Method and device for data security encryption based on alliance block chain
A blockchain and data technology, applied in electrical components, transmission systems, etc., can solve problems such as data leakage and data security hidden dangers in data storage networks, and achieve the effect of transparent access, security protection, and high degree of transparency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
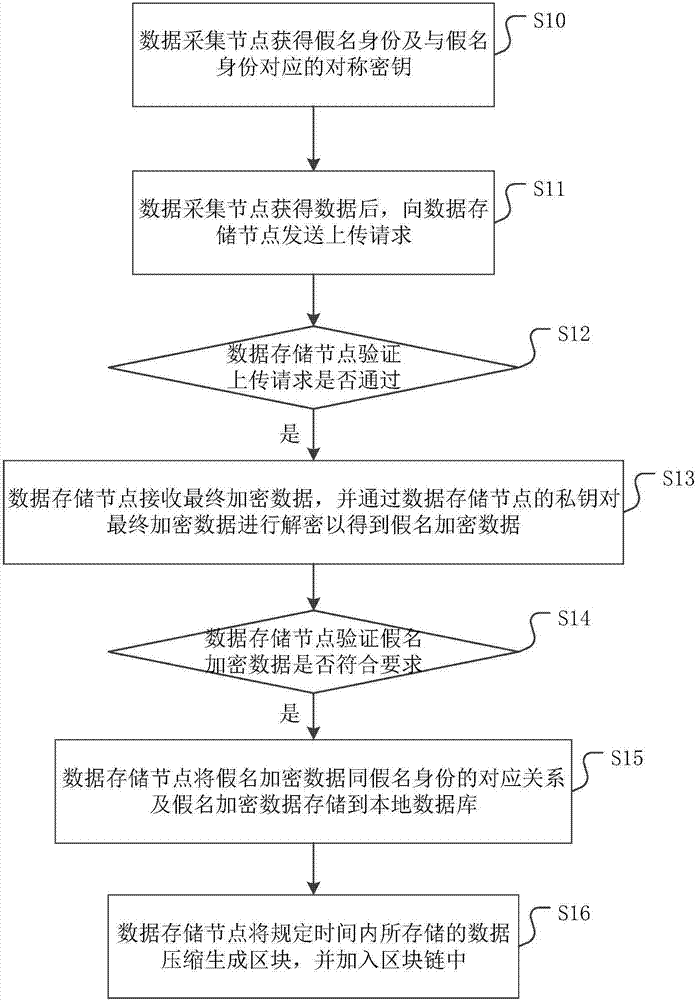
[0038] figure 1 It is a flow chart of a data security encryption method based on consortium blockchain provided by an embodiment of the present invention. Please refer to figure 1 , the specific steps of the data security encryption method based on the alliance blockchain include:
[0039] Step S10: the data collection node obtains the pseudonym identity and the symmetric key corresponding to the pseudonym identity.
[0040] The purpose of this step is that the data acquisition node uses a pseudonym to hide its real node identity, and uses a pseudonym to communicate with other nodes. It can be understood that since the nodes communicating with the data collection node cannot know the true identity of the data collection node, the concealment and security of the data collection node are further improved, and the malicious attacks of the data node by other nodes are reduced. This may lead to data loss, leakage and forgery.
[0041] In addition, data acquisition nodes can obt...
Embodiment 2
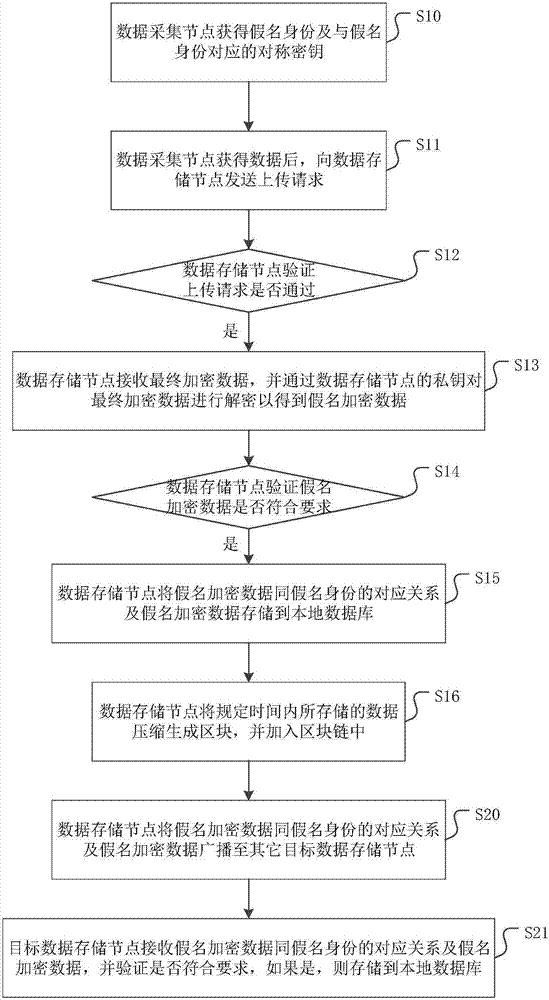
[0059] figure 2 It is a flow chart of another data security encryption method based on consortium blockchain provided by the embodiment of the present invention. figure 2 In steps S10-S16 and figure 1 Same, no more details here.
[0060] like figure 2 As shown, as a preferred embodiment, it also includes:
[0061] Step S20: the data storage node broadcasts the correspondence between the pseudonym encrypted data and the pseudonym identity and the pseudonym encrypted data to other target data storage nodes.
[0062] The purpose of the data storage node broadcasting the data stored by itself to other target data storage nodes is that other target data storage nodes can also obtain the data in the data storage node, which ensures the transparency of data sharing. It is understandable that when the data storage node fails or is attacked and the data is lost, the user can still obtain the data from other target data storage nodes, which ensures that the stored data is not eas...
Embodiment 3
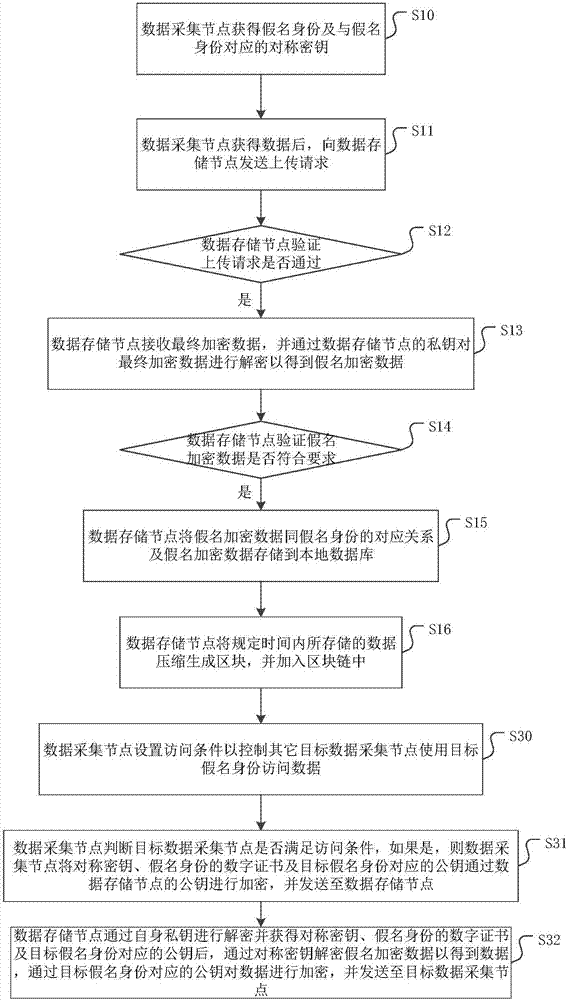
[0067] Corresponding to the data collection node storing data in the data storage node, this embodiment further provides a method for the target data collection node to access the data of the data collection node. For specific steps, please refer to image 3 .
[0068] image 3 It is a flow chart of a data access method corresponding to a data security encryption method based on consortium blockchain provided by an embodiment of the present invention. like image 3 As shown, on the basis of the foregoing embodiments, it also includes:
[0069] Step S30: the data collection node sets access conditions to control other target data collection nodes to use the target pseudonym to access data.
[0070] In this step, the access conditions may include: the target pseudonym identity is within the scope of the pseudonym identity set by the data collection node, the data accessed by the target pseudonym identity is within the data sharing range set by the data collection node, and th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com