Method for authenticating validity of IKE V2 certificate
A key exchange protocol and validity technology, applied in the field of certificate validity verification in the Internet key exchange protocol, can solve problems such as low efficiency and lack of security guarantees, and achieve the effect of improving efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
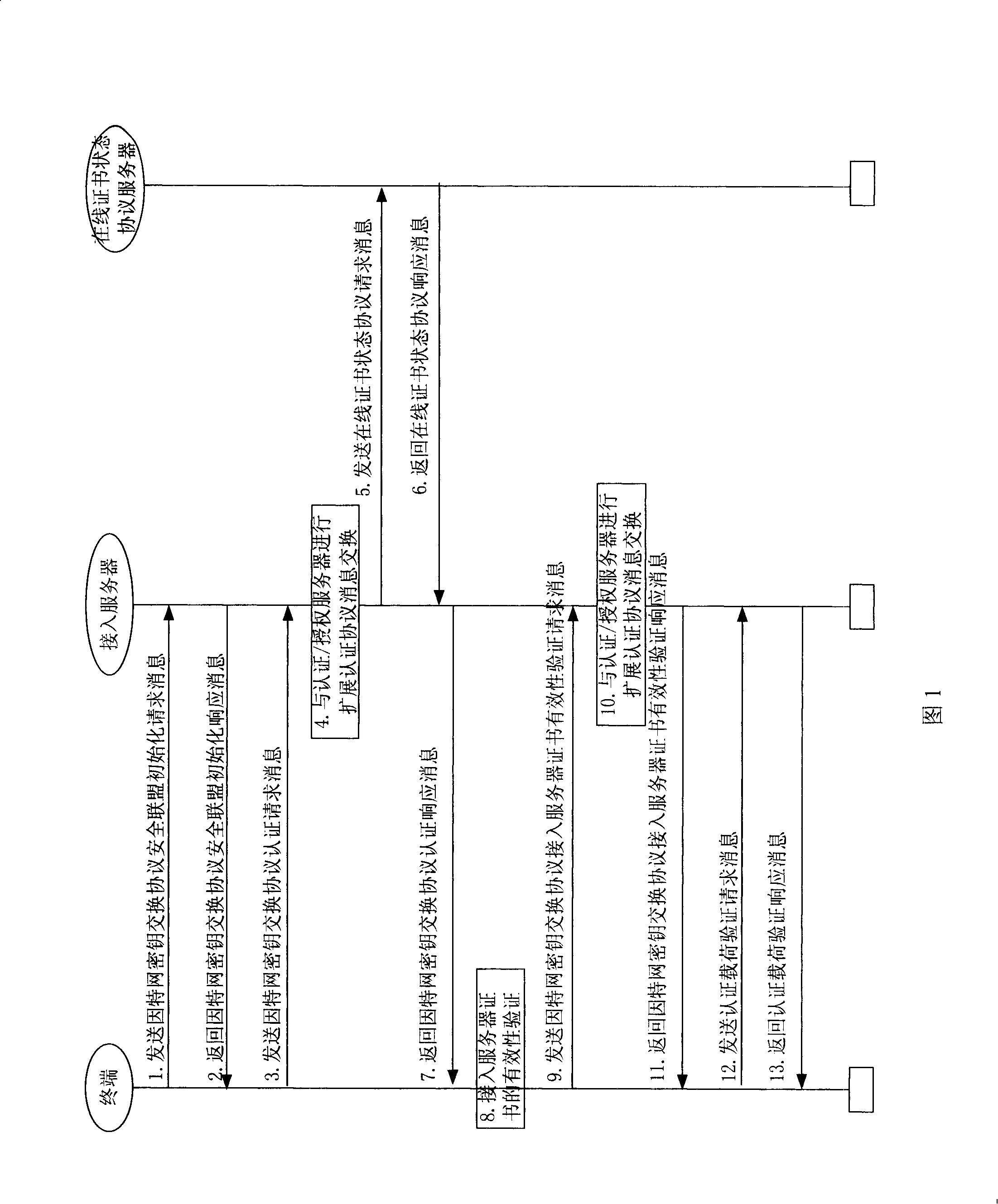
[0019] Below in conjunction with accompanying drawing, the present invention will be described in further detail:
[0020] In Fig. 1, an IPsec tunnel is established between the terminal and the access server through IKEv2 negotiation, and then the terminal accesses the network through this tunnel. In the IKEv2 protocol process, the terminal authenticates the identity of the access server through the certificate, and the access server uses EAP (Extensible Authentication Protocol) to verify whether the terminal is an authorized legal user. After the terminal and the access server authenticate each other and complete the security parameter negotiation, the access server allows the terminal to access the network. Before the IKEv2 process is completed, the terminal is not allowed to access the network, so it cannot access the OCSP server in the network to verify the validity of the access server certificate.
[0021] Using the method proposed by the invention, the terminal complet...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More