Program grade invasion detecting system and method based on sequency mode evacuation
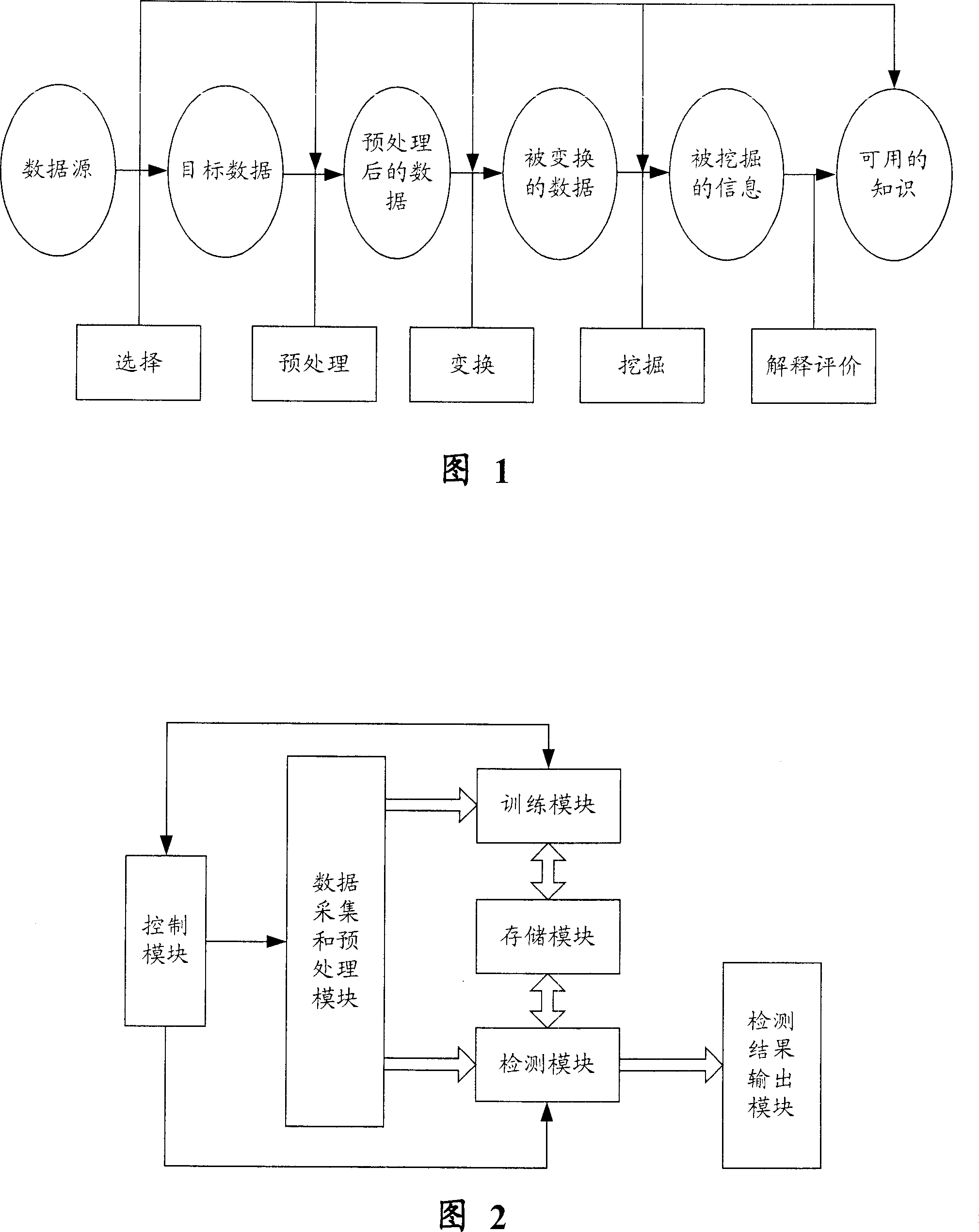
A sequence pattern mining and intrusion detection technology, applied in the field of network information security, can solve problems such as system call sequence differences
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
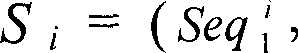
Embodiment Construction
[0071] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings.
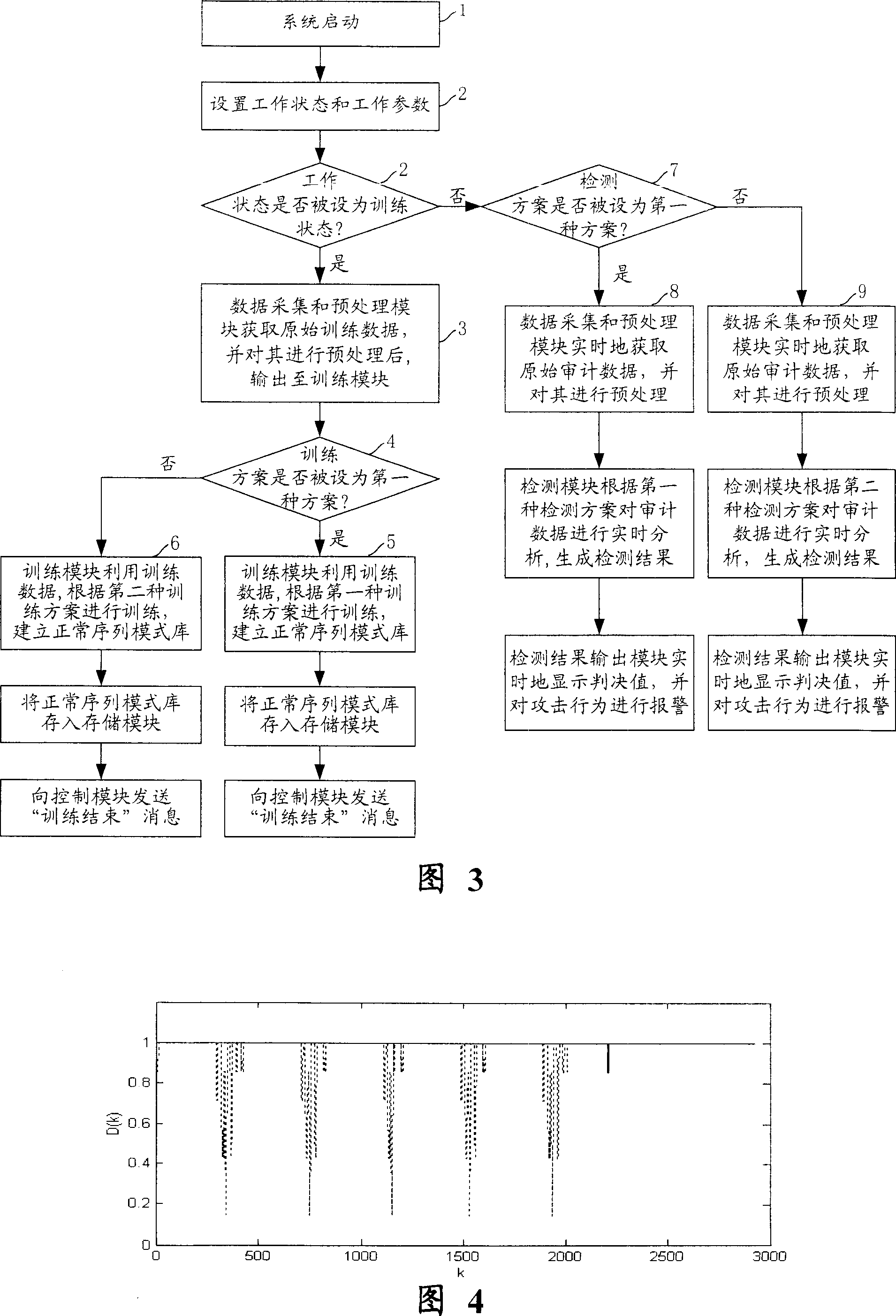
[0072] Referring to FIG. 2 , the structure of a program-level intrusion detection system based on sequence pattern mining in the present invention is introduced. The system is a software product, that is, each module is composed of corresponding program units, configured on the server that needs to be monitored, using the system calls generated when the privileged program is running as audit data, and monitoring the operation of the privileged program in the network server , using anomaly detection technology based on data mining to detect whether intrusion occurs in the network server. The system consists of a control module, a data acquisition and preprocessing module, a training module, a storage module, a detection module, and a detection result output module....
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More