Method and device for secret key generation and corresponding decryption
A technology for generating keys and user equipment, which is applied in the computer field and can solve problems such as key security at the user equipment end
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
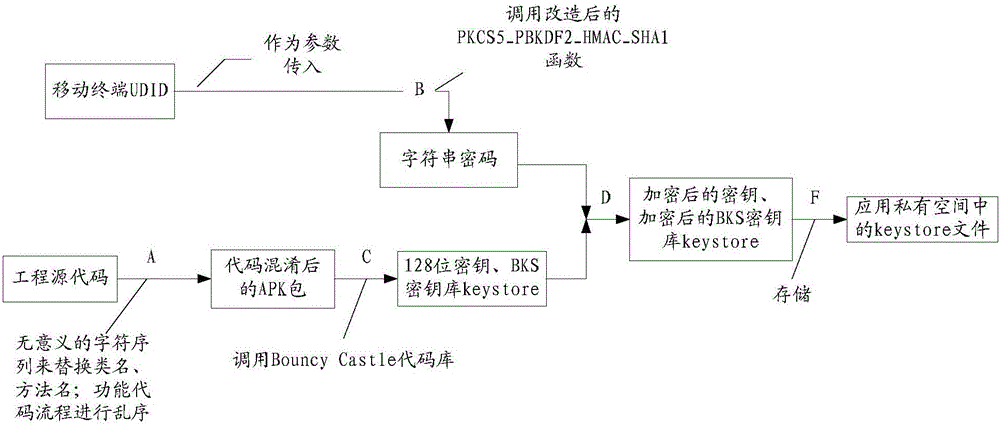
[0038] The application will be described in further detail below in conjunction with the accompanying drawings.
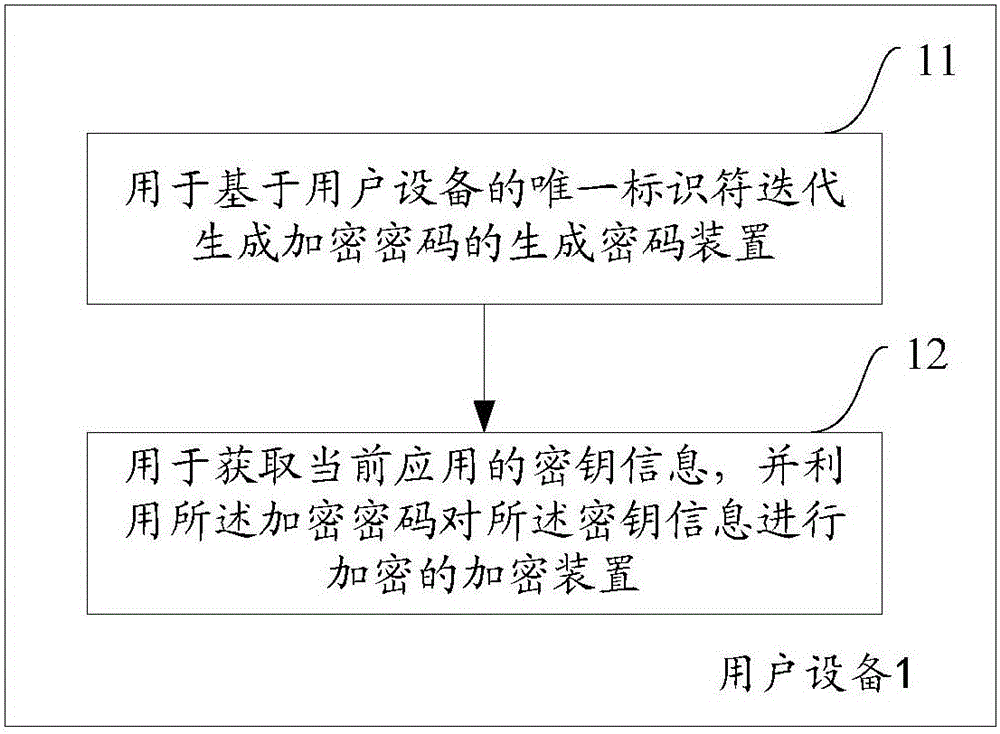
[0039] figure 1 A schematic structural diagram of a user equipment for generating a key according to one aspect of the present application is shown. The user equipment 1 includes a password generation device 11 and an encryption device 12, wherein the password generation device 11 iteratively generates an encryption password based on the unique identifier of the user equipment; the encryption device 12 obtains the key information of the current application, and uses the encryption password The key information is encrypted.
[0040] Here, the user equipment 1 includes but is not limited to any mobile electronic product that can interact with the user through a touch panel, such as a smart phone, a PDA, etc., and the mobile electronic product can use any operating system, such as android operating system, iOS operating system, etc. Preferably, the user equipment 1...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More