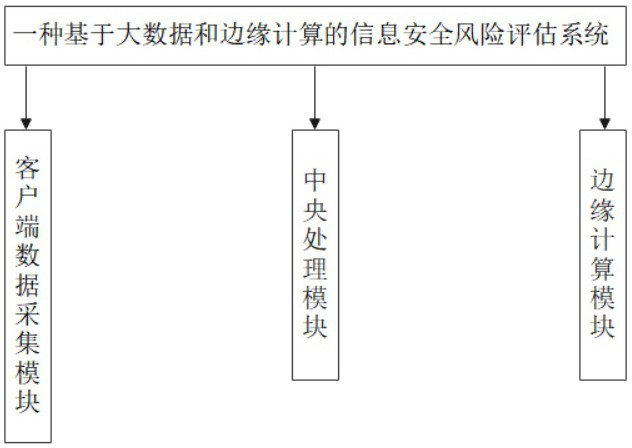
Information security risk assessment system and method based on big data and edge computing
An edge computing and information security technology, applied in the field of risk assessment, can solve problems such as unreceived, paralyzed, and impact on equipment to be managed, and achieve accurate security, get rid of dependence, obtain and execute in a timely manner
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
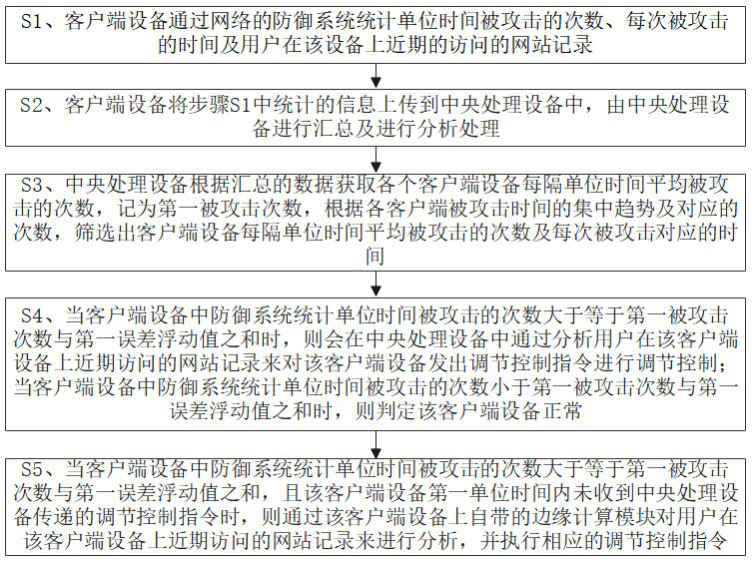
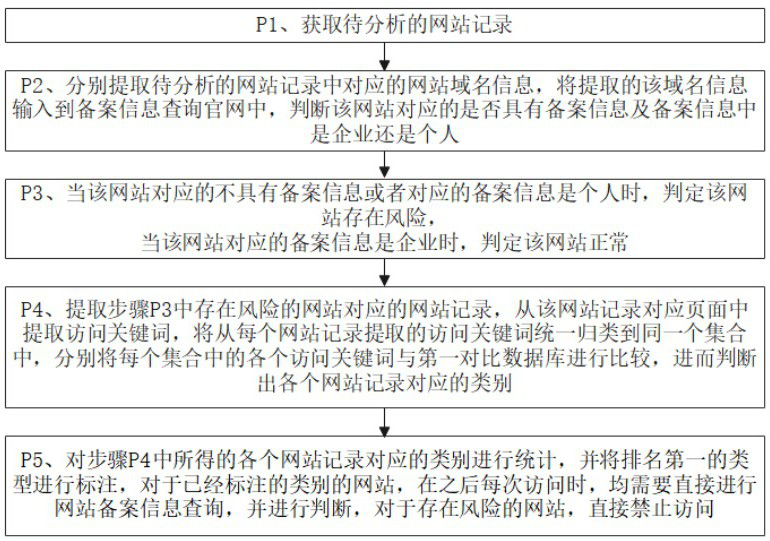
[0055] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
[0056] see Figure 1-Figure 4 , the present invention provides a technical solution: an information security risk assessment method based on big data and edge computing, characterized in that the method includes the following steps:
[0057] S1. The client device counts the number of attacks per unit time, the time of each attack, and the recent website records visited by the user on the device through the network defense system;
[0058] S2. The client devic...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More