Industrial internet field identity access control method based on zero-trust model
An industrial Internet and access control technology, applied in the field of identity access control in the field of industrial Internet based on the zero trust model, can solve problems such as the lack of effective and complete solutions
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
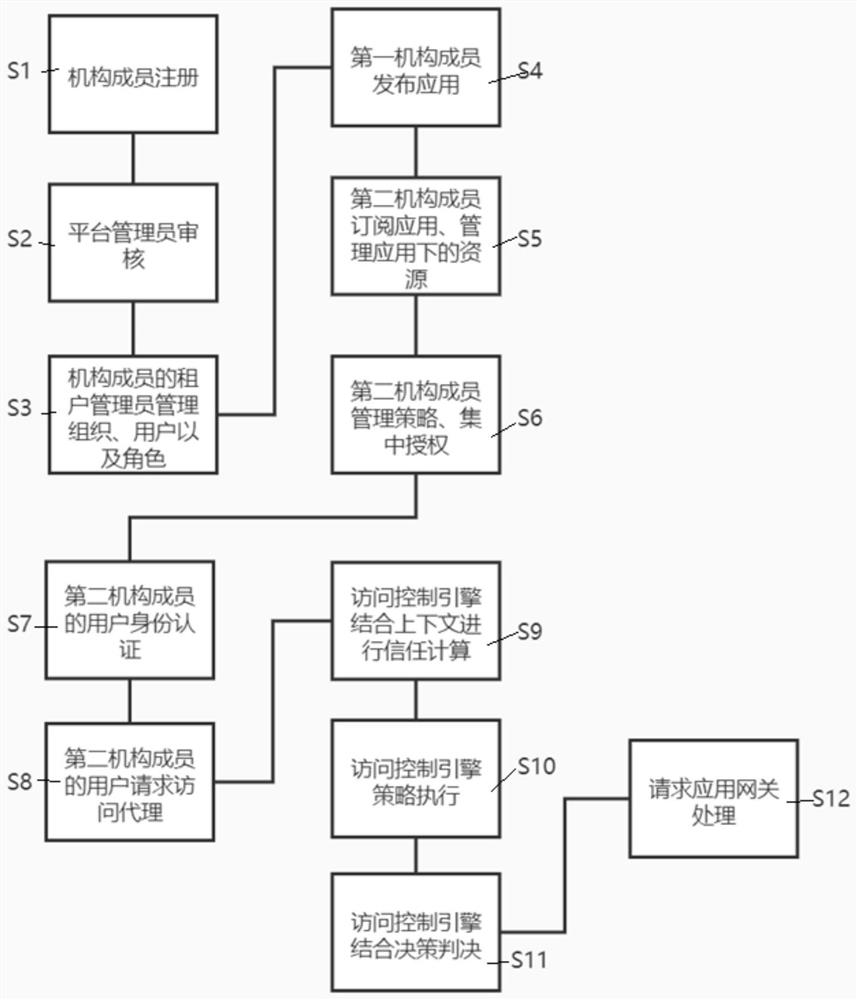
[0053] The present invention will be further described below in conjunction with accompanying drawing.
[0054] see figure 1 , the present invention is a zero-trust model-based identity access control method in the field of industrial Internet, the method comprising the following steps:
[0055] S1. Institutional members of the Industrial Internet platform register through the Zero Trust platform and submit corporate information to apply for tenant administrators.
[0056] S2. The administrator of the industrial Internet platform reviews the materials submitted by the organization members, creates tenant information after passing the review, and notifies the organization members of the review results.
[0057] S3. The tenant administrator manages organization and view information, user and user group information, role and role group information, and the association relationship between user groups and role groups. The association relationship is as follows: 1) An organizatio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More