Method for implementing extensible trusted SSH
An implementation method and reliable technology, applied in electrical components, user identity/authority verification, transmission systems, etc., can solve problems such as poor scalability, and achieve the effect of tight integration
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
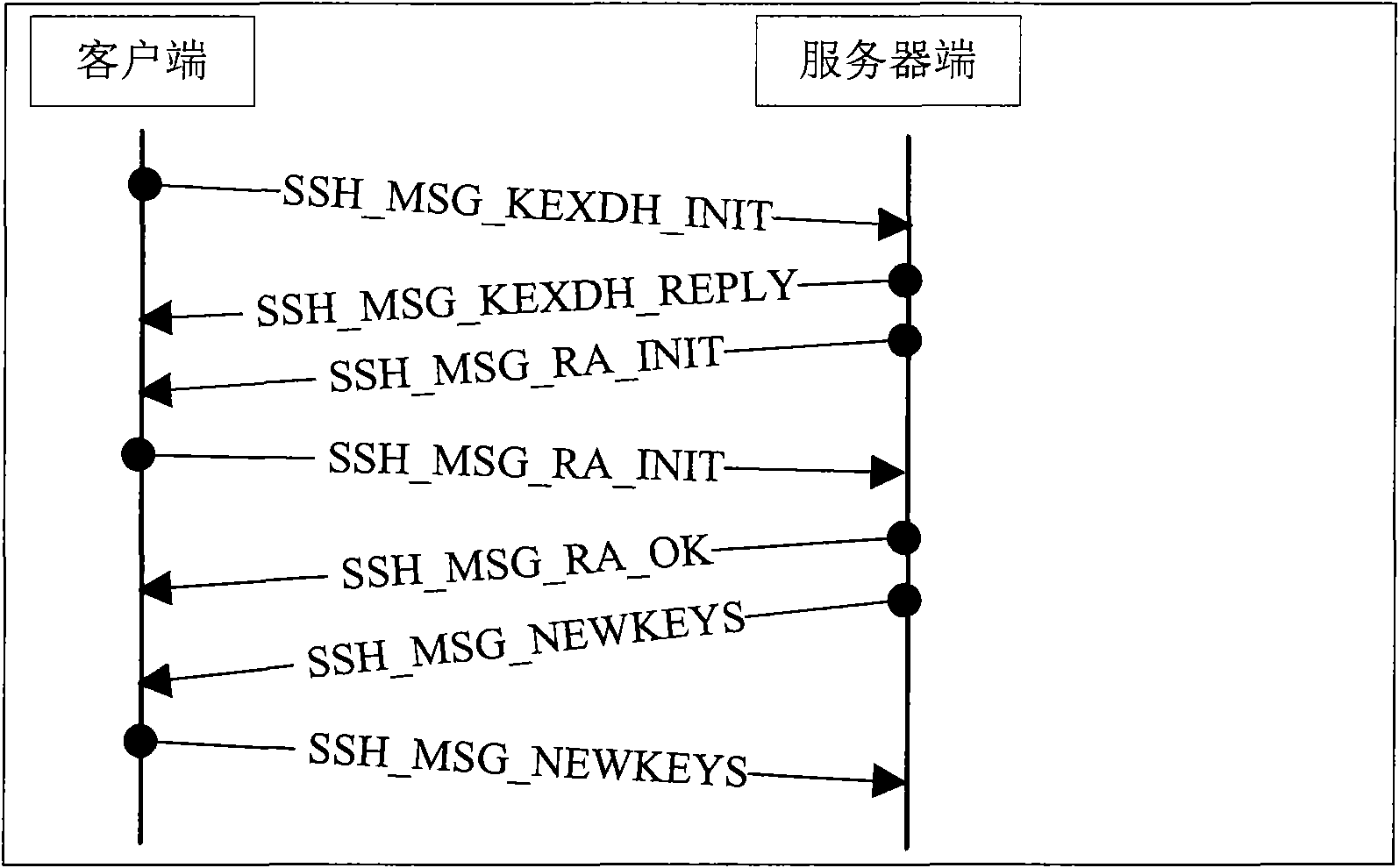
[0024] Below through specific embodiment and image 3 The present invention will be described in detail.
[0025] The method provided by the present invention requires both the server end and the client end to be equipped with a trusted security chip in hardware, and the BIOS of the server end and the client end all support TPM; in terms of software, the server end and the client end are required to install a measurement module and a trusted operating system . The measurement module determines the entity to be measured, the measurement time and the method of safely maintaining the measurement result. Its main functions include calculating the measurement value of those measured entities, recording the measurement event to the measurement storage log and recording the measurement value into the TPM specified PCR. The method of recording the measurement value into the PCR is: new PCR value=hash(original PCR value||measurement value). The metric storage log includes at least: ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More