Rapid ciphertext retrieval method and system capable of resisting statistical analysis attack
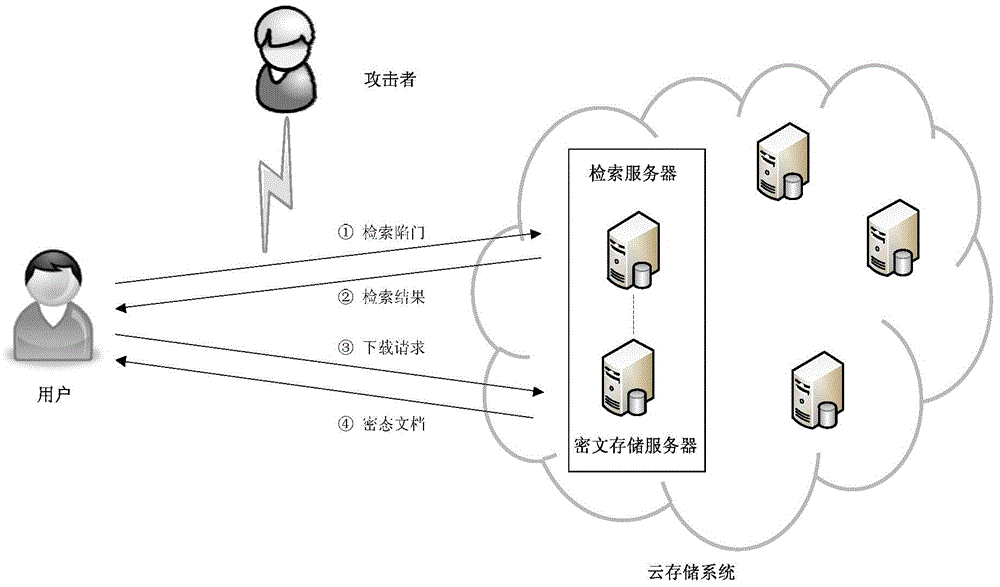
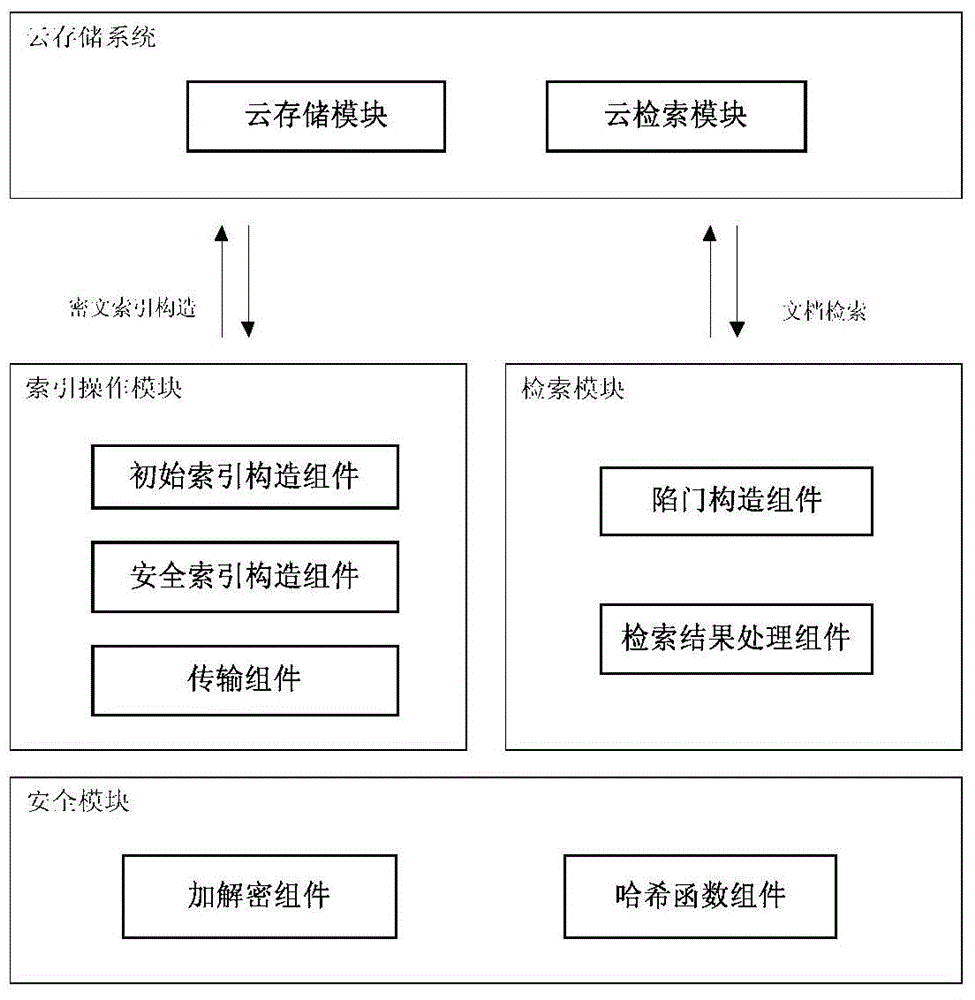
A statistical analysis, ciphertext technology, applied in the field of information security, can solve the problem of sensitive information leakage, and achieve the effect of low communication cost, fewer interactions, and high security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
[0085] In this embodiment, the client side selects four hash functions, uses a 20-bit bit string to represent the document index, and has five documents to be uploaded.
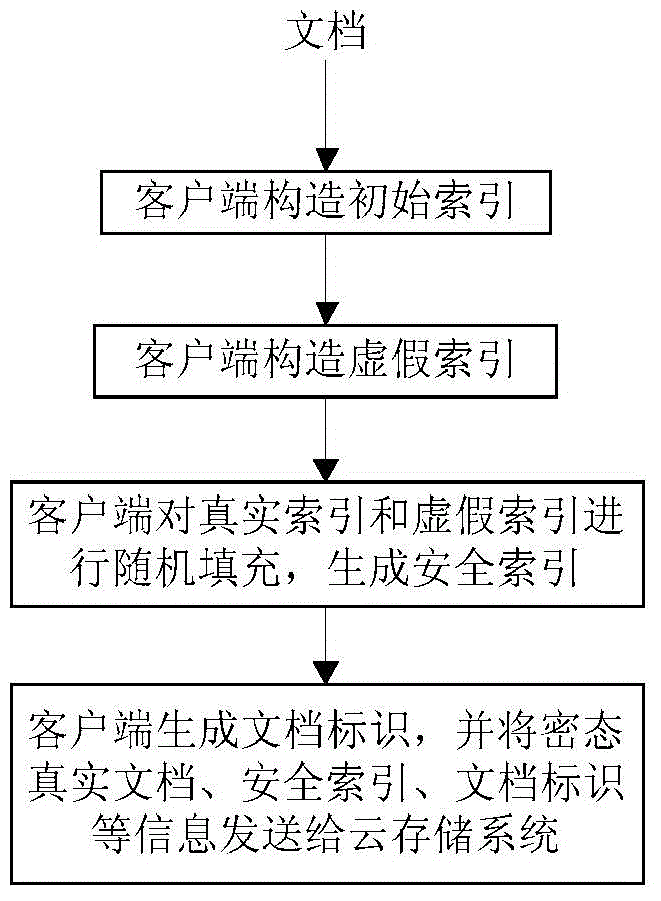
[0086] The flow process of this embodiment is as follows:
[0087] 1. The client generates the key and related parameters for the aes256 encryption algorithm, and selects 4 mutually independent hash functions h 1 ,..., h 4 , where h i :{0,1} * →[1,20], i∈[1,4].
[0088] 2. The keyword lists of each document in document set D are:
[0089] D. 1 ={"china","computation","university","science"}
[0090] D. 2 ={"china","computation","university"}
[0091] D. 3 ={"china","computation"}
[0092] D. 4 ={"china","university"}
[0093] D. 5 ={"china","science"}
[0094] to document D 1 The keywords in the list do the following:
[0095] 1) Calculate h 1 ("china")=2,h 2 ("china")=9,
[0096] h 3 ("china")=14,h 4 ("china") = 20;
[0097] 2) Calculate h 1 ("computation")=1,h 2 ("computation")=6,
...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More