Mobile commerce identity authentication method
An identity authentication and business technology, applied in the field of mobile business information security, can solve the problems that traditional authentication protocols cannot be directly applied to mobile business environment, password sequence method decimal attack, time synchronization scheme is not easy to implement on mobile network, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0083] Authentication model architecture such as figure 1 As shown, the model divides the authentication into two levels, the first level is the authentication of the identity of the user 1 by the mobile device 2, and the second level is the two-way identity authentication between the mobile device 2 and the authentication server 3. The first level verifies that the user 1 using the mobile device 2 is a legitimate user, and the second level verifies the legitimacy of the mobile device 2 and the authentication server 3, that is, it is not a counterfeit terminal. If the first-level verification fails, there will be no communication between the mobile device 2 and the authentication server 3 . If the first-level verification is passed, the mobile device 2 automatically communicates with the authentication server 3, and the user 1 cannot see the process and can only know whether the verification is passed.
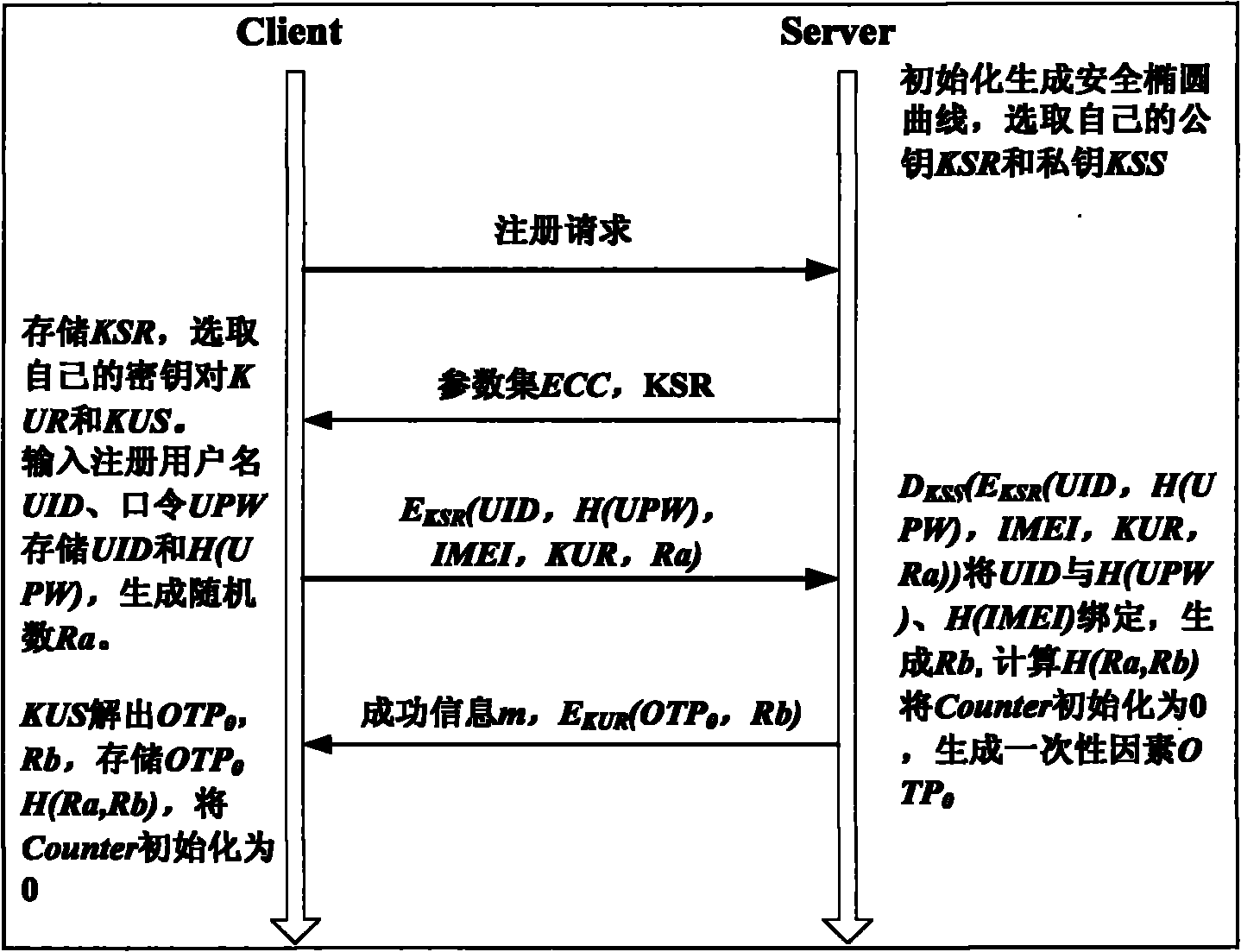
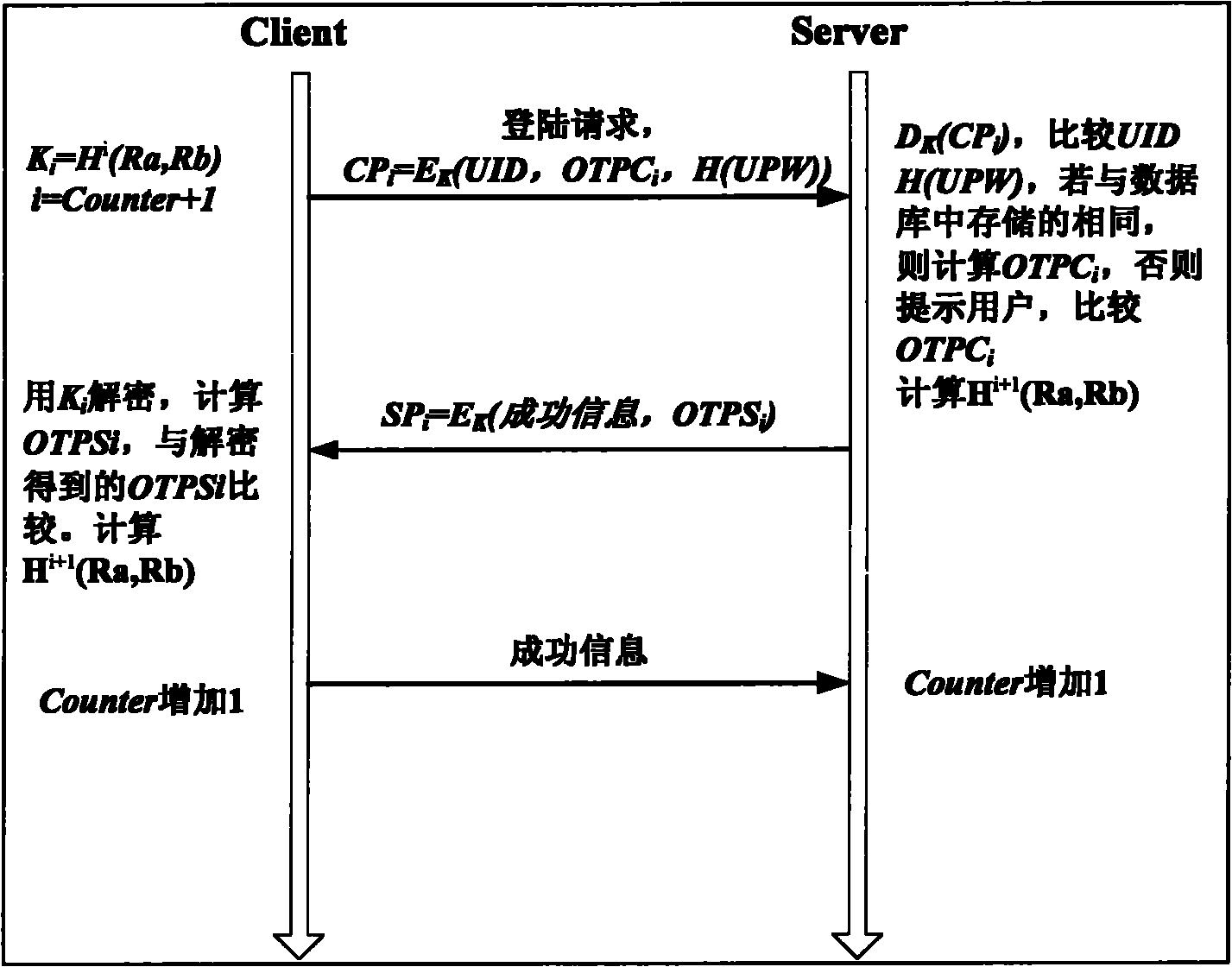
[0084] like Figures 2 to 4 The flowcharts are the registration stage, ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More