Host file security monitoring method
A security monitoring and file technology, applied in the field of information security, can solve the problems of increasing the internal control security of terminal files, single monitoring function, lack of monitoring strategies, etc., and achieve the effect of simple structure and fast running speed.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] The present invention will be further described below in conjunction with the accompanying drawings and embodiments.
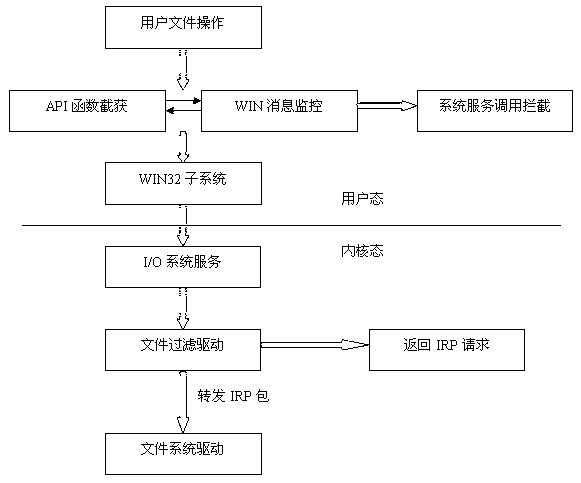
[0035] This embodiment provides a host file security monitoring protection method, such as Figure 1~Figure 4 As shown, the following steps are included.
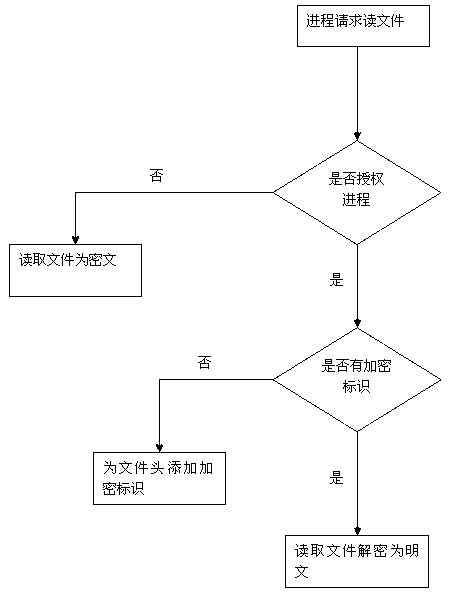
[0036] Step 1, when the user creates a new file or reads an existing file on the hard disk, determine whether the current process is authorized, if the current process is an authorized process, and the file type belongs to the file type that needs to be protected, then determine whether the file contains Encryption flag, if it contains, encrypt the file on the hard disk, and put this piece of data in the protected memory area; if it does not contain encryption flag, add encryption flag to the file header.
[0037] Step 2, monitor and protect the file types, and the user is not allowed to change the protected file types.
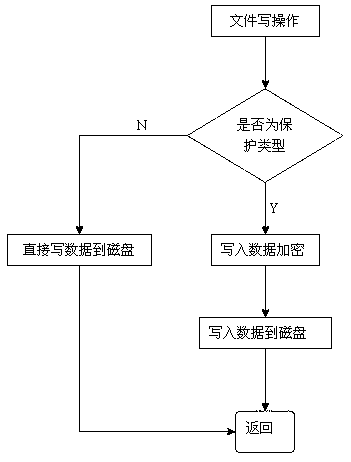
[0038] Step 3: For the file to which the encryption mark has been added, the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More