Node collaboration based Sybil attack detection method
An attack detection and node technology, applied in the cross technology application of information security, the field of wireless sensor network, can solve the problem of not considering the node transmission power, Sybil node missed detection and false detection, etc., to extend the network life cycle and reduce false detection. The effect of missing detection and improving detection efficiency
Active Publication Date: 2014-10-29
NANJING UNIV OF POSTS & TELECOMM
View PDF2 Cites 10 Cited by
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
[0005] The technical problem to be solved by the present invention is: the present invention provides a Sybil attack detection method based on node cooperation, which solves the real environmental conditions that cannot be oriented to the operation of wireless sensor networks in the prior art, and does not consider the node transmission power, resulting in The problem of missed detection and false detection of Sybil nodes
Method used
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
View moreImage
Smart Image Click on the blue labels to locate them in the text.
Smart ImageViewing Examples
Examples
Experimental program
Comparison scheme
Effect test
Embodiment Construction
[0040] The technical scheme of the present invention is described in detail below in conjunction with accompanying drawing:
[0041] 1. Analysis of RSSI secondary difference in power controllable WSN
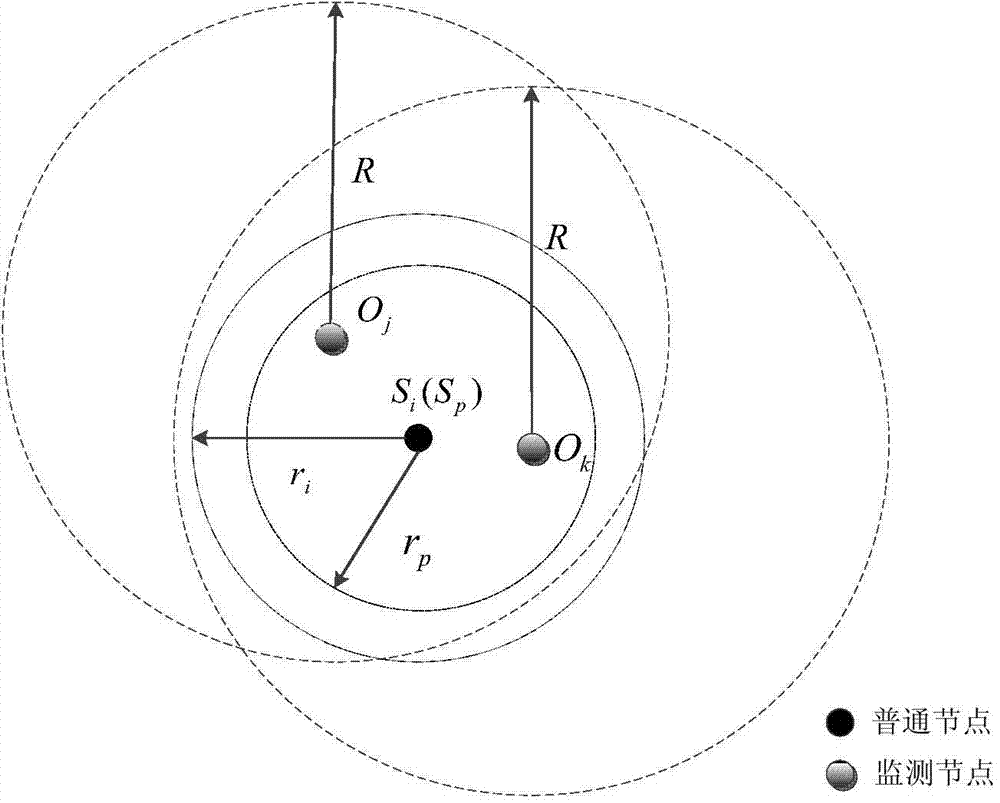
[0042] Suppose S is a malicious node, S i and S p is two Sybil nodes forged by it, and their respective neighbor monitoring node sets are respectively and o j and O k is S i and S p The public monitoring node of O j , Sybil attack such as figure 1 shown. When the malicious node S uses S i When the identity broadcasts the Hello neighbor message to the neighbor node, based on the large-scale transmission model O j The calculated RSSI value is:
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More PUM
 Login to View More
Login to View More Abstract
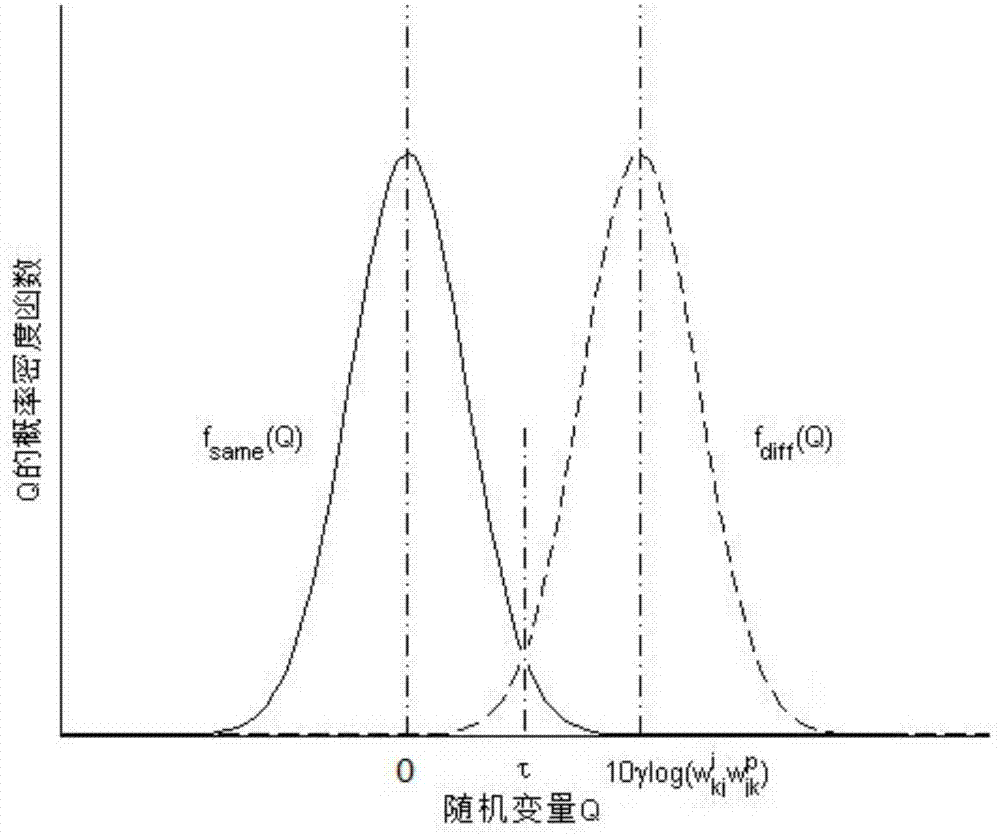
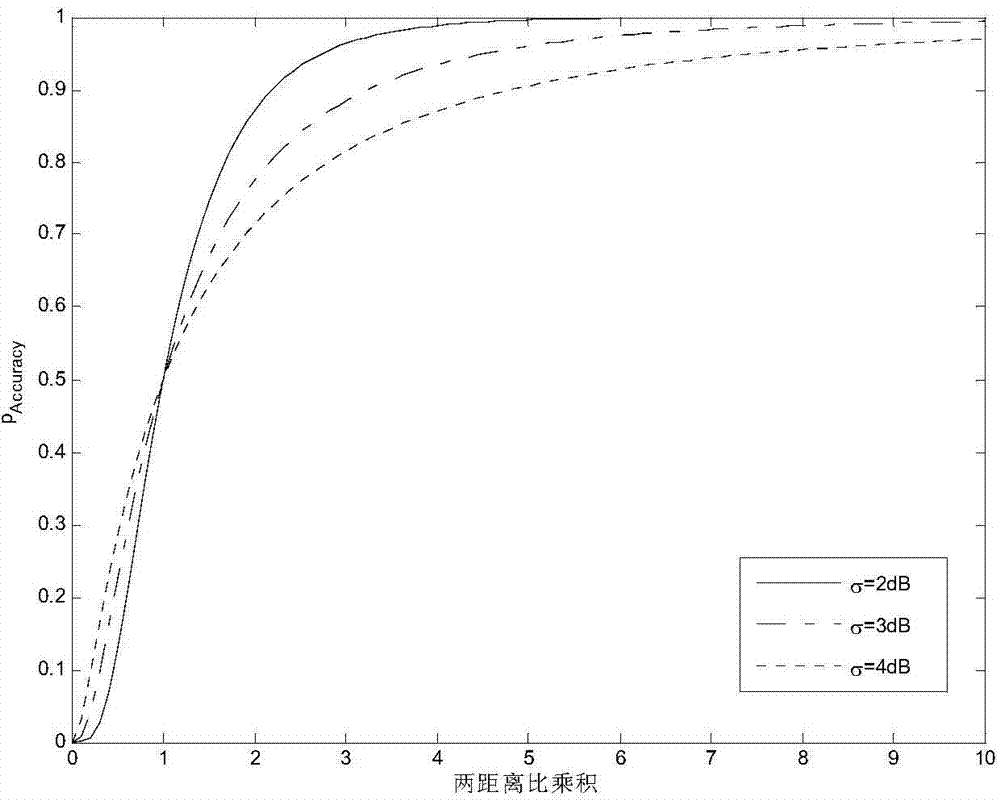
The invention discloses a node collaboration based Sybil attack detection method in a power controllable WSN (Wireless Sensor Network) and belongs to the network security technical field. The node collaboration based Sybil attack detection method comprises facing the real network environment which comprises the path loss and shadow fading and is a large scale propagation model to analyze a secondary difference value of an RSSI (Received Signal Strength Indicator) and providing a Sybil node identification algorithm according to the characteristic that the secondary difference value of the RSSI is not affected by changes of the node transmission power, wherein the Sybil node identification algorithm distinguishes whether two nodes are two Sybil identities which are forged through a malicious node or not through the mutual collaboration of public monitoring nodes of the two ordinary nodes. According to the node collaboration based Sybil attack detection method, the characteristics of the secondary difference value of the RSSI and the monitoring node cooperation scheme are combined and accordingly the detection efficiency of Sybil attacks in the power controllable WSN is improved and the network life cycle can be extended.
Description
technical field [0001] The invention belongs to the cross-technical application fields of wireless sensor networks and information security, and in particular relates to a Sybil attack detection method based on node cooperation. Background technique [0002] Sybil attack refers to an attack method in which an attacker makes a legitimate node a malicious node by capturing sensor nodes or listening to a large number of communication messages, and then appears in front of other nodes in the network with multiple false identities. Among them, the node identity forged by malicious nodes is called Sybil node. Early Sybil attacks appeared in P2P networks. Due to the lack of trusted authority centers in distributed networks, a legitimate physical node is easily captured by Sybil attacks, and the reputation system in P2P networks is destroyed by forging peer node identities. , and similar problems also exist in wireless sensor networks. Sybil attack is one of the most important int...
Claims
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More Application Information
Patent Timeline
 Login to View More
Login to View More IPC IPC(8): H04W12/12
CPCY02D30/70
Inventor 程春玲钱雅秋
Owner NANJING UNIV OF POSTS & TELECOMM