunction with the accompanying drawings.
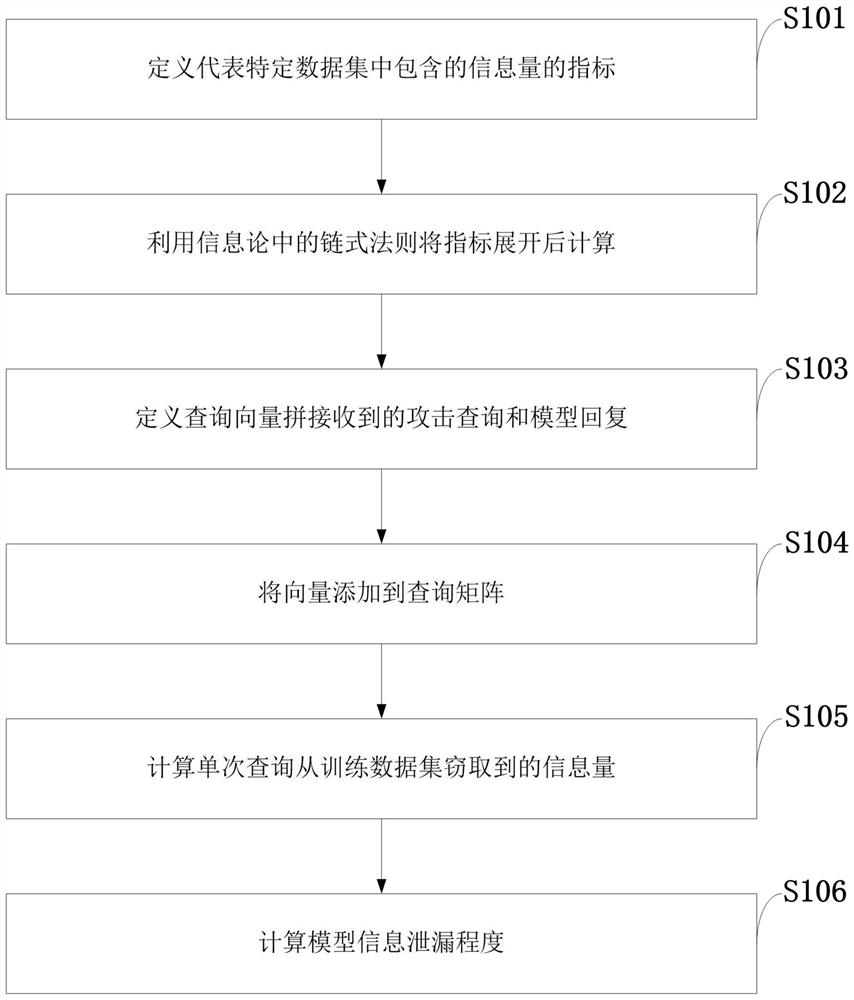
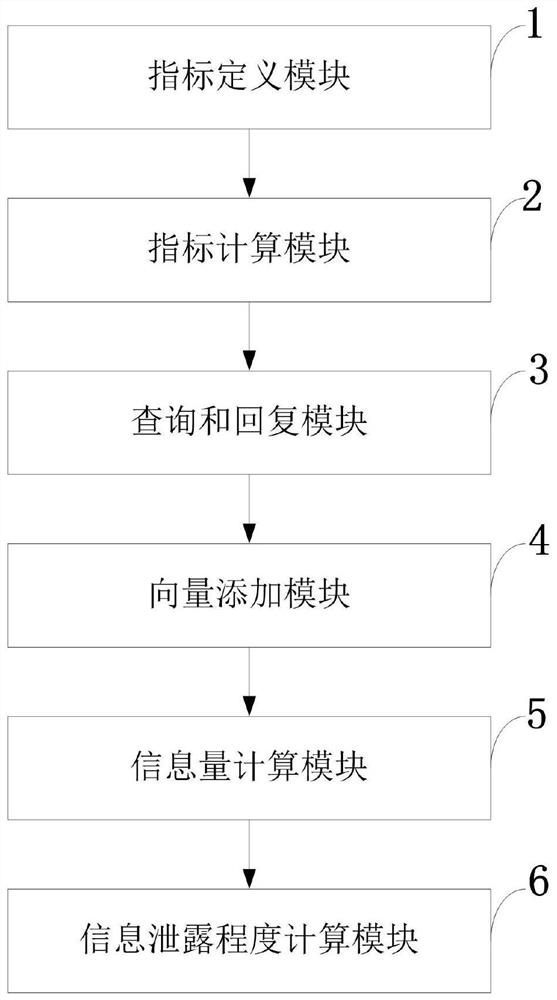
[0068] Such as figure 1 As shown, the intelligent model information leakage degree evaluation method provided by the present invention includes the following steps:
[0069] S101: Define an indicator representing the amount of information contained in a specific data set;
[0070] S102: Use the chain rule in information t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More