cascade authentication method based on cas
An authentication method and cascading technology, applied in the information field, can solve problems such as the inability to achieve cross-deployment unit SSO penetration, and the inability to support the application integration of large group companies, so as to achieve the effect of improving the application experience
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
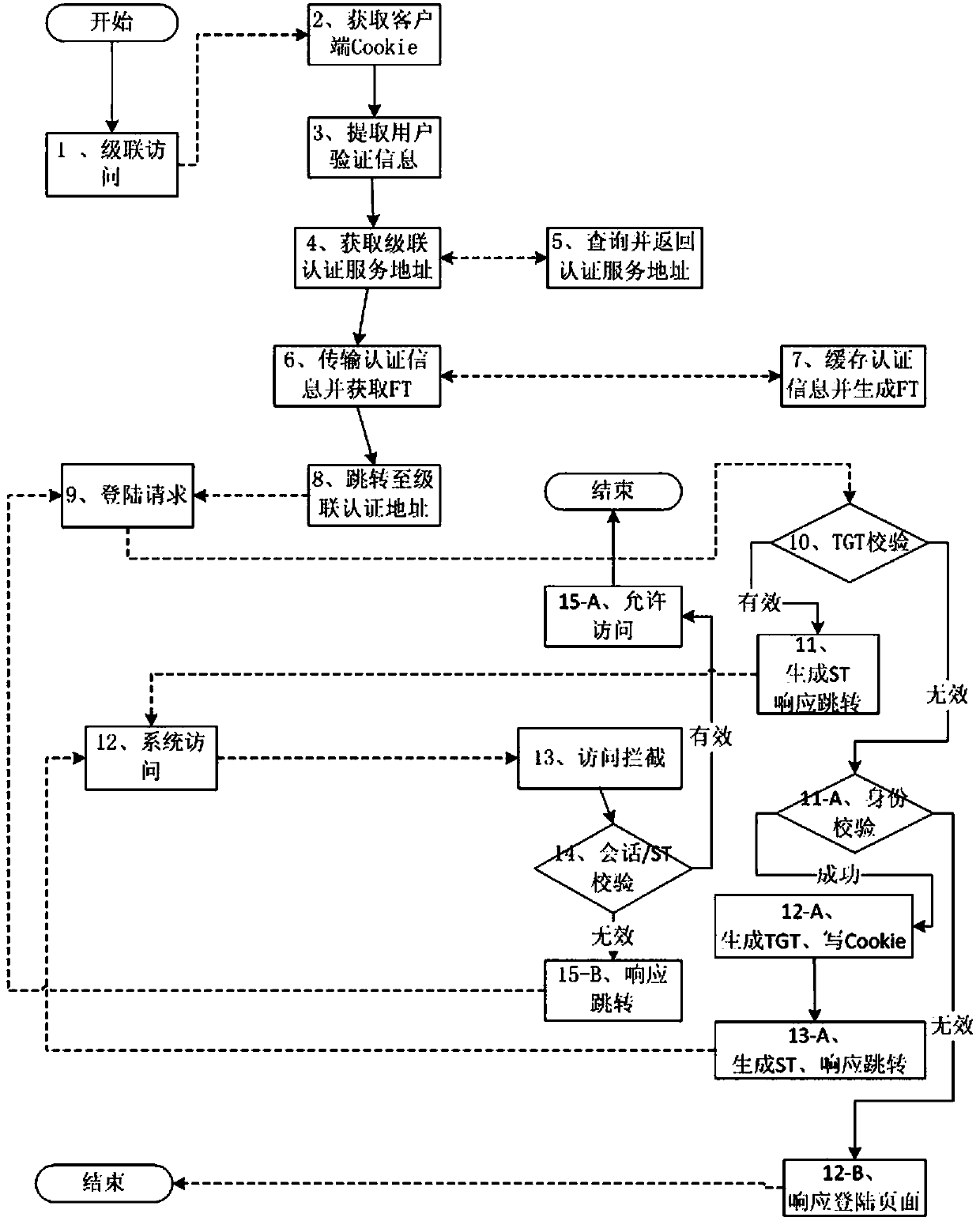
[0054] Based on the CAS cascading authentication method, when the user logs in for the first time, each cross-domain authentication service will authenticate the user once, and if the authentication is successful, a TGT will be assigned to the client. As long as the user client has the TGT of each authentication domain, it will Cross-domain access between different deployment units can be realized; specifically, the following steps are included:
[0055] 1) In the CAS client component, a Servlet program is newly developed to return the cascading target authentication service address to the requester;
[0056] 2) On the CAS server, a new cascading handshake interface based on the http protocol is newly developed to receive the input of user login credentials, generate an FT, then cache the user login credentials with FT as the logo, and finally return the FT field string to the caller;
[0057] 3) When the CAS server processes the verification of user login credentials, if the ...
Embodiment 2
[0068] This embodiment is further optimized on the basis of the above embodiments. Further, in order to better realize the present invention, in the step 8), the cascade controller forwards the user request to the integrated level of the cascade target business system When connecting to the target authentication service, the user client receives a jump response, the jump address is the authentication address of the cascading target authentication service, and initiates a login authentication request to the cascading target authentication service, and the cascading target authentication service will receive the user The cascade authentication request of the client, when processing the request, first parses from the user client whether it has a valid TGT, if it is valid, generates an ST for the user client, and then forwards the request to the "system access process"; if invalid, returns Proceed to step 9).
[0069] Extend the new processing process and effectively combine with ...
Embodiment 3
[0071] This embodiment is further optimized on the basis of Embodiment 1. Further, in order to better realize the present invention, in the step 9), verifying the user login credential includes the following steps:
[0072] 9.1), authentication is successful:
[0073] 9.1.1), generate TGT, write Cookie: the cascade authentication identity verification is successful, enter the standard CAS function process, that is, generate TGT for the user client, and write the TGT into the CAS client Cookie;
[0074] 9.1.2), generate ST, response jump: After the TGT is generated successfully, then generate ST for the user according to the TGT, and then jump the user request to the "system access process";
[0075] 9.2) Respond to the login page if the identity verification is invalid: In the case of cascade authentication failure, a login page will be returned to the user client, requiring the user to log in.
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com