Safety communication among virtual machines in cloud computing framework
A virtual machine and cloud computing technology, applied in the field of cloud computing, can solve the problem that the security mechanism cannot allocate the data storage area, and the user cannot actively customize the network resources of the security level.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
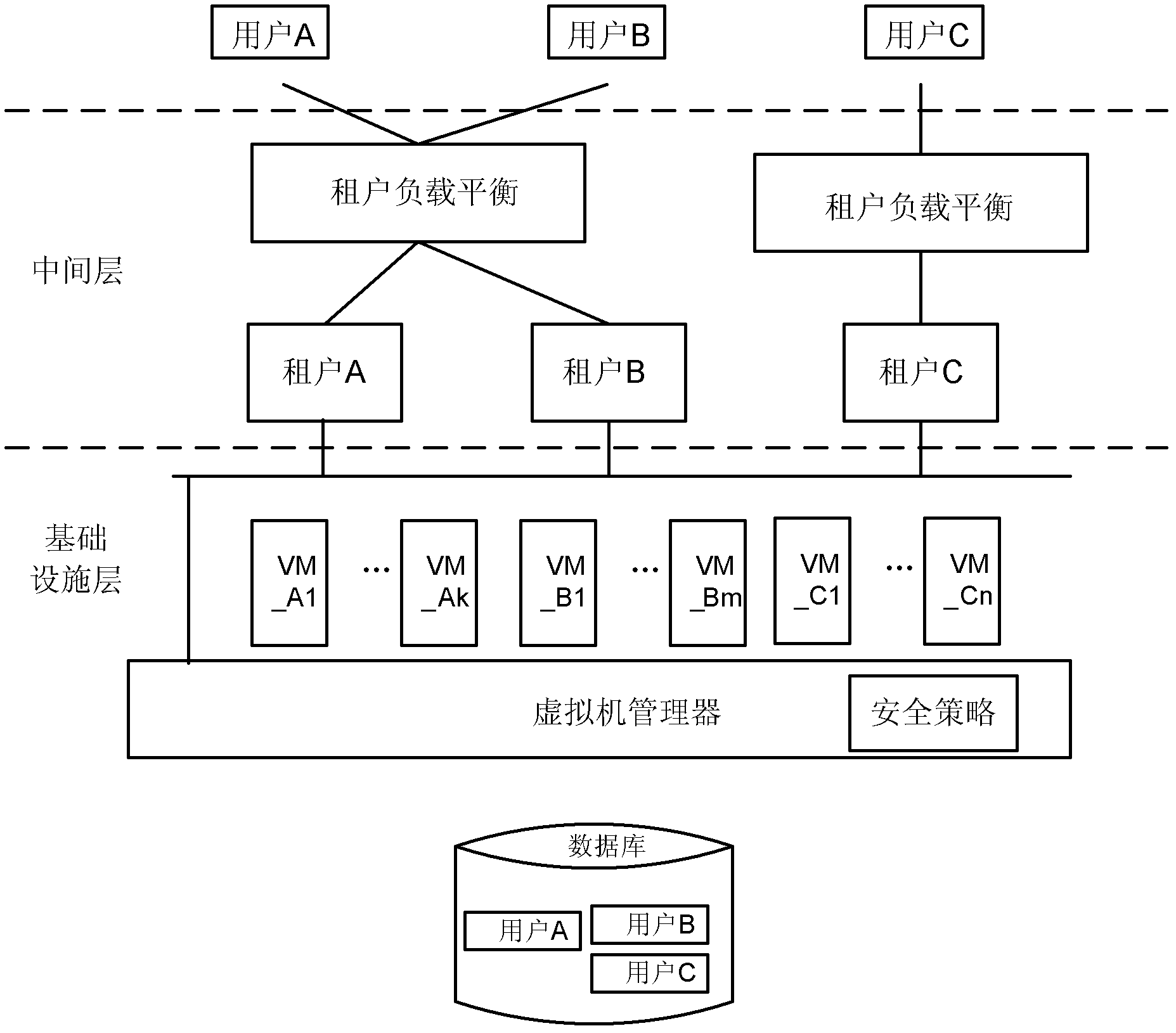
[0023] It is believed that the above and other objects, features and advantages of the present invention will become more apparent through the following detailed description of specific embodiments of the present invention in conjunction with the accompanying drawings.
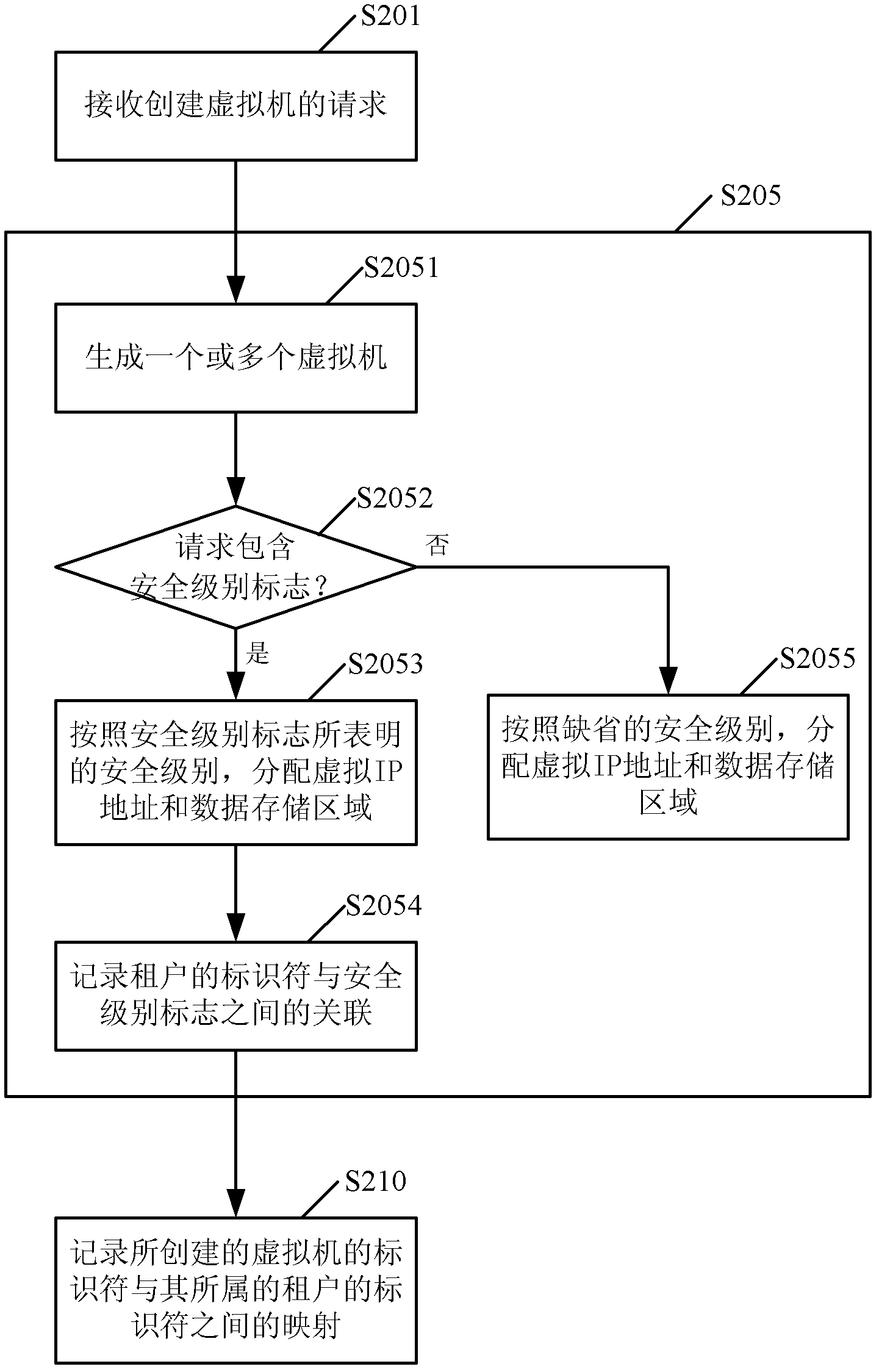
[0024] figure 2 A flowchart showing a method for creating a user's virtual machine in a cloud computing architecture according to an embodiment of the present invention. The present embodiment will be described in detail below in conjunction with the accompanying drawings.
[0025] The method for creating a user's virtual machine in this embodiment can be executed in a virtual machine manager in a cloud computing architecture.
[0026] like figure 2 As shown, in step S201, a request for creating a virtual machine is received from a tenant established by a user. As mentioned above, when a user executes an application, a tenant for the application is created. The tenant then generates and sends a request t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More