Power attack test system based on attack topology
An attack test, power technology, applied in transmission systems, electrical components, etc., can solve problems such as the inability to provide simulated attack samples
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0022] The following description serves to disclose the present invention to enable those skilled in the art to carry out the present invention. The preferred embodiments described below are only examples, and those skilled in the art can devise other obvious variations. The basic principles of the present invention defined in the following description can be applied to other embodiments, variations, improvements, equivalents and other technical solutions without departing from the spirit and scope of the present invention.
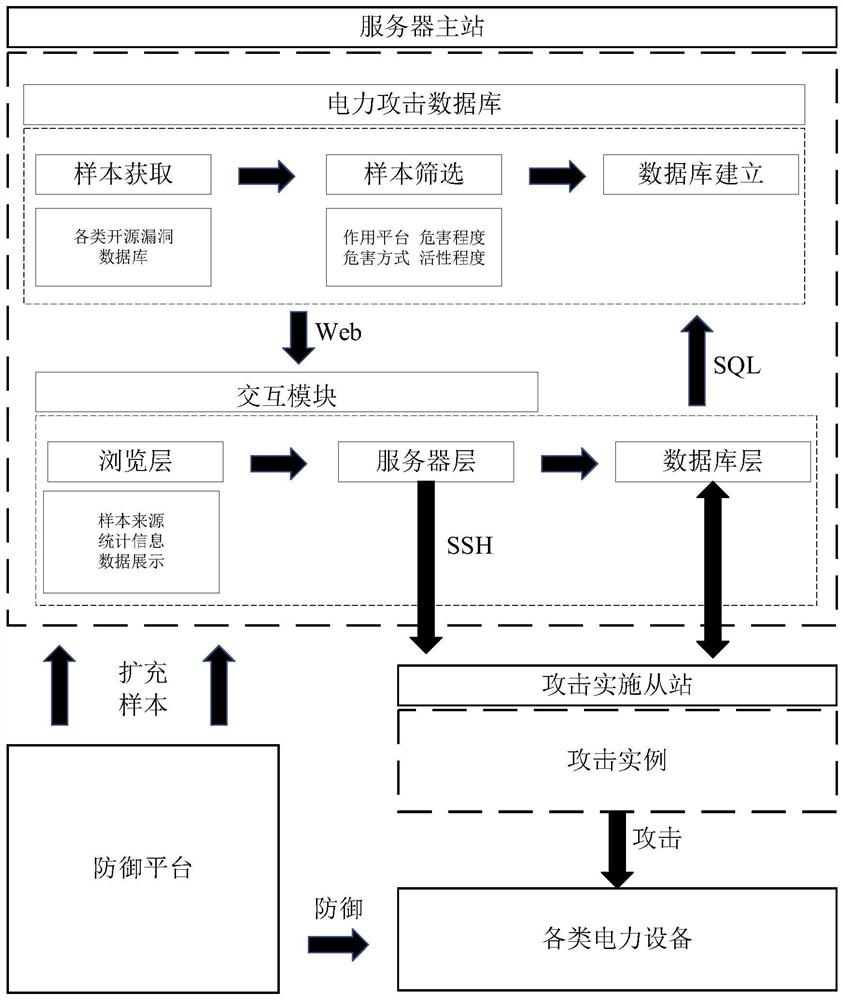
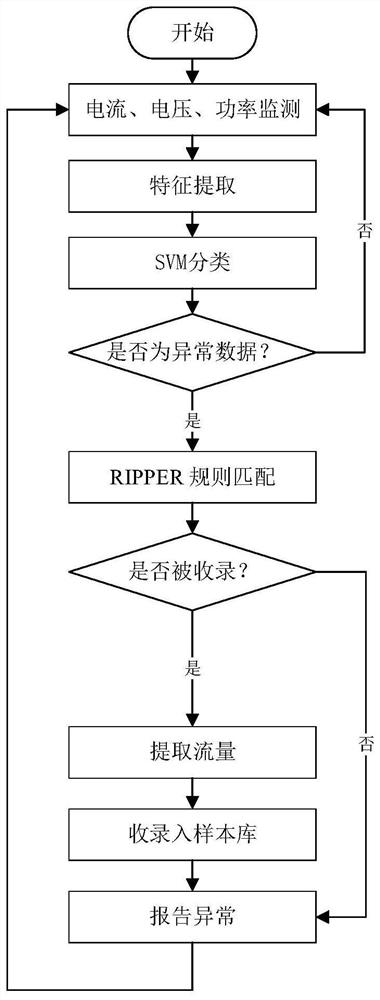
[0023] Such as figure 1 As shown, the construction process of the power attack test system of the present invention includes the following steps:
[0024] 1) Construction of power attack sample database:
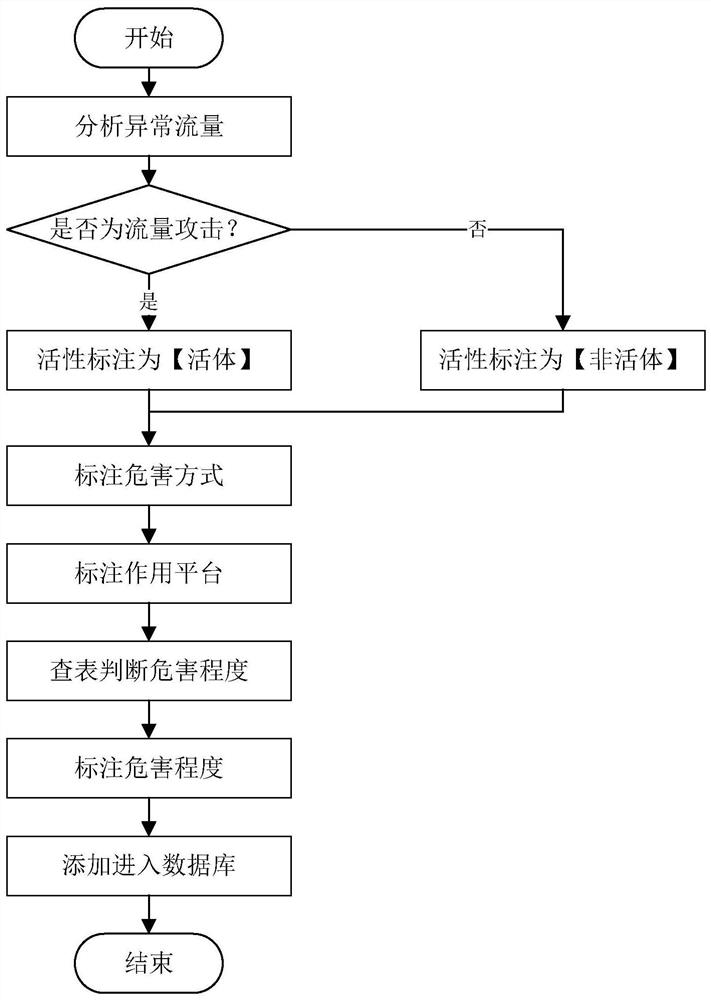
[0025] ① Data acquisition: There are two types of data sources for the power attack sample database. One is the basic data, which comes from the China National Information Security Vulnerability Sharing Platform, the National Information Security Vul...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More