File encryption-decryption method of USB removable storage device
A mobile storage device and storage device technology, applied in the field of information security, can solve the problems of non-real-time encryption and decryption, time-consuming and inconvenient, and achieve the effects of security performance assurance, good functional characteristics, and improved transmission rate
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
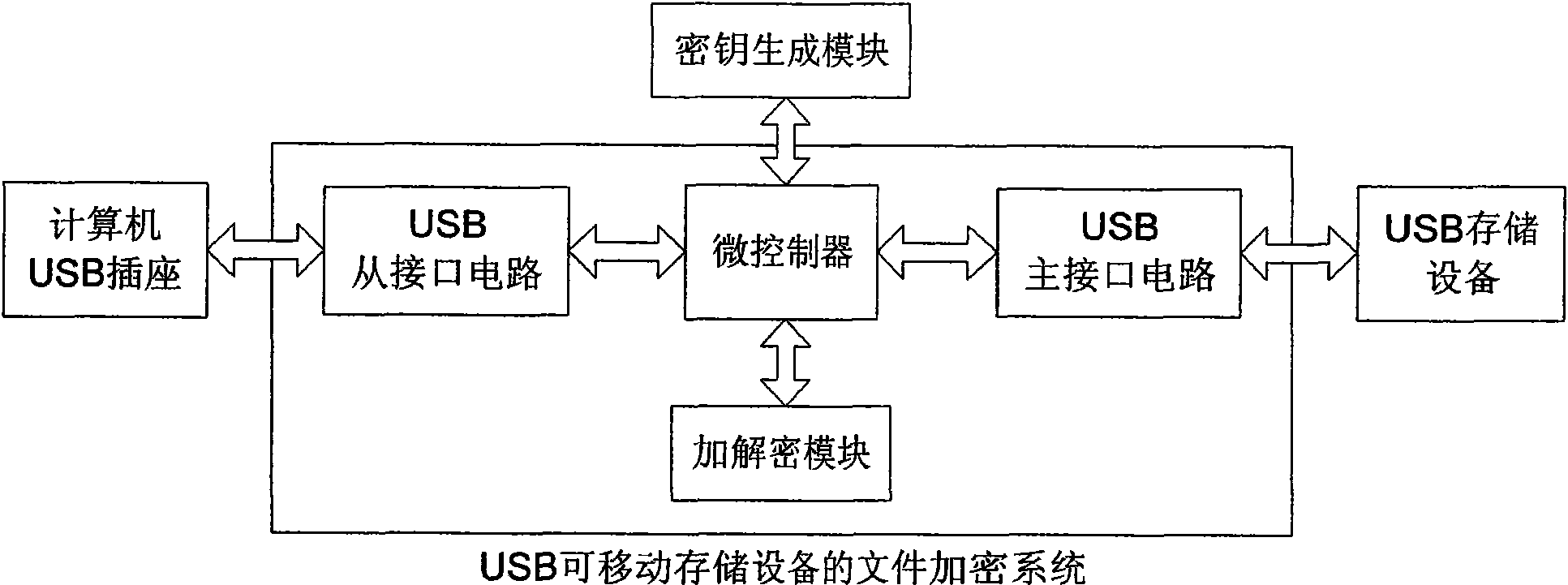
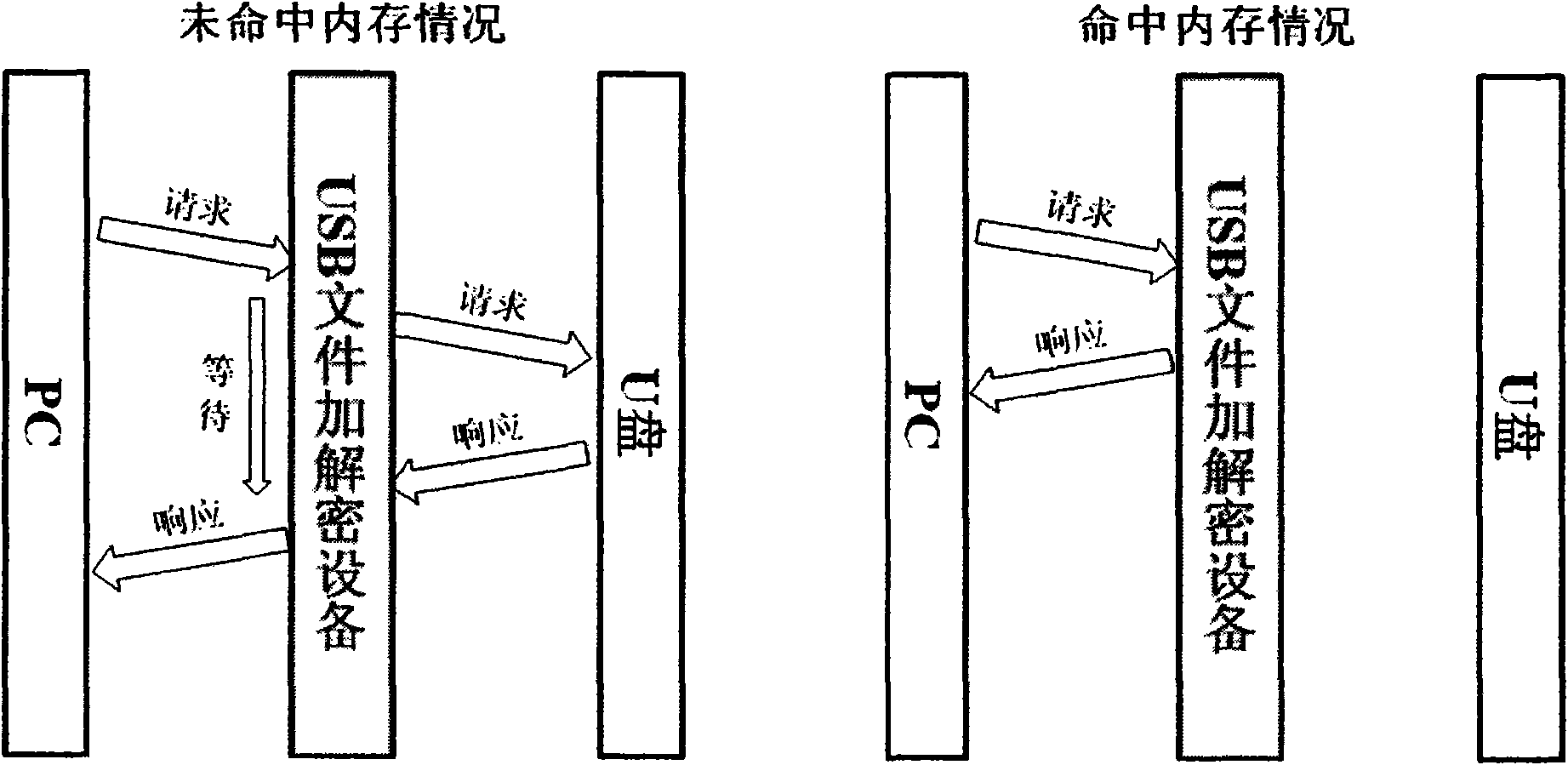
[0024] The file encryption and decryption method of the USB removable storage device of the present invention is respectively connected to the computer and the USB storage device through two USB interfaces, and the analysis and filtering of the USB data stream on one of the USB interfaces identifies the file data cluster of the FAT file system ; At the same time, by opening up a cache, using the direct mapping method to map with the address of the USB storage device, and temporarily storing the data that has been read and written recently; then use the encryption and decryption algorithm for the identified file data, and replace the encryption The data before decryption is finally returned to the physical layer and sent out from another USB interface. The key can be obtained from the key generation module through a reserved port.
[0025] Concrete steps that the present invention comprises are as follows:
[0026] 1. Analysis of USB data stream:
[0027] The analysis of the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com