Network attack analysis method
A network attack and analysis method technology, applied in the field of network attack analysis, can solve the problems of security management personnel spending processing useless information, intuitively obtaining abnormal behavior, and difficult network attack conditions.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0032] Specific embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings.
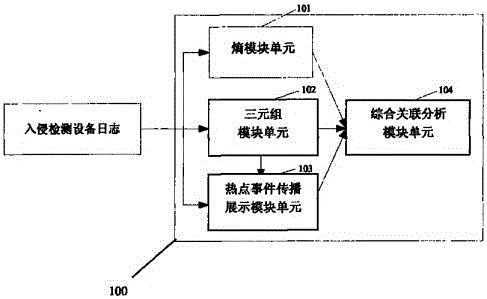
[0033] figure 1 is a schematic structural diagram of a network attack analysis system according to an embodiment of the present invention. The network attack analysis system 100 according to this embodiment includes an entropy module unit 101 , a triple module unit 102 , a hot event propagation display module unit 103 , and a comprehensive correlation analysis module unit 104 .
[0034] The entropy module unit 101 is used to read the intrusion detection device log within a specified time period, then calculate the entropy distribution value of the source address and the destination address of the intrusion detection device log, determine whether there is a large-scale network attack event, and then provide comprehensive correlation analysis The module unit 104 outputs the judgment result of the address distribution status of the current netwo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More