Electric power trusted computing cryptographic module for PCI/PCI-E interface
A PCI-E, trusted computing technology, applied in the trust model of public key infrastructure, public key for secure communication, electrical components, etc. advanced questions
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] The specific embodiments of the present invention will be further described in detail below in conjunction with the accompanying drawings.
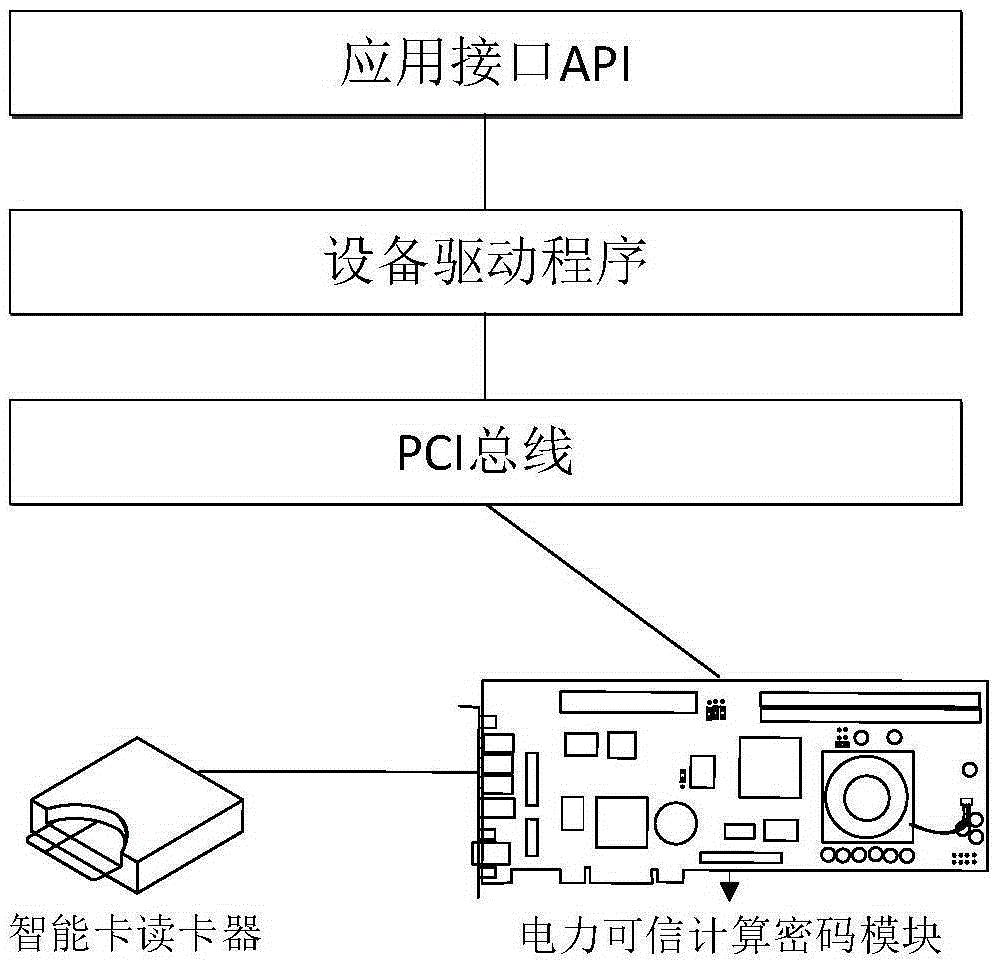
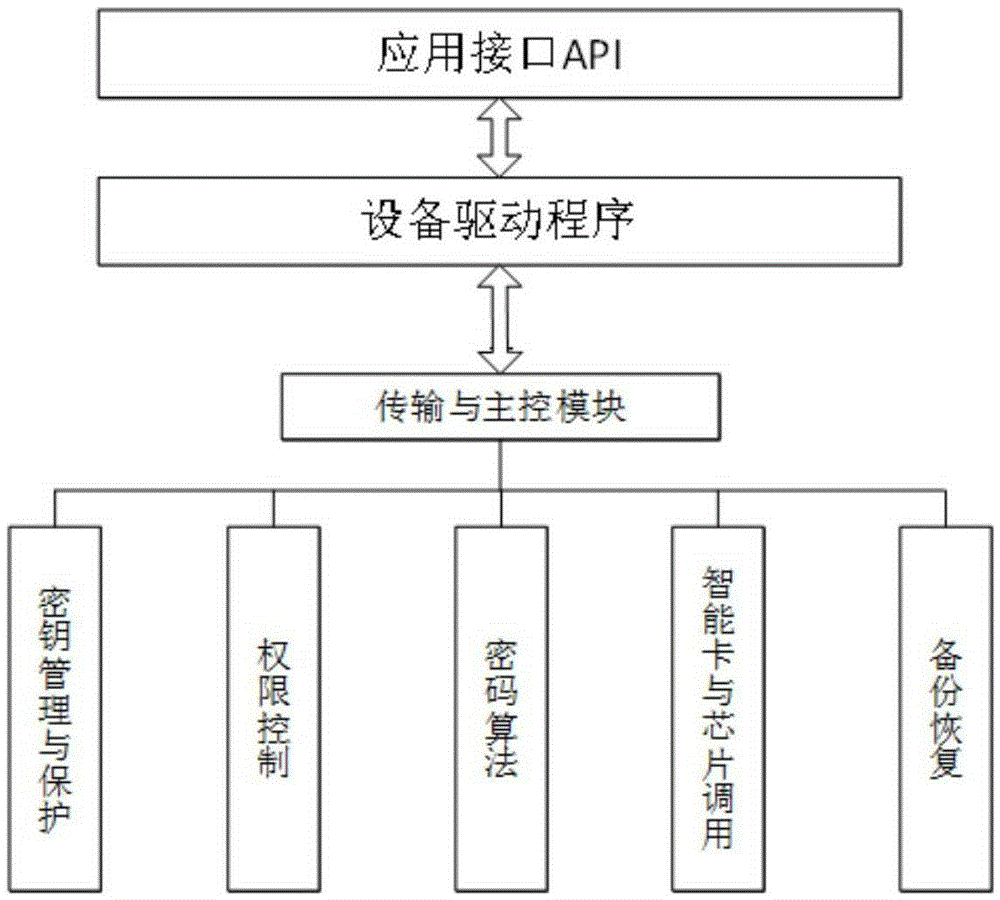
[0030] The technical solution provided by the present invention is a PCI / PCI-E interface power trusted computing cryptographic module where the system layered schematic diagram of the module is shown figure 1 Shown:
[0031] (1) Application interface API
[0032] This module invokes the hardware device of the underlying power trusted computing cryptographic module through the driver program, and provides basic cryptographic services to the cryptographic application system through the upper-layer general cryptographic service interface or directly.
[0033] (2) Device driver
[0034] Provide a communication interface between the power trusted computing cryptographic module hardware and the cryptographic device application interface, and realize the cryptographic calling function of the hardware by the application interface.
[00...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More